
Hackers started exploiting an authentication bypass vulnerability in SmarterTools’ SmarterMail e-mail server and collaboration instrument that permits resetting admin passwords.
An authentication bypass vulnerability in SmarterTools SmarterMail, which permits unauthenticated attackers to reset the system administrator password and acquire full privileges, is now actively exploited within the wild.
The problem resides within the force-reset-password API endpoint, which is deliberately uncovered with out authentication.
Researchers at cybersecurity firm watchTowr reported the problem on January 8, and SmarterMail launched a repair on January 15 with out an identifier being assigned.
After the problem was addressed, the researchers discovered proof that menace actors began to take advantage of it simply two days later. This means that hackers reverse-engineered the patch and located a strategy to leverage the flaw.
SmarterMail is a self-hosted Home windows e-mail server and collaboration platform developed by SmarterTools that gives SMTP/IMAP/POP e-mail, webmail, calendars, contacts, and fundamental groupware options.
It’s sometimes utilized by managed service suppliers (MSPs), small and medium-sized companies, and internet hosting suppliers providing e-mail companies. SmarterTools claims that its merchandise have 15 million customers in 120 international locations.
The CVE-less flaw arises from the API endpoint ‘force-reset-password’ accepting attacker-controlled JSON enter, together with a ‘IsSysAdmin’ bool kind property, which, if set to ‘true,’ forces the backend to execute the system administrator password reset logic.
Nonetheless, the mechanism doesn’t carry out any safety controls or confirm the previous password, regardless of the ‘OldPassword’ area being current within the request, watchTowr researchers discovered.
Consequently, anybody who is aware of or guesses an admin username might set a brand new password and hijack the account.
The researchers be aware that the flaw impacts solely admin-level accounts, not common customers.
With admin-level entry, attackers can run OS instructions, thus getting full distant code execution on the host.
watchTowr researchers have created a proof-of-concept exploit that demonstrates SYSTEM-level shell entry.
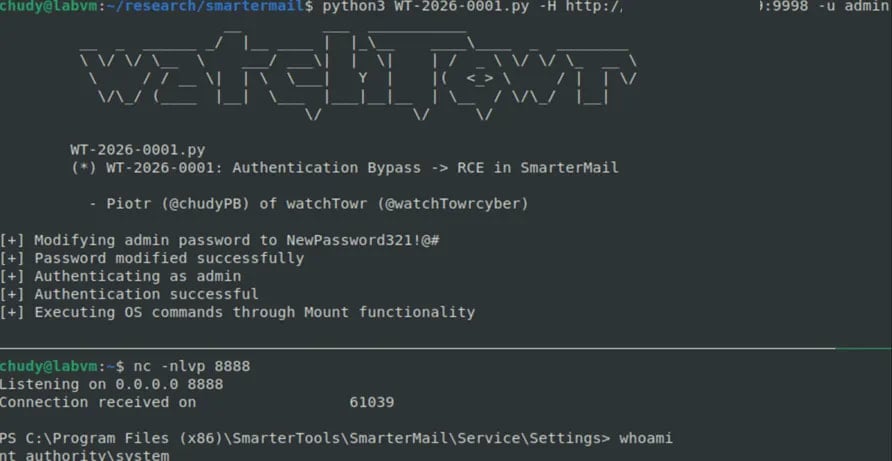
Supply: watchTowr
The researchers realized that the vulnerability was being exploited within the wild from an nameless person, who said that any person was resetting administrator passwords.
To again their claims, the tipster pointed watchTowr researchers to a discussion board publish describing an analogous scenario.
Analyzing the shared logs revealed that these assaults focused the ‘force-reset-password’ endpoint, supporting the conclusion that the problem is at the moment underneath energetic exploitation.
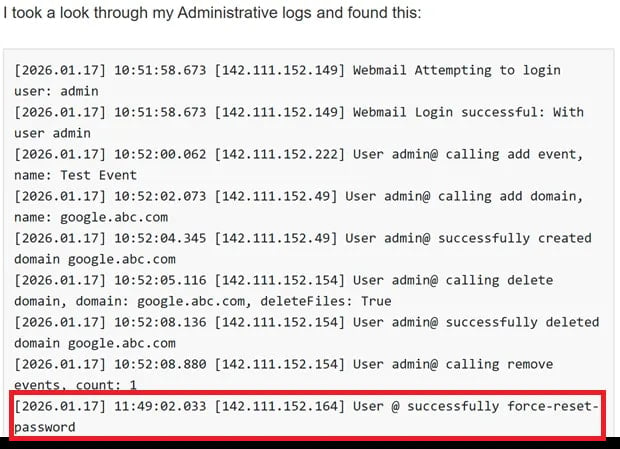
Supply: watchTowr
Two weeks earlier, watchTowr found a essential pre-auth RCE flaw in SmarterMail, tracked as CVE-2025-52691, which led to the invention of the most recent subject.
Customers of SmarterMail are really helpful to improve to the most recent model of the software program, Construct 9511, launched on January 15, that addresses each points.
Replace 1/23 – The vulnerability has obtained the identifier CVE-2026-23760, rated “essential” (CVSS rating: 9.3).
Moreover, Huntress researchers have additionally printed a report with their observations on the in-the-wild exploitation exercise.




