
Toyota Monetary Providers (TFS) has confirmed that it detected unauthorized entry on a few of its programs in Europe and Africa after Medusa ransomware claimed an assault on the corporate.
Toyota Monetary Providers, a subsidiary of Toyota Motor Company, is a worldwide entity with a presence in 90% of the markets the place Toyota sells its automobiles, offering auto financing to its prospects.
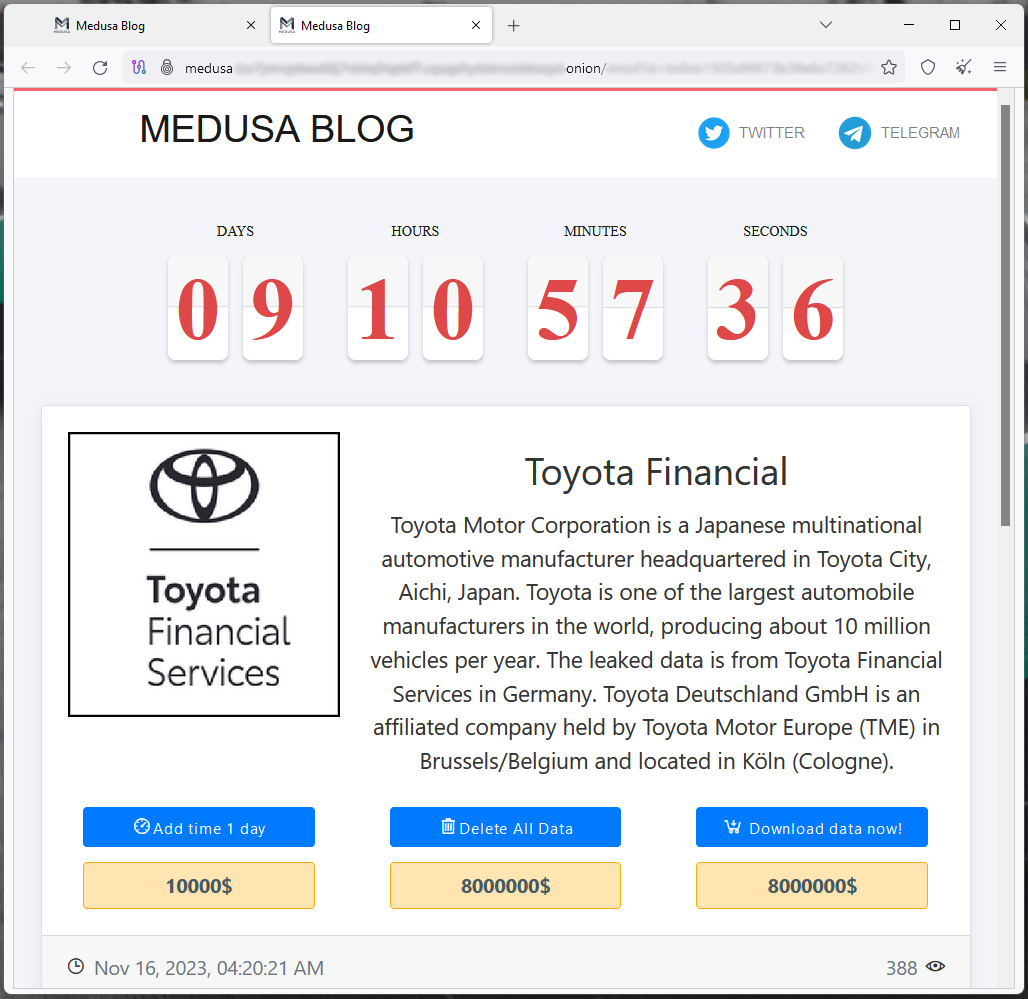
Earlier as we speak, the Medusa ransomware gang listed TFS to its information leak web site on the darkish net, demanding a fee of $8,000,000 to delete information allegedly stolen from the Japanese firm.
The risk actors gave Toyota 10 days to reply, with the choice to increase the deadline for $10,000 per day.
Whereas Toyota Finance didn’t verify if information was stolen within the assault, the risk actors declare to have exfiltrated information and threaten with an information leak if a ransom isn’t paid.
To show the intrusion, the hackers printed pattern information that features monetary paperwork, spreadsheets, buy invoices, hashed account passwords, cleartext consumer IDs and passwords, agreements, passport scans, inside group charts, monetary efficiency studies, employees electronic mail addresses, and extra.
Medusa additionally offers a .TXT file with the file tree construction of all the info they declare to have stolen from Toyota’s programs.
Many of the paperwork are in German, indicating that the hackers managed to entry programs serving Toyota’s operations in Central Europe.
BleepingComputer reached out to the Japanese automaker for a touch upon the leaked information and an organization spokesperson supplied the next assertion:
“Toyota Monetary Providers Europe & Africa not too long ago recognized unauthorized exercise on programs in a restricted variety of its places.”
“We took sure programs offline to analyze this exercise and to scale back threat and have additionally begun working with regulation enforcement.”
“As of now, this incident is restricted to Toyota Monetary Providers Europe & Africa.”
Concerning the standing of the impacted programs and their estimated return to regular operations, the spokesperson informed us that the method of bringing programs again on-line is already underway in most nations.
One other Citrix Bleed breach?
Earlier as we speak, following Medusa’s disclosure of TFS as their sufferer, safety analyst Kevin Beaumont highlighted that the agency’s German workplace had an internet-exposed Citrix Gateway endpoint which had not been up to date since August 2023, indicating that it was susceptible to the essential Citrix Bleed (CVE-2023-4966) safety difficulty.
A couple of days again, it was confirmed that Lockbit ransomware operatives had been utilizing publicly obtainable exploits for Citrix Bleed to obtain breaches in opposition to the Industrial and Business Financial institution of China (ICBC), DP World, Allen & Overy, and Boeing.
It’s doable that different ransomware teams have began to use Citrix Bleed, profiting from the huge assault floor estimated to rely a number of thousand endpoints.


