
Legislation enforcement businesses arrested a malware developer linked with the Ragnar Locker ransomware gang and seized the group’s darkish web pages in a joint worldwide operation.
The Ragnar Locker ransomware gang is believed to have carried out assaults towards 168 worldwide firms globally since 2020.
“The ‘key goal’ of this malicious ransomware pressure was arrested in Paris, France, on 16 October, and his dwelling in Czechia was searched. 5 suspects have been interviewed in Spain and Latvia within the following days,” Europol mentioned right now.
“On the finish of the motion week, the primary perpetrator, suspected of being a developer of the Ragnar group, has been introduced in entrance of the inspecting magistrates of the Paris Judicial Court docket.
Eurojust opened the case in Might 2021 on the French authorities’ request. The company carried out 5 coordination conferences to facilitate judicial collaboration amongst authorities concerned within the investigation.
This joint operation between authorities from France, the Czech Republic, Germany, Italy, Latvia, the Netherlands, Spain, Sweden, Japan, Canada, and america marks the third motion towards the identical ransomware gang.
In September 2021, coordinated efforts involving French, Ukrainian, and US authorities led to the arrest of two suspects in Ukraine.
Subsequently, in October 2022, one other suspect was apprehended in Canada by way of a joint operation carried out by French, Canadian, and US legislation enforcement businesses.
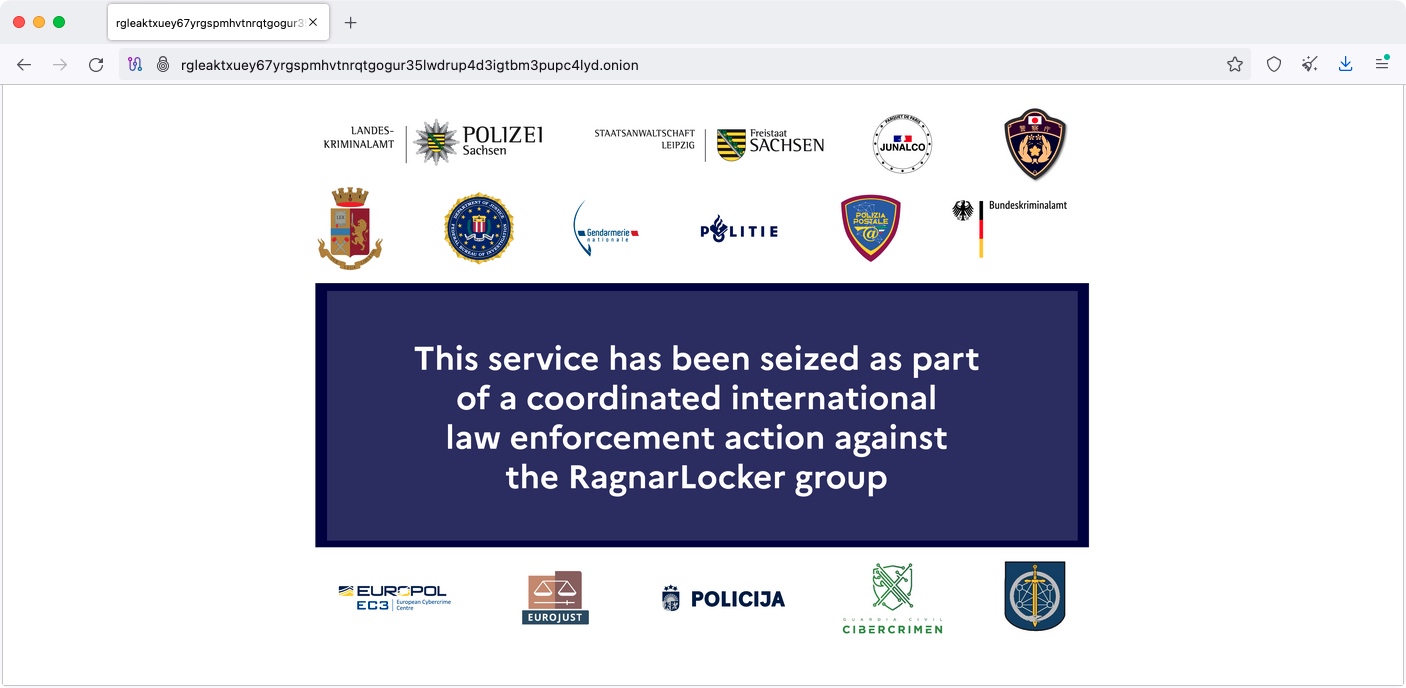
Throughout the coordinated operation, legislation enforcement brokers additionally seized cryptocurrency property and took down the Ragnar Locker’s Tor negotiation and information leak websites on Thursday.
“Moreover, 9 servers have been taken down; 5 within the Netherlands, two in Germany and two in Sweden,” Europol mentioned.
“This service has been seized as a part of a coordinated legislation enforcement motion towards the Ragnar Locker group,” a banner displayed on Ragnar Locker’s information leak website reads.
Alongside the profitable seizure of Ragnar Locker’s infrastructure, the Ukrainian Cyber Alliance (UCA) hacked the Trigona Ransomware operation, efficiently retrieving information and wiping the cybercriminals’ servers.
The Ragnar Locker (also referred to as Ragnar_Locker and RagnarLocker) ransomware operation surfaced in late December 2019 when it began concentrating on enterprise victims worldwide.
In distinction to many fashionable ransomware gangs, Ragnar Locker didn’t function as a Ransomware-as-a-Service, the place associates are recruited to breach targets’ networks and deploy the ransomware in change for a share of the income.
As a substitute, Ragnar Locker operated semi-private, as they did not actively recruit associates, selecting to collaborate with exterior penetration testers to breach networks.
Its listing of earlier victims consists of distinguished entities resembling pc chip producer ADATA, aviation large Dassault Falcon, and Japanese sport maker Capcom.
In keeping with a March 2022 FBI advisory, this ransomware has been deployed on the networks of at the least 52 organizations throughout numerous essential infrastructure sectors in america since April 2020.


