Net Utility Safety consists of a myriad of safety controls that guarantee that an internet software:
- Capabilities as anticipated.
- Can’t be exploited to function out of bounds.
- Can not provoke operations that it’s not speculated to do.
Net Purposes have develop into ubiquitous after the growth of Net 2.0, which Social Media Platforms, E-Commerce web sites, and electronic mail shoppers saturating the web areas lately.
Because the purposes eat and retailer much more delicate and complete information, they develop into an ever extra interesting goal for attackers.
Frequent Assault Strategies
The three commonest vulnerabilities that exist on this house are Injections (SQL, Distant Code), Cryptographic Failures (beforehand delicate information publicity), and Damaged Entry Management (BAC). Right now, we’ll give attention to Injections and Damaged Entry Management.
Injections
SQL is the commonest Database software program that’s used, and hosts a plethora of cost information, PII information, and inner enterprise information.
A SQL Injection is an assault that makes use of malicious SQL code for backend database manipulation to entry data that was not supposed to be displayed.
The place to begin for this, is a command such because the one under:
This can return ALL rows from the “Customers” desk, since OR 1=1 is at all times TRUE. Going additional with this, this methodology can even return passwords if there are any.
Image an assault like this being carried out towards a big social media firm, or a big e-commerce enterprise, and one can start to see how a lot delicate information might be retrieved with only one command.
Damaged Entry Management
Damaged Entry Management (BAC) has risen the ranks on the OWASP high ten from fifth to the commonest Net Utility Safety Dangers. The 34 Frequent Weak spot Enumerations (CWEs) mapped to Damaged Entry Management had extra occurrences in purposes than another class throughout OWASP’s latest testing.
The most typical sorts of BAC, is Vertical and Horizontal privilege escalation. Vertical privilege escalation happens when a person can elevate their privileges and carry out actions, they need to not have entry to do.
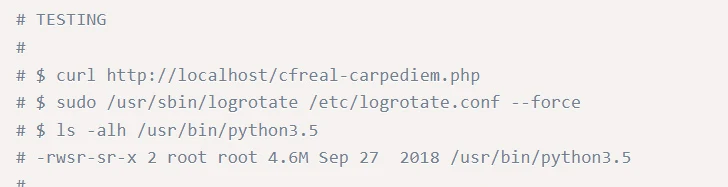
The CVE-2019-0211, which was an Apache Native Privilege Escalation. This crucial vulnerability, from 2019, affected Apache HTTP servers operating on Unix techniques, particularly these using the mod_prefork, mod_worker, and mod_event libraries.
This granted attackers the potential to execute unprivileged scripts, doubtlessly resulting in root entry and compromising shared internet hosting providers. Exploiting this flaw requires the manipulation of shared-memory areas inside Apache’s employee processes, which have to be achieved earlier than initiating an Apache swish restart.
The under is a screenshot of the POC code. As one can see, a sure degree of technical capacity is required on this respect, nevertheless, vertical privilege escalation can simply as simply happen when a person’s permissions are overly permissive, or not revoked after they depart a enterprise.
This takes us again to the precept of least privilege, a ubiquitous time period discovered all through the IT world, that’s now turning into extra commonplace as we realise how essential internet purposes have develop into.
Horizontal Privilege Escalation is when a person good points entry to information they aren’t speculated to have entry to, however that information is held on the identical degree as their very own permissions. This may be seen with one customary person accessing the info of one other customary person. While this shouldn’t be allowed, the privileges usually are not rising vertical, however spreading horizontally. That is typically seen as extra harmful, as it may possibly happen with out elevating any alerts on safety techniques.
With BAC turning into ever extra current within the final couple of years, it is very important bear in mind:
- Solely relying on obfuscation shouldn’t be a enough methodology for entry management.
- If a useful resource shouldn’t be meant to be accessible to the general public, it ought to be denied entry by default.
- Builders ought to explicitly specify allowed entry for every useful resource on the code degree, with entry denial because the default setting.
Finest Practices – Learn between the Traces (of code!)
To keep up safety, builders have to confirm incoming information, implement parameterized queries when interacting with databases, and apply efficient session administration strategies to guard delicate information. A lot of this depends on each the safety of internet browsers, but additionally of the back-end safety of the net servers delivering internet content material, resulting in a segregation of duties in internet safety.
The largest drawback that arises right here, is that while Net Utility Firewalls (WAFs), can mitigate these dangers, a lot of the accountability for safe implementation of internet content material lands on the toes of the builders who put these websites collectively. Cybersecurity can typically develop into an afterthought, with performance being most well-liked.
Sensible Instance – Enter Validation
Enter Validation is the only and only methods to implement safe coding, on this instance to forestall SQL injections.
- Person Enter: The person gives enter, for instance:
- Sanitization: The person enter shouldn’t be instantly inserted into the SQL question. It’s sanitized and handled as information, not as SQL code.
- Question Execution: The SQL question is executed with the person enter as a parameter:
- As such, the question enters the backend as under:
On this code, the (user_input,) is a tuple containing the person’s enter. The database driver takes care of escaping and correctly dealing with this enter. It ensures that the enter is handled as an information worth, not executable SQL code.
If the person enter incorporates malicious code, akin to “105 or 1=1,” it’s not executed as SQL. As an alternative, it is handled as a worth to be in comparison with the UserId within the database.
The database driver routinely handles the escaping of the enter, stopping it from affecting the construction of the SQL question or introducing safety vulnerabilities.
Net Utility Firewalls (WAFs)
A WAF operates at layer 7 of the OSI mannequin, and acts as a reverse proxy, guaranteeing consumer visitors passes by way of the WAF earlier than coming into the backend server. The foundations or insurance policies on the WAF shield towards the documented vulnerabilities which are current in these backend servers and filter out malicious visitors.
There are a plethora of WAFs in the marketplace, and these can all present a powerful defence towards the extra novel assaults, and contribute effectively to a defence in depth strategy, the apply of safe coding is one thing that make sure the foundations of the net software is safe and won’t fall sufferer to extra complicated or novel assaults sooner or later.
WAFs are at the moment shifting in direction of a mix of safety mannequin that use behavioural-analysis applied sciences to detect malicious threats, and additional mitigate towards the threats of extra superior ‘bots’ which have been leveraged for low-effort assaults on web sites.
The principle downside of utilizing a WAF, apart from the added latency and HTTP overhead, is the truth that a WAF might be bypassed through the use of a 0-day exploit towards an online software, which safe coding and proper sanitisation can mitigate towards extra successfully that offsetting all Net software safety to a WAF. It is very important bear in mind a WAF is solely a layer of safety, and never the whole resolution.
Incident Response and Restoration
SecurityHQ’s strategies to mitigate towards assaults:
- Using a WAF as a primary line of defence is crucial to make sure enterprise can defend towards a big quantity of assaults.
- Guarantee up-to-date and powerful customary algorithms and protocols are in use, this ought to be paired with correct key administration.
- Encrypt information in transit with safe protocols akin to TLS with ahead secrecy (FS) ciphers, cipher prioritization by the server. Implement encryption utilizing directives akin to HTTP Strict Transport Safety (HSTS).
- Allow bot administration methods on web sites and have a documented incident response plan.
- Guarantee safe growth practices are in place, with a documented means of testing new options on internet purposes and guarantee enter validation is deployed.
- This ought to be coupled with guaranteeing the precept of least privilege.
For extra data on these threats, converse to an knowledgeable right here. Or in case you suspect a safety incident, you may report an incident right here.
Observe: This text was expertly written by Tim Chambers, Senior Cyber Safety Supervisor at SecurityHQ