
Attackers are exploiting a critical-severity privilege escalation vulnerability (CVE-2025–8489) within the King Addons for Elementor plugin for WordPress, which lets them acquire administrative permissions in the course of the registration course of.
The risk exercise began on October 31, only a day after the difficulty was publicly disclosed. To this point, the Wordfence safety scanner from Defiant, an organization that gives safety companies for WordPress web sites, has blocked greater than 48,400 exploit makes an attempt.
King Addons is a third-party add-on for Elementor, a well-liked visible web page builder plugin for WordPress websites. It’s used on roughly 10,000 web sites, offering further widgets, templates, and options.
CVE-2025–8489, found by researcher Peter Thaleikis, is a flaw within the plugin’s registration handler that permits anybody signing as much as specify their consumer function on the web site, together with the administrator function, with out imposing any restrictions.
In line with observations from Wordfence, attackers ship a crafted ‘admin-ajax.php’ request specifying ‘user_role=administrator,’ to create rogue admin accounts on focused websites.
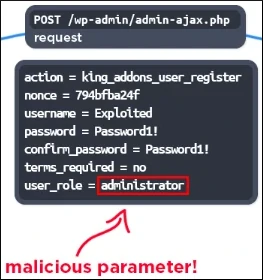
Supply: Wordfence
The researchers seen a peak within the exploitation exercise between November 9 and 10, with two IP addresses being probably the most energetic: 45.61.157.120 (28,900 makes an attempt) and 2602:fa59:3:424::1 (16,900 makes an attempt).
Wordfence offers a extra in depth listing of offensive IP addresses and recommends that web site directors search for them within the log recordsdata. The presence of latest administrator accounts can be a transparent signal of compromise.
Web site house owners are suggested to improve to model 51.1.35 of King Addons, which addresses CVE-2025–8489, launched on September 25.
Wordfence researchers are additionally warning of one other crucial vulnerability within the Superior Customized Fields: Prolonged plugin, energetic on greater than 100,000 WordPress web sites, which could be exploited by an unauthenticated attacker to execute code remotely.
The flaw impacts variations 0.9.0.5 by means of 0.9.1.1 of the plugin and is at present tracked as CVE-2025-13486. It was found and reported responsibly by Marcin Dudek, the pinnacle of the nationwide laptop emergency response staff (CERT) in Poland.
The vulnerability is “as a result of operate accepting consumer enter after which passing that by means of call_user_func_array(),” Wordfence explains.
“This makes it potential for unauthenticated attackers to execute arbitrary code on the server, which could be leveraged to inject backdoors or create new administrative consumer accounts.”
The safety subject was reported on November 18, and the plugin vendor addressed it in model 0.9.2 of Superior Customized Fields: Prolonged, launched a day after receiving the vulnerability report.
Provided that the flaw could be leveraged with out authentication solely by means of a crafted request, the general public disclosure of technical particulars is prone to generate malicious exercise.
Web site house owners are suggested to maneuver to the newest model as quickly as potential or disable the plugin on their websites.
Damaged IAM is not simply an IT downside – the impression ripples throughout your complete enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with trendy calls for, examples of what “good” IAM seems to be like, and a easy guidelines for constructing a scalable technique.



