Android smartphone customers in India are the goal of a brand new malware marketing campaign that employs social engineering lures to put in fraudulent apps which can be able to harvesting delicate knowledge.
“Utilizing social media platforms like WhatsApp and Telegram, attackers are sending messages designed to lure customers into putting in a malicious app on their cell machine by impersonating reliable organizations, comparable to banks, authorities providers, and utilities,” Microsoft menace intelligence researchers Abhishek Pustakala, Harshita Tripathi, and Shivang Desai mentioned in a Monday evaluation.
The last word objective of the operation is to seize banking particulars, fee card info, account credentials, and different private knowledge.
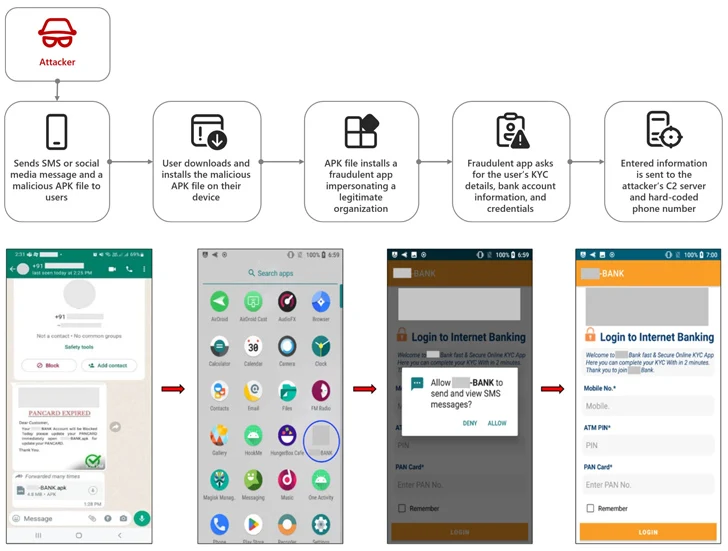
The assault chains contain sharing malicious APK information by way of social media messages despatched on WhatsApp and Telegram by falsely presenting them as banking apps and inducing a way of urgency by claiming that the targets’ financial institution accounts shall be blocked until they replace their everlasting account quantity (PAN) issued by the Indian Revenue Tax Division by the bogus app.
Upon set up, the app urges the sufferer to enter their checking account info, debit card PIN, PAN card numbers, and on-line banking credentials, that are subsequently transmitted to an actor-controlled command-and-control (C2) server and a hard-coded telephone quantity.
“As soon as all of the requested particulars are submitted, a suspicious observe seems stating that the small print are being verified to replace KYC,” the researchers mentioned.
“The person is instructed to attend half-hour and to not delete or uninstall the app. Moreover, the app has the performance to cover its icon, inflicting it to vanish from the person’s machine house display screen whereas nonetheless working within the background.”
One other notable side of the malware is that it requests the person to grant it permission to learn and ship SMS messages, thereby enabling it to intercept one-time passwords (OTPs) and ship the victims’ messages to the menace actor’s telephone quantity by way of SMS.
Variants of the banking trojan found by Microsoft have additionally been discovered to steal bank card particulars together with personally identifiable info (PII) and incoming SMS messages, exposing unsuspecting customers to monetary fraud.
Nevertheless, it is price noting that for these assaults to achieve success, customers should allow the choice to put in apps from unknown sources exterior of the Google Play Retailer.
“Cell banking trojan infections can pose vital dangers to customers’ private info, privateness, machine integrity, and monetary safety,” the researchers mentioned. “These threats can usually disguise themselves as reliable apps and deploy social engineering techniques to realize their objectives and steal customers’ delicate knowledge and monetary belongings.”
The event comes because the Android ecosystem has additionally come below assault from the SpyNote trojan, which has focused Roblox customers below the guise of a mod to siphon delicate info.
In one other occasion, pretend grownup web sites are getting used as lures to entice customers into downloading an Android malware referred to as Enchant that particularly focuses on pilfering knowledge from cryptocurrency wallets.
“Enchant malware makes use of the accessibility service characteristic to focus on particular cryptocurrency wallets, together with imToken, OKX, Bitpie Pockets, and TokenPocket pockets,” Cyble mentioned in a latest report.
“Its major goal is to steal crucial info comparable to pockets addresses, mnemonic phrases, pockets asset particulars, pockets passwords, and personal keys from compromised units.”
Final month, Physician Net uncovered a number of malicious apps on the Google Play Retailer that displayed intrusive advertisements (HiddenAds), subscribed customers to premium providers with out their data or consent (Joker), and promoted funding scams by masquerading as buying and selling software program (FakeApp).
The onslaught of Android malware has prompted Google to announce new security measures comparable to real-time code-level scanning for apps that haven’t been beforehand scanned earlier than. It additionally launched restricted settings with Android 13 that prohibits apps from acquiring entry to crucial machine settings (e.g., accessibility) until it is explicitly enabled by the person.
It is not simply Google. Samsung, in late October 2023, unveiled a brand new Auto Blocker possibility for Galaxy units that stops app installations from sources aside from Google Play Retailer and Galaxy Retailer, and blocks dangerous instructions and software program installations by the USB port.
To keep away from downloading malicious software program from Google Play and different trusted sources, customers are suggested to examine the legitimacy of the app builders, scrutinize evaluations, and vet the permissions requested by the apps.
Replace
Following the publication of the story, a Google spokesperson shared the next assertion with The Hacker Information –
Customers are protected by Google Play Shield, which is enabled by default and warns customers or blocks apps recognized to exhibit malicious conduct on Android units with Google Play Providers, even when these apps come from sources exterior of Play. Google applied protections for TrojanSpy:AndroidOS/SpyBanker.Y in December 2022 and for Trojan:AndroidOS/Banker.U in September 2023.