
A number of ransomware gangs are utilizing a packer-as-a-service platform named Shanya to assist them deploy payloads that disable endpoint detection and response options on sufferer techniques.
Packer providers present cybercriminals with specialised instruments to package deal their payloads in a method that obfuscates malicious code to evade detection by most recognized safety instruments and antivirus engines.
The Shanya packer operation emerged in late 2024 and has grown in reputation considerably, with malware samples utilizing it being noticed in Tunisia, the UAE, Costa Rica, Nigeria, and Pakistan, as per telemetry information from Sophos Safety.
Among the many ransomware teams confirmed to have used it are Medusa, Qilin, Crytox, and Akira, with the latter being the one which makes use of the packers service most frequently.

Supply: Sophos
How Shanya works
Risk actors submit their malicious payloads to Shanya, and the service returns a “packed” model with a customized wrapper, utilizing encryption and compression.
The service promotes the singularity of the ensuing payloads, highlighting the “non-standard module loading into reminiscence, wrapper over the system loaderStub uniqueization,” with “every buyer receiving their very own (comparatively) distinctive stub with a singular encryption algorithm upon buy.”

Supply: Sophos
The payload is inserted right into a memory-mapped copy of the Home windows DLL file ‘shell32.dll.’ This DLL file has valid-looking executable sections and measurement, and its path seems regular, however its header and .textual content part have been overwritten with the decrypted payload.
Whereas the payload is encrypted contained in the packed file, it’s decrypted and decompressed whereas nonetheless totally in reminiscence, after which inserted into the ‘shell32.dll’ copy file, by no means touching the disk.
Sophos researchers discovered that Shanya performs checks for endpoint detection and response (EDR) options by calling the ‘RtlDeleteFunctionTable’ perform in an invalid context.
This triggers an unhandled exception or a crash when operating beneath a user-mode debugger, disrupting automated evaluation earlier than full execution of the payload.
Disabling EDRs
Ransomware teams usually search to disable EDR instruments operating on the goal system earlier than the information theft and encryption phases of the assault.
The execution often happens by way of DLL side-loading, combining a authentic Home windows executable reminiscent of ‘consent.exe’ with a Shanya-packed malicious DLL like msimg32.dll, model.dll, rtworkq.dll, or wmsgapi.dll.
In response to the evaluation from Sophos, the EDR killer drops two drivers: a legitimately signed ThrottleStop.sys (rwdrv.sys) from TechPowerUp, which accommodates a flaw enabling arbitrary kernel reminiscence writing, and the unsigned hlpdrv.sys.
The signed driver is used for privilege escalation, whereas hlpdrv.sys disables safety merchandise primarily based on instructions obtained from consumer mode.
The user-mode element enumerates operating processes and put in providers, then compares the outcomes in opposition to entries in an in depth hardcoded listing, sending a “kill” command to the malicious kernel driver for every match.
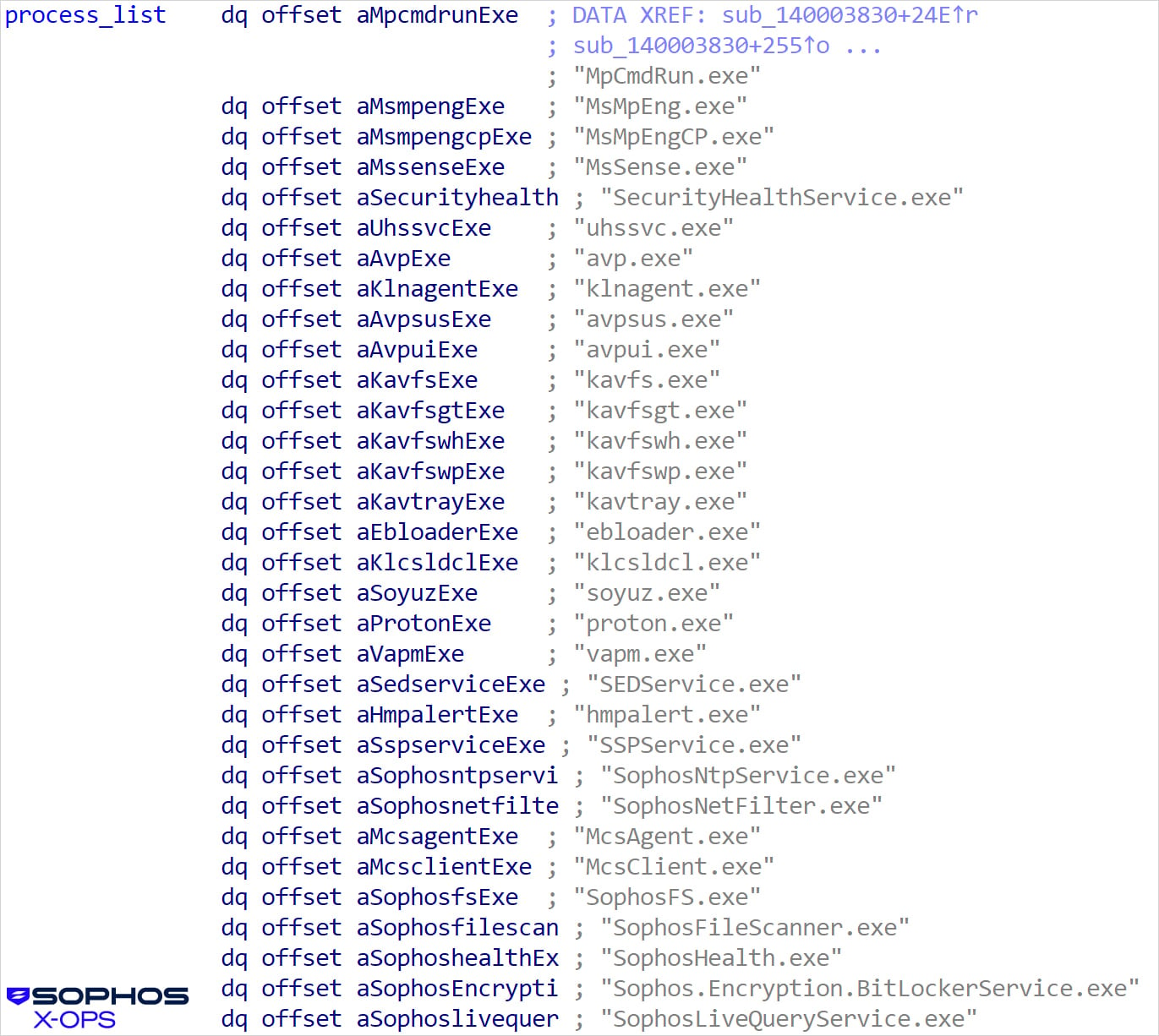
Supply: Sophos
Aside from ransomware operators centered on EDR disabling, Sophos has additionally noticed latest ClickFix campaigns using the Shanya service to package deal the CastleRAT malware.
Sophos notes that ransomware gangs typically depend on packer providers to organize EDR killers for being deployed undetected.
The researchers present an in depth technical evaluation of among the payloads filled with Shanya.
The report additionally contains indicators of compromise (IoCs) related to Shanya-powered campaigns.
Damaged IAM is not simply an IT downside – the influence ripples throughout your complete enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with fashionable calls for, examples of what “good” IAM seems to be like, and a easy guidelines for constructing a scalable technique.



