
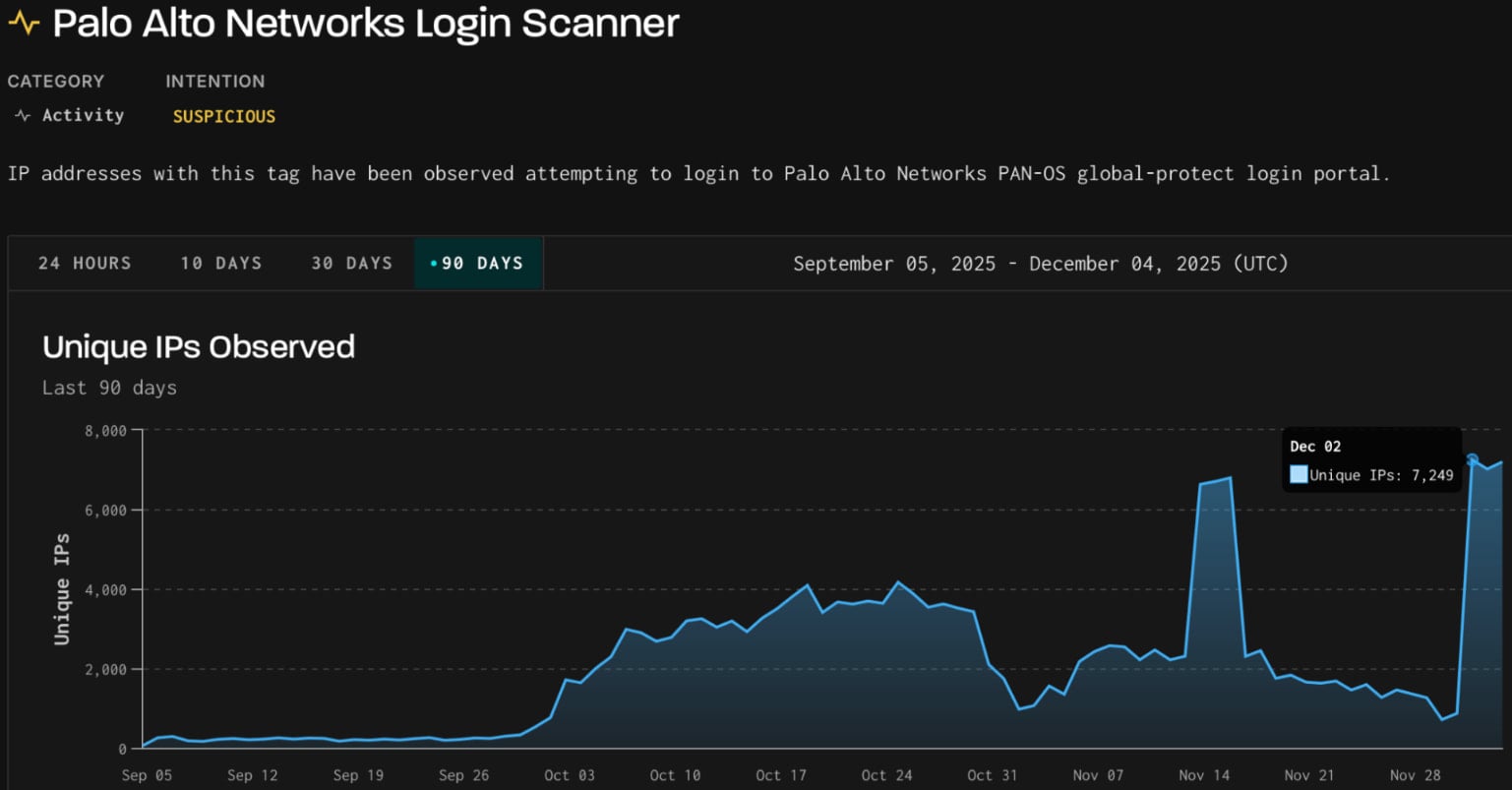
A marketing campaign has been noticed concentrating on Palo Alto GlobalProtect portals with login makes an attempt and launching scanning exercise in opposition to SonicWall SonicOS API endpoints.
The exercise began on December 2nd and originated from greater than 7,000 IP addresses from infrastructure operated by the German IT firm 3xK GmbH, which runs its personal BGP community (AS200373) and operates as a internet hosting supplier.
Initially, the actor focused GlobalProtect portals with bruteforce and login makes an attempt, then pivoted to scanning SonicWall API endpoints, menace intelligence firm GreyNoise says in a report this week.
GlobalProtect is the VPN and distant entry element of Palo Alto Networks’ firewall platform, utilized by massive enterprises, authorities companies, and repair suppliers.
Supply: GreyNoise
In response to GreyNoise, the GlobalProtect login makes an attempt focused two profiles within the firm’s sensor community for passive seize of scanning and exploitation exercise.
The researchers say that the surge used three consumer fingerprints beforehand noticed in scanning makes an attempt recorded between late September and mid-October.
This previous exercise originated from 4 ASNs with no historical past of malicious exercise, producing over 9 million non-spoofable HTTP classes, principally concentrating on GlobalProtect portals.
In mid-November, GreyNoise additionally noticed exercise from 3xK Tech GmbH’s infrastructure probing GlobalProtect VPN portals with 2.3 million scan classes. Many of the attacking IPs (62%) had been situated in Germany, and used the identical TCP/JA4t fingerprints.
Based mostly on the analyzed indicators, the corporate confidently attributes each actions to the identical actor.
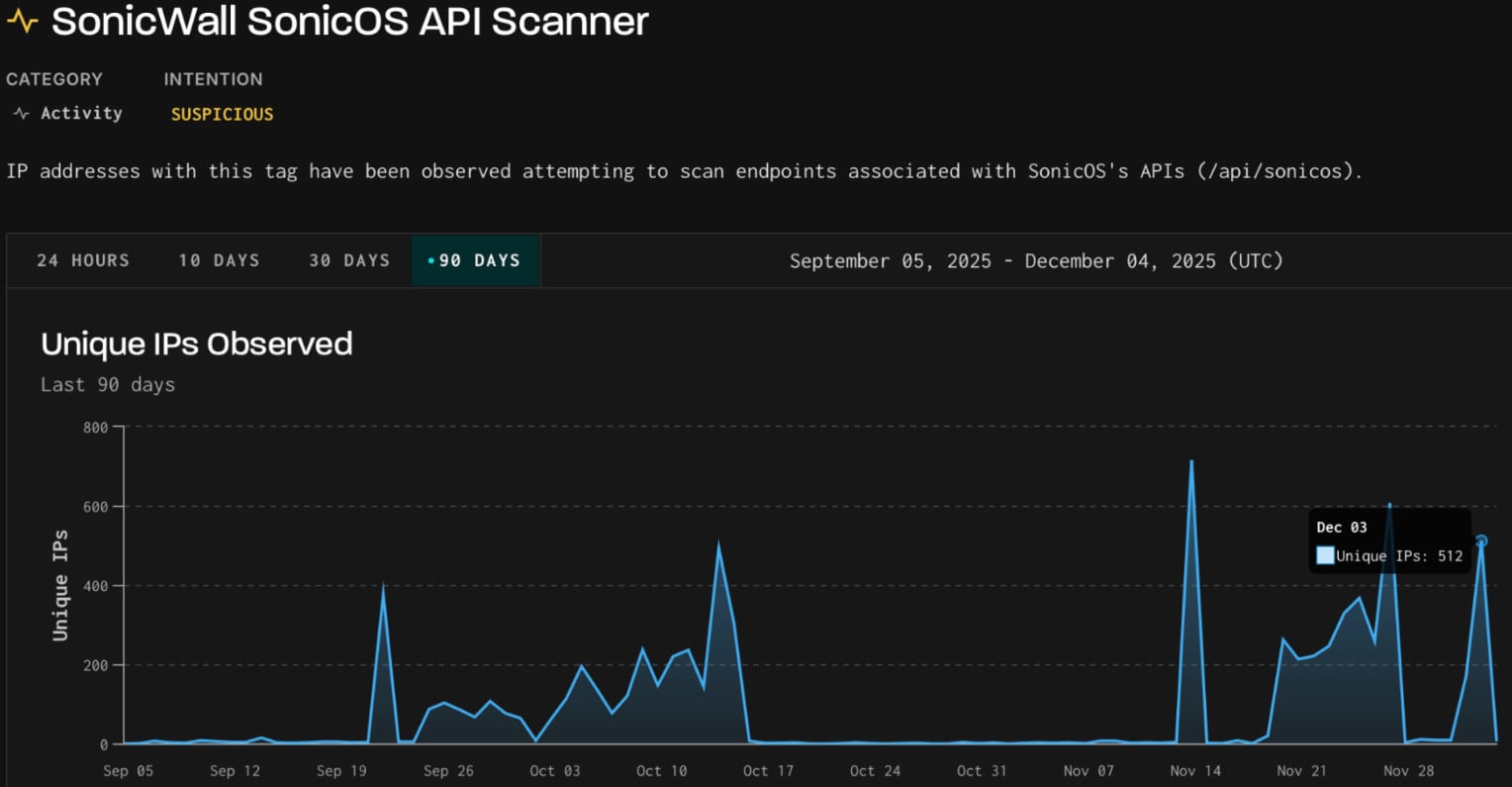
On December 3, the identical three fingerprints had been seen in scanning exercise concentrating on SonicWall SonicOS API.
Supply: GreyNoise
SonicOS is the working system operating on SonicWall firewalls, exposing API endpoints for configuration, distant administration, and monitoring.
Malicious scanning concentrating on these endpoints is often finished to establish vulnerabilities and misconfigurations. GreyNoise has beforehand famous that these scans might also assist uncover uncovered infrastructure in preparation for potential exploitation of upcoming flaws.
Because of this, defenders are suggested to observe for IPs related to one of these exercise and block them.
It is usually really helpful to observe authentication surfaces for irregular velocity/repeated failures, observe recurring consumer fingerprints, and use dynamic, context-aware blocking as a substitute of static fame lists.
BleepingComputer has contacted Palo Alto Networks and SonicWall about this exercise.
Palo Alto Networks mentioned that it detected elevated scanning geared toward GlobalProtect interfaces, and confirmed that it “represents credential-based assaults, not an exploit of a software program vulnerability.”
“Moreover, our inside telemetry and Cortex XSIAM safety verify this exercise doesn’t represent a compromise of our services or products,” the corporate instructed BleepingComputer.
Palo Alto Networks recommends prospects implement Multi-Issue Authentication (MFA) to guard in opposition to credential abuse.
Damaged IAM is not simply an IT drawback – the influence ripples throughout your entire enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with fashionable calls for, examples of what “good” IAM appears to be like like, and a easy guidelines for constructing a scalable technique.



