
Ransomware attackers concentrating on a Fortune 100 firm within the finance sector used a brand new malware pressure, dubbed PDFSider, to ship malicious payloads on Home windows techniques.
The attackers employed social engineering of their try to realize distant entry by impersonating technical assist employees and to trick firm staff into putting in Microsoft’s Fast Help software.
Researchers at cybersecurity firm Resecurity discovered PDFSider throughout an incident response and describe it as a stealthy backdoor for long-term entry, noting that it exhibits “traits generally related to APT tradecraft.”
Legit .EXE, malicious .DLL
A Resecurity spokesperson informed BleepingComputer that PDFSider has been seen deployed in Qilin ransomware assaults. Nonetheless, the corporate’s risk searching crew notes that the backdoor is already “actively used” by a number of ransomware actors to launch their payloads.
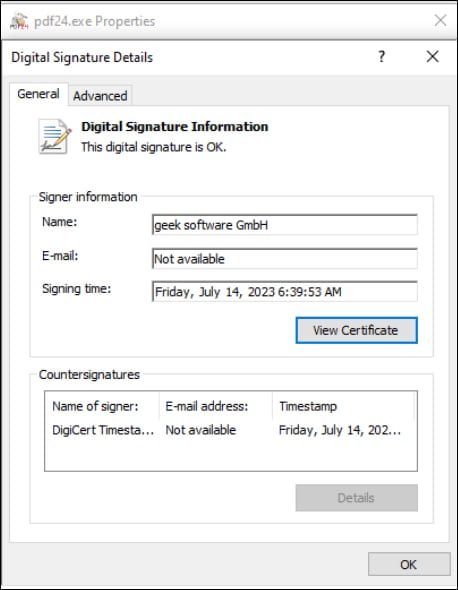
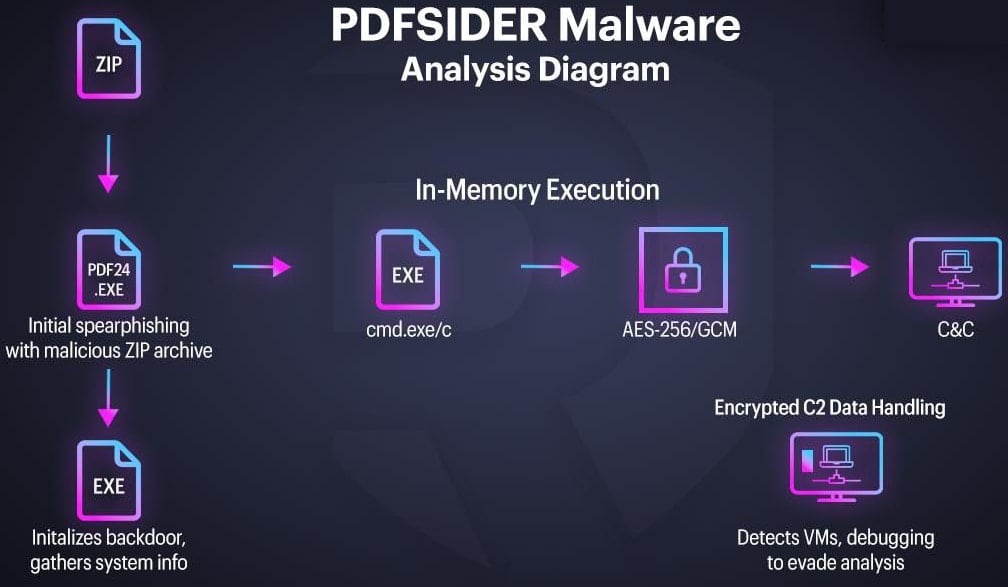
The PDFSider backdoor is delivered through spearphishing emails that carry a ZIP archive with a reputable, digitally signed executable for the PDF24 Creator software from Miron Geek Software program GmbH. Nonetheless, the package deal additionally features a malicious model of a DLL (cryptbase.dll), which the appliance requires to perform correctly.
When the executable runs, it hundreds the attacker’s DLL file, a way generally known as DLL side-loading, and supplies code execution on the system.
Supply: Resecurity
In different circumstances, the attacker makes an attempt to trick e mail recipients into launching the malicious file by utilizing decoy paperwork that look like tailor-made to the targets. In a single instance, they used a Chinese language authorities entity because the creator.
As soon as launched, the DLL runs with the rights of the executable that loaded it.
“The EXE file has a reputable signature; nevertheless, the PDF24 software program has vulnerabilities that attackers had been capable of exploit to load this malware and bypass EDR techniques successfully,” Resecurity explains.
In line with the researchers, discovering susceptible software program that may be exploited is turning into simpler for cybercriminals, because of the rise of AI-powered coding.
PDFSider hundreds straight into reminiscence, leaving minimal disk artifacts, and makes use of nameless pipes to launch instructions through CMD.
Contaminated hosts are assigned a novel identifier, and system data is collected and exfiltrated to the attacker’s VPS server over DNS (port 53).
PDFSider protects its command-and-control (C2) trade through the use of the Botan 3.0.0 cryptographic library and AES-256-GCM for encryption, decrypting incoming knowledge in reminiscence to reduce its footprint on the host.
Furthermore, the info is authenticated utilizing Authenticated Encryption with Related Information (AEAD) in GCM mode.
“This sort of cryptographic implementation is typical of distant shell malware utilized in focused assaults, the place sustaining the integrity and confidentiality of communications is vital,” Resecurity notes.
Supply: Resecurity
The malware additionally options a number of anti-analysis mechanisms, reminiscent of RAM dimension checks and debugger detection, to exit early when indicators of operating in a sandbox are detected.
Based mostly on its evaluation, Resecurity says that PDFSider is nearer to “espionage tradecraft than financially motivated malware” and is constructed as a stealthy backdoor that may preserve long-term covert entry and supply versatile distant command execution and encrypted communication.




