In a nutshell: USB worms are historically designed to unfold wherever they will, hopping on any detachable storage gadget they will discover. When cyber-espionage and cyber-war enter the fray, this spreading functionality can work in opposition to the malware’s authentic intent.
Examine Level Analysis not too long ago found and analyzed a brand new worm with USB spreading capabilities, a seemingly “easier” malware created by Gamaredon, a well known group working with the Russian Federal Safety Service (FSB). Also referred to as Primitive Bear, ACTINIUM, and Shuckworm, Gamerdon is an uncommon participant throughout the Russian espionage ecosystem, which goals virtually solely at compromising Ukraine targets.
Examine Level mentioned that whereas different Russian cyber-espionage groups favor to cover their presence as a lot as they will, Gamaredon is thought for its large-scale campaigns whereas nonetheless specializing in regional targets. LitterDrifter, the group’s not too long ago found worm, appears to stick to Gamaredon’s traditional habits because it has probably gone means past its authentic targets.
LitterDrifter is a worm written within the much-maligned VBScript language (VBS) with two major functionalities: “automated” spreading over USB flash drives, and listening to distant orders coming from the creators’ command&management (C2) servers. The malware appears to be an evolution of Gamaredon’s earlier efforts with USB propagation, Examine Level researchers defined.
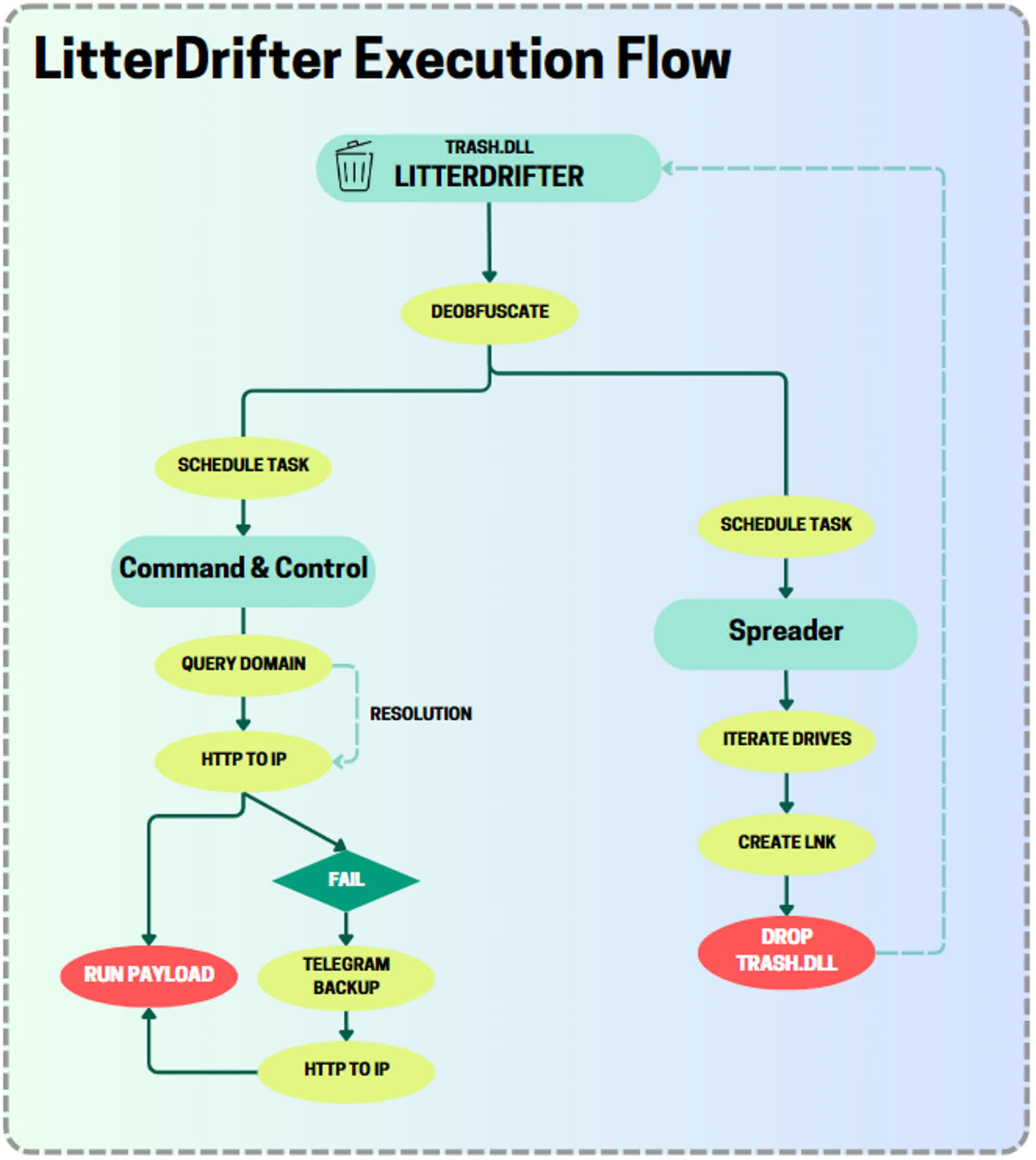
LitterDrifter employs two separate modules to attain its targets, that are executed by a “closely obfuscated” orchestrator VBS element discovered within the trash.dll library. The worm tries to ascertain persistence on Home windows methods by including new scheduled duties and Registry keys, exploiting the Home windows Administration Instrumentation (WMI) framework to establish USB targets and create shortcuts with random names.
The worm tries to contaminate a USB goal as quickly because the flash drive is linked to the system. After an infection, LitterDrifter tries to contact a C2 server hidden behind a community of dynamic IP addresses which normally final so long as 28 hours. As soon as a connection has been established, LitterDrifter can obtain further payloads, decode and eventually execute them on a compromised system.
Examine Level Analysis mentioned that no additional payloads have been downloaded through the evaluation job, which signifies that LitterDrifter is probably going the primary stage of a extra complicated, ongoing assault. The vast majority of LitterDrifter infections have been found in Ukraine, however the worm was additionally recognized on PCs situated within the US, Germany, Vietnam, Chile, Poland. Gamaredon has probably misplaced management of its worm, which in the end unfold to unintended targets earlier than the total assault was deployed.