
The FBI has warned a few new pattern in ransomware assaults the place a number of strains are deployed on victims’ networks to encrypt programs in beneath two days.
FBI’s warning comes within the type of a Personal Business Notification prompted by developments noticed beginning July 2023.
The federal regulation enforcement company explains that ransomware associates and operators have been noticed utilizing two distinct variants when focusing on sufferer organizations. Variants utilized in these twin ransomware assaults embody AvosLocker, Diamond, Hive, Karakurt, LockBit, Quantum, and Royal.
“This use of twin ransomware variants resulted in a mixture of information encryption, exfiltration, and monetary losses from ransom funds,” the FBI stated.
“Second ransomware assaults towards an already compromised system may considerably hurt sufferer entities.”
48 hours between ransomware assaults
In distinction to the previous, when ransomware teams sometimes required a minimal of 10 days to execute such assaults, now the overwhelming majority of ransomware incidents focusing on the identical sufferer happen inside a mere 48-hour timeframe of one another, in response to FBI’s information.
Coveware CEO & Co-Founder Invoice Siegel additionally informed BleepingComputer that double-encryption has been a factor for years, with some corporations dealing with re-extortion because the risk actor doesn’t present decryptors for each ransomware assaults.
“There are some risk actor teams that deliberately use two totally different variants on each assault. As an illustration, we usually see MedusaLocker and Globemposter used on the identical time by the identical risk actor on a single sufferer,” Siegel stated.
“Conditions the place the preliminary entry dealer sells entry to the community to 2 totally different ransomware associates that use totally different manufacturers of ransomware. Each associates are then within the community, impacting machines in shut time proximity to one another.”
Moreover, the FBI says that beginning in early 2022, a number of ransomware gangs have begun including new code to their customized information theft instruments, wipers, and malware to evade detection.
In different incidents, malware containing data-wiping performance was configured to stay dormant on compromised programs till a predetermined time. At that time, it will execute to destroy information on targets’ networks at periodic intervals.
Breached 3 times in two months
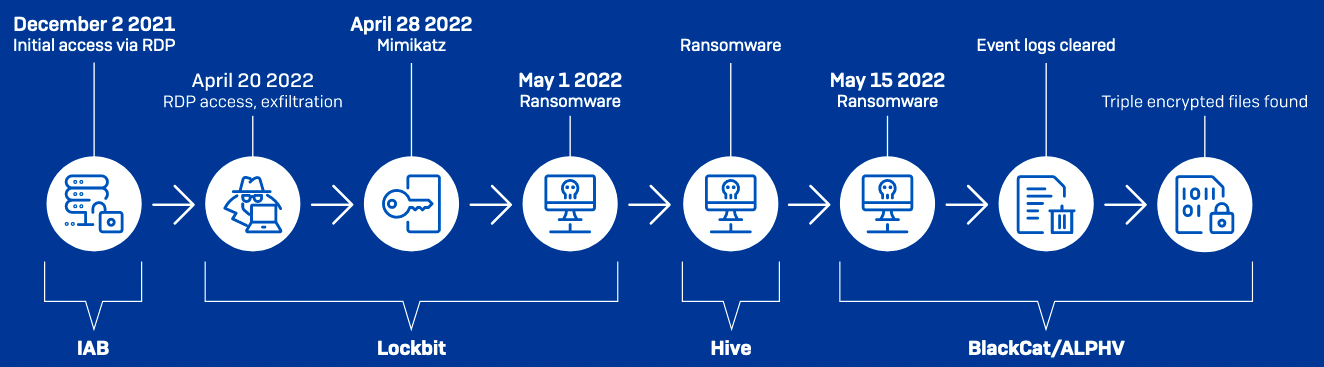
In a single such assault that began final 12 months, in April, an automotive provider was breached 3 times by LockBit, Hive, and ALPHV/BlackCat associates inside simply two months, in response to Sophos X-Ops incident responders.
Whereas the sufferer group was busy restoring programs encrypted with LockBit and Hive ransomware after the primary breach, an ALPHV/BlackCat affiliate linked to beforehand compromised units to steal information and—as soon as once more—lock information with their very own encrypter.
To make issues even worse, the incident responders found that a number of the sufferer’s information had been encrypted as much as 5 instances.
“As a result of the Hive assault began 2 hours after Lockbit, the Lockbit ransomware was nonetheless operating – so each teams stored discovering information with out the extension signifying that they have been encrypted,” the Sophos crew stated.
The way to defend towards ransomware assaults
The FBI advises organizations to keep up shut connections with FBI Area Workplaces of their area. These relationships will enable the FBI to help with the identification of vulnerabilities and the mitigation of potential threat-related actions.
Community defenders are additionally suggested to use mitigation measures included within the FBI’s Personal Business Notification printed on Thursday to restrict the attackers’ use of frequent system and community discovery strategies and cut back the chance of ransomware assaults.
They’re urged to maintain all programs up-to-date and conduct thorough scans of their infrastructures to determine potential backdoors or vulnerabilities launched by the attackers as fail-safes that will allow them to regain entry to the community if their entry is blocked.
Defenders must also safe companies like VNC, RDP, and different distant entry options accessible from exterior sources. Entry must be restricted solely by way of VPN and completely granted to accounts with sturdy passwords and enforced multi-factor authentication (MFA).
One other really useful follow contains community segmentation, the place vital servers are remoted inside VLANs to reinforce safety. Moreover, conducting complete scans and audits throughout all the community is essential to figuring out units weak to exploitation as a consequence of a scarcity of crucial patches.


