In 2023, the worldwide common price of a knowledge breach reached $4.45 million. Past the rapid monetary loss, there are long-term penalties like diminished buyer belief, weakened model worth, and derailed enterprise operations.
In a world the place the frequency and price of information breaches are skyrocketing, organizations are coming face-to-face with a harsh actuality: conventional cybersecurity measures won’t be slicing it anymore.
In opposition to this backdrop, companies should discover methods to strengthen their measures to safeguard treasured knowledge and significant belongings. On the coronary heart of this shift lies a key technique: steady monitoring.
Understanding Steady Safety Monitoring in Cybersecurity
Steady monitoring is a dynamic strategy that encompasses a number of methods to fulfil a multi-layered protection technique. These methods can embrace:
In contrast to point-in-time assessments, that are analogous to taking a photograph of your safety posture, steady monitoring is sort of a 24/7 stay stream. It proactively scouts for vulnerabilities, irregularities, misconfigurations, and potential threats, making certain swift detection and response.
Steady Safety Monitoring for Net Purposes
Defending enterprise purposes needs to be a central element of any efficient cybersecurity technique. Not solely are they a tempting goal for cybercriminals, however they’re additionally more and more troublesome to guard. In line with a latest report, primarily based on evaluation of three.5 million enterprise belongings, the overwhelming majority (74%) of internet-exposed net apps containing private identifiable info (PII) are weak to a cyberattack.
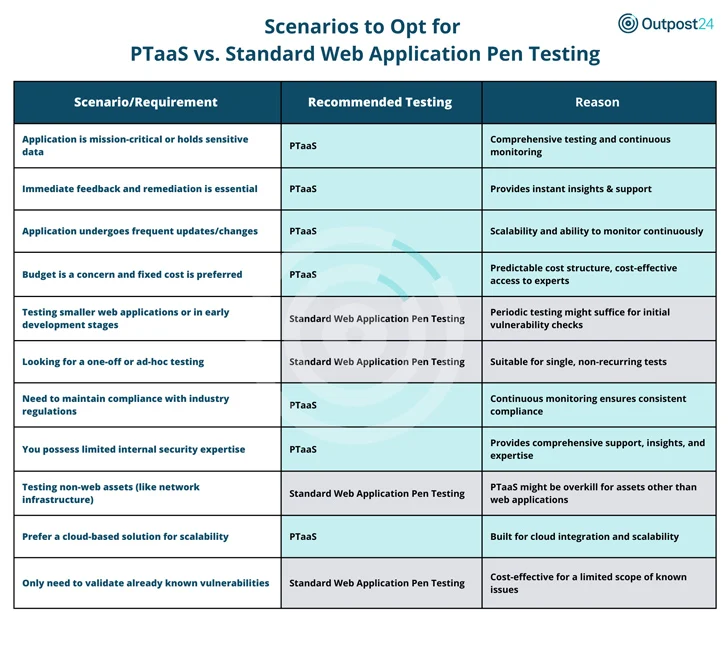
With regards to defending their net software, organizations typically grapple with a important selection: a pen testing as a service (PTaaS) resolution or the usual (periodic or ad-hoc) pen take a look at. The selection boils all the way down to your group’s particular wants. Each instruments have their deserves; it is about aligning the software with the duty at hand, making certain you are all the time forward within the cybersecurity recreation.
The Advantages of PTaaS
- In environments the place apps are essential or deal with delicate knowledge a PTaaS resolution and its steady monitoring is a non-negotiable. It presents ongoing safety towards evolving vulnerabilities.
- On the funds entrance, PTaaS presents a predictable price mannequin, making it a cheap path to high-level safety experience.
- For organizations restricted in safety manpower, PTaaS fills the hole, offering strong help and direct entry to safety consultants.
The Advantages of the Commonplace Pen Testing
- For newer or smaller net apps, occasional checks is likely to be sufficient, which is the place the usual pen take a look at steps in.
- Have a one-time want, like a selected safety verification? commonplace pen testing is your finest wager. It is also extra suited to duties centered on non-web belongings, like community infrastructure.
- When you’re strictly seeking to validate identified vulnerabilities, commonplace pen testing presents a centered, cost-effective resolution.
The Broader Panorama of Steady Monitoring
Outpost24 identifies safety gaps throughout your whole assault floor and helps you prioritize vulnerabilities to optimize your cybersecurity posture and scale back publicity.
- Outscan NX (RBVM): Vulnerability administration with real-world menace intelligence to focus remediation and scale back enterprise threat.
- SWAT (PTaaS): Handbook testing and automatic scanning with entry to safety consultants to your agile growth cycles.
- Sweepatic (EASM): Assault floor discovery and monitoring in real-time with actionable insights.
- Menace Compass (Cyber Menace Intelligence): Focused and actionable intelligence for quicker menace detection and incident response.
The digital age calls for a rethink of our cybersecurity paradigms. The rising prices and dangers related to knowledge breaches make it clear: steady safety monitoring is not simply an possibility, it is a necessity. With the above options, Outpost24 presents a strong toolkit to navigate this new cybersecurity panorama.