Guaranteeing delicate knowledge stays confidential, protected against unauthorized entry, and compliant with knowledge privateness laws is paramount. Information breaches lead to monetary and reputational harm but additionally result in authorized penalties. Subsequently, strong knowledge entry safety measures are important to safeguard a company’s property, keep buyer belief, and meet regulatory necessities.
A complete Information Safety Platform is crucial for full visibility and management of delicate knowledge. One instance is Satori’s Common Information Permissions Scanner (UDPS), an open-source authorization evaluation device. UDPS, out there on GitHub, permits common visibility into knowledge entry permissions throughout numerous knowledge shops. With this device, it is simpler to determine who has the potential to entry delicate knowledge, which may also help organizations take a proactive strategy to enhancing their safety posture, streamline compliance, and guarantee well-governed knowledge entry.
Understanding the Want for Common Information Permissions
In managing knowledge entry permissions throughout massive volumes of information, knowledge engineers need to cope with a number of challenges.
One such problem is the complexity of granting and revoking permissions to varied customers throughout many knowledge repositories. As organizations scale up their operations and knowledge grows exponentially, holding monitor of who has entry to what turns into more and more difficult.
This complexity can result in errors, safety vulnerabilities, and difficulties in sustaining an audit path of information entry, which is essential for compliance and safety functions. Information engineers are sometimes tasked with sustaining a effective steadiness between offering entry to licensed customers and safeguarding knowledge from unauthorized entry.
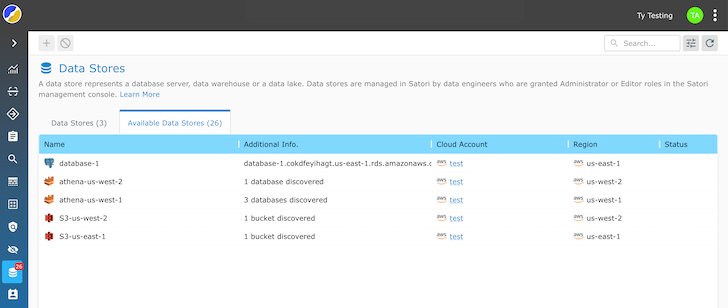
Dispersed Information Shops
The info entry permissions administration panorama has turn into extra difficult in recent times as a result of widespread adoption of cloud computing. Information engineers face a extremely distributed knowledge panorama, with knowledge now residing in on-prem knowledge facilities, a number of cloud platforms, and edge units. Guaranteeing knowledge safety and governance throughout these various environments requires a extra unified strategy to knowledge entry permissions.
The dynamic nature of the cloud implies that conventional entry management fashions could now not suffice, and knowledge engineers should undertake new paradigms that embody granular management, visibility, and governance.
Satori’s UDPS
Satori’s open-source UDPS takes a proactive and complete strategy to knowledge entry authorization. It scans and analyzes the permissions mannequin of every knowledge platform to retrieve a human-readable checklist of customers and their entry degree to knowledge property, together with database tables, cloud storage buckets, information, and extra.
As a substitute of requiring knowledge engineers to navigate the intricacies of every particular person knowledge retailer’s entry controls, UDPS gives a unified platform to view and handle knowledge permissions throughout all knowledge repositories. Information engineers now not want to make use of totally different entry management mechanisms, lowering the potential for errors and unauthorized entry.
The standout function of UDPS is its common visibility into knowledge entry permissions. After scanning all databases, knowledge warehouses, cloud accounts, and knowledge lakes, UDPS analyzes the permissions and retrieves a listing of customers, their entry ranges, and what they’ve entry to.
The Common Information Permissions Scanner is on the market in two methods:
- Scan the permissions construction of a database to get the checklist of all customers and knowledge property they will entry.
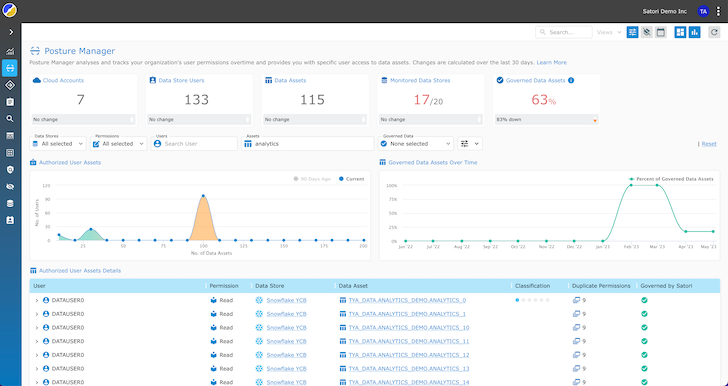
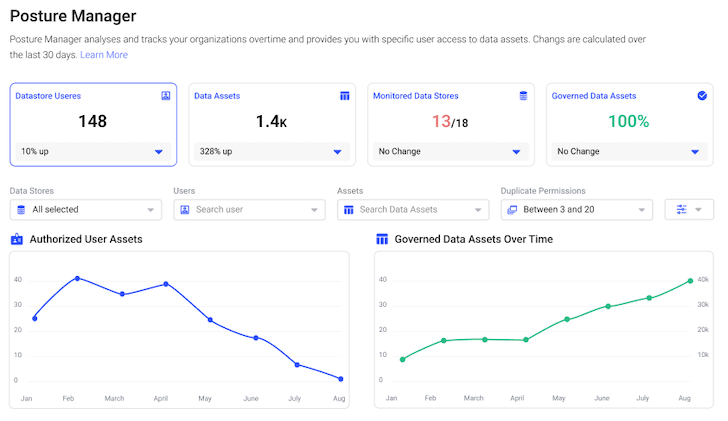
- Posture Supervisor – a completely managed SaaS answer to periodically scan, retailer, and visualize all customers and knowledge property they will entry.
Information engineers achieve larger visibility, permitting them to shortly determine overprivileged customers, unauthorized entry, or uncommon habits in actual time. Common visibility simplifies the auditing course of and ensures that knowledge entry stays clear and compliant with safety and privateness laws.
Information engineers can effectively handle knowledge safety and governance, lowering safe and compliant knowledge entry challenges.
Advantages of Utilizing an OS UDPS
- Figuring out Overprivileged Customers and Lowering Safety Dangers: With complete visibility into knowledge entry permissions, organizations can pinpoint people or accounts granted pointless or extreme entry to delicate knowledge. By figuring out and rectifying overprivileged customers, companies can scale back the chance of information breaches and unauthorized knowledge entry.
- Streamlining Compliance Reporting and Privateness Legislation Compliance: Organizations generate compliance reviews extra effectively by aggregating knowledge entry info throughout numerous repositories. This streamlines the reporting course of and ensures knowledge entry aligns with regulatory necessities. Companies can keep compliance with knowledge safety legal guidelines corresponding to GDPR or HIPAA, lowering the potential for authorized points and fines.
- Enhancing Information Safety and Information Posture: Information engineers and safety proactively deal with safety gaps by clearly viewing knowledge entry authorizations and figuring out potential vulnerabilities. Enhanced knowledge safety protects a company’s property and preserves its popularity and buyer belief in an more and more data-sensitive world.
- Detecting Uncommon Habits and Monitoring Information Utilization: Protect knowledge integrity by detecting uncommon habits and monitoring knowledge utilization throughout complicated knowledge infrastructures. It screens entry patterns and raises alerts when deviations from the norm are detected. This proactive strategy permits organizations to reply to potential safety incidents swiftly, lowering the influence of information breaches or insider threats. By monitoring knowledge utilization, companies achieve helpful insights into using their knowledge, which may inform decision-making processes and enhance operational effectivity.
- Simplifying Authorization Administration for Information and Safety Engineers: Simplifies the intricate activity of authorization administration for knowledge and safety engineers. As a substitute of navigating a number of knowledge repositories and entry management techniques, these professionals can use a centralized platform to handle and implement knowledge entry insurance policies. This streamlines the method, reduces the probability of misconfigurations, and ensures that knowledge authorization is constant and clear throughout the group. Simplified authorization administration interprets to extra environment friendly knowledge governance and a stronger safety posture.
- Enhancing Productiveness: Untangling the online of permissions complexity permits seamless info sharing throughout departments, accelerating time-to-value. Which means knowledge will be effectively accessed and leveraged when wanted, facilitating agile decision-making and fostering collaboration amongst groups. It removes the limitations that after hindered the fast circulation of knowledge inside the enterprise.
Ease of Implementation
Some key insights into the benefit of implementing Satori’s answer:
- Agentless Deployment: There is no such thing as a want to put in brokers or extra software program in your knowledge shops or techniques. This agentless strategy simplifies the deployment course of and eliminates the necessity for complicated configurations or alterations to your present infrastructure.
- Zero Code Adjustments: It doesn’t require any adjustments to present knowledge constructions or schemas. The info stays intact and retains its construction.
- Person-Pleasant Interface: The interface simplifies the definition and enforcement of information entry insurance policies. Safety and knowledge engineering groups can simply configure and handle fine-grained insurance policies to manage who can entry particular knowledge parts with out requiring specialised coding or intensive technical experience.
- Actual-time Coverage Updates: Permits for real-time coverage updates in order that safety measures are tailored on the fly to deal with rising threats or altering compliance necessities. This agility simplifies the continuing administration of information safety controls.
- Non-Intrusive Information Encryption: Clear knowledge encryption that does not disrupt present consumer interactions. Information stays accessible to licensed customers with out noticeable adjustments in how they work together.
- Compatibility and Scalability: Suitable with many knowledge shops, databases, knowledge lakes, and cloud platforms. It additionally scales along with your group’s wants.
Implementation is an easy and hassle-free course of. It would not require alterations to your knowledge constructions or consumer interactions. The convenience of implementation makes Satori a lovely answer for organizations trying to improve their knowledge safety effortlessly.
Conclusion
Satori’s Common Information Permissions Scanner (UDPS) simplifies knowledge entry authorization complexities by offering a centralized, non-intrusive answer. It gives common visibility into knowledge entry permissions throughout various knowledge repositories, enabling organizations to determine overprivileged customers, streamline compliance reporting, and improve knowledge safety. It’s simple to implement, with no adjustments to present knowledge constructions or consumer interactions; learn extra concerning the UDPS within the mission documentation.
Organizations can detect uncommon habits, monitor knowledge utilization, and simplify authorization administration, contributing to a stronger safety posture and streamlined knowledge governance.