
A hacker claims to have breached Condé Nast and leaked an alleged WIRED database containing greater than 2.3 million subscriber data, whereas additionally warning that they plan to launch as much as 40 million extra data for different Condé Nast properties.
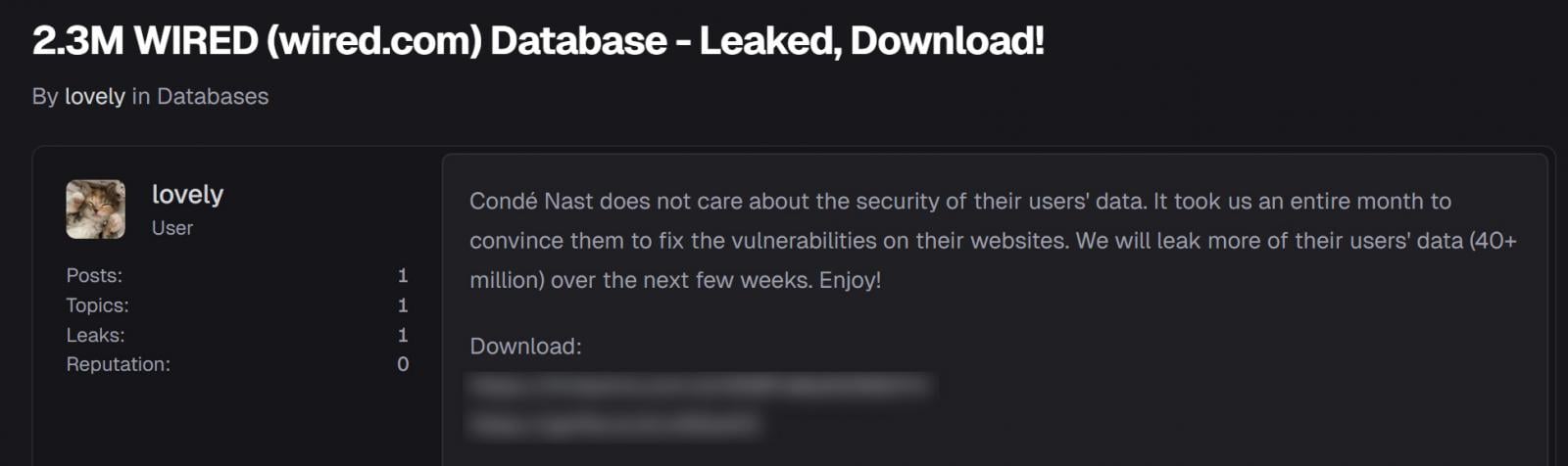
On December 20, a risk actor utilizing the identify “Pretty” leaked the database on a hacking discussion board, providing entry for about $2.30 within the web site’s credit system. Within the put up, Pretty accused Condé Nast of ignoring vulnerability experiences and claimed the corporate didn’t take safety severely.
“Condé Nast doesn’t care concerning the safety of their customers’ knowledge. It took us a complete month to persuade them to repair the vulnerabilities on their web sites,” reads a put up on a hacking discussion board.
“We’ll leak extra of their customers’ knowledge (40+ million) over the subsequent few weeks. Get pleasure from!”
Supply: BleepingComputer
The identical particular person later leaked the info on different hacking boards, the place customers additionally needed to spend discussion board credit to disclose the password to the archive containing the info.
Pretty additionally shared document counts for different Condé Nast properties they declare to have stolen knowledge, together with, primarily based on the abbreviations used, The New Yorker, Epicurious, SELF, Vogue, Attract, Vainness Honest, Glamour, Males’s Journal, Architectural Digest, Golf Digest, Teen Vogue, Fashion.com, and Condé Nast Traveler.
Whereas Condé Nast has not but confirmed it was breached, BleepingComputer analyzed the leaked database and was capable of validate twenty of the data as official WIRED subscribers.
The dataset incorporates 2,366,576 whole data and a couple of,366,574 distinctive e-mail addresses, with timestamps starting from April 26, 1996, to September 9, 2025.
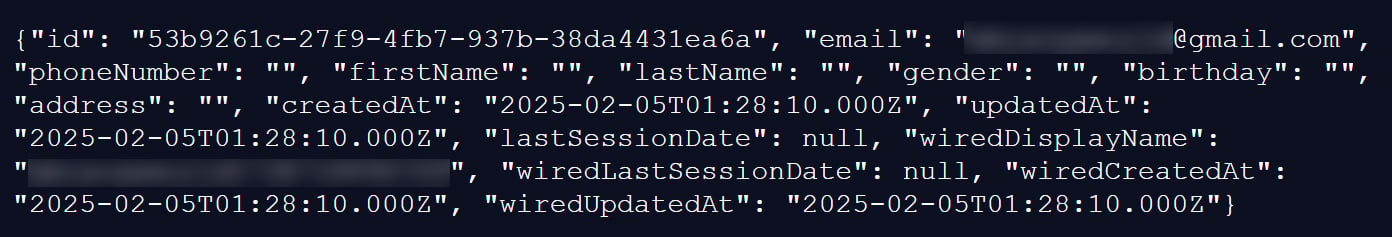
Every document features a subscriber’s distinctive inner ID, an e-mail deal with, and non-obligatory knowledge, similar to first and final identify, cellphone quantity, bodily deal with, gender, and birthday. Many of those fields are empty.
The data additionally embrace account creation and replace timestamps, final session data, and WIRED-specific fields similar to a show username and WIRED account creation and replace dates.
Supply: BleepingComputer
Whereas lots of the data fields are empty, some embrace extra private particulars.
Roughly 284,196 data (12.01%) embrace each a primary and final identify, 194,361 data (8.21%) embrace a bodily deal with, 67,223 data (2.84%) embrace a birthday, and 32,438 data (1.37%) embrace a cellphone quantity.
A a lot smaller subset consists of extra full profiles, with 1,529 data (0.06%) containing a full identify, birthday, cellphone quantity, deal with, and gender.
Alon Gal, co-founder and CTO of Hudson Rock, additionally verified the data utilizing infostealer logs containing beforehand compromised credentials.
“Our researchers recognized official subscriber credentials for wired.com inside international infostealer an infection logs,” reads an article on Infostealers.com.
“By matching these compromised credentials towards the data within the leaked database, we’ve definitively confirmed the authenticity of the dataset with none interplay with the sufferer group.”
The leaked database has since been added to Have I Been Pwned, permitting customers to verify whether or not their e-mail addresses have been uncovered by the info leak.
Claiming to be a safety researcher
Earlier than the leak, Pretty reportedly claimed to be a safety researcher who contacted Dissent Doe of DataBreaches.internet for assist in responsibly disclosing vulnerabilities to Condé Nast.
Based on DataBreaches.internet, the person contacted them in late November in search of assist reaching Condé Nast’s safety crew relating to vulnerabilities that allegedly allowed attackers to view and modify person account data.
The particular person initially mentioned they’d downloaded solely a small variety of data to offer proof to Condé Nast, together with data verified as belonging to DataBreaches.internet and a WIRED worker.
Nonetheless, after receiving no response from Condé Nast, the particular person later instructed Dissent Doe they’d downloaded the whole database and have been threatening to leak it.
Dissent Doe concluded that she had been misled and described the incident as a case the place they’d been performed by a risk actor who downloaded and leaked stolen knowledge relatively than pursuing accountable disclosure.
“As for ‘Pretty,’ they performed me. Condé Nast ought to by no means pay them a dime, and nobody else ought to ever, as their phrase clearly can’t be trusted,” admitted DataBreaches.internet.
BleepingComputer contacted Condé Nast with questions concerning the incident, however has not obtained a response right now.
Damaged IAM is not simply an IT downside – the impression ripples throughout your complete enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with trendy calls for, examples of what “good” IAM appears to be like like, and a easy guidelines for constructing a scalable technique.




