
A novel and complicated backdoor malware named ‘Deadglyph’ was seen utilized in a cyberespionage assault towards a authorities company within the Center East.
The Deadglyph malware is attributed to the Stealth Falcon APT (aka Mission Raven or FruityArmor), a state-sponsored hacking group from the United Arab Emirates (UAE).
The hacking group has been recognized for concentrating on activists, journalists, and dissidents for nearly a decade.
In a brand new report launched on the LABScon cybersecurity convention, ESET researcher Filip Jurčacko shares evaluation of the brand new modular malware and the way it infects Home windows gadgets.
Deadglyph assaults
ESET doesn’t have perception into the technique of preliminary an infection, however it’s suspected {that a} malicious executable, presumably a program installer, is used.
Nonetheless, ESET obtained many of the elements of the an infection chain to color an image of how the malware operates and makes an attempt to evade detection.
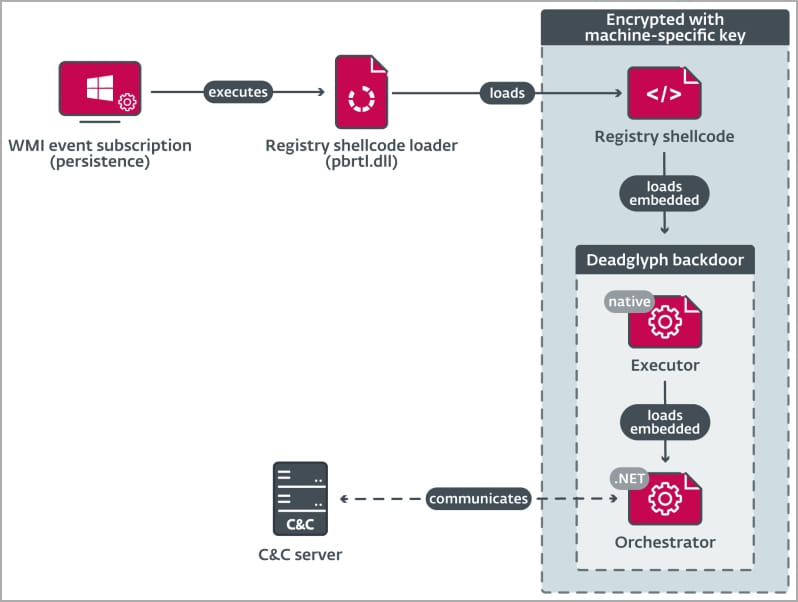
Deadglyph’s loading chain begins with a registry shellcode loader (DLL) that extracts code from the Home windows registry to load the Executor (x64) part, which in flip masses the Orchestrator (.NET) part.
Solely the preliminary part exists on the compromised system’s disk as a DLL file, minimizing the probability of detection.
ESET says the loader will load the shellcode from the Home windows Registry, which is encrypted to make evaluation tougher.
Because the DLL part is saved on the filesystem, it’s extra more likely to be detected. Because of this, the risk actors utilized a homoglyph assault within the VERSIONINFO useful resource utilizing distinct Greek and Cyrillic Unicode characters to imitate Microsoft’s info and seem as reliable Home windows file.
“We noticed a homoglyph assault mimicking Microsoft Company within the VERSIONINFO useful resource of this and different PE elements,” explains the ESET report.
“This methodology employs distinct Unicode characters that seem visually comparable, however on this case not equivalent, to the unique characters, particularly Greek Capital Letter San (U+03FA, Ϻ) and Cyrillic Small Letter O (U+043E, о) in Ϻicrоsоft Corpоratiоn.
The Executor part masses AES-encrypted configurations for the backdoor, initializes the .NET runtime on the system, masses the .NET a part of the backdoor, and acts as its library.
Lastly, the Orchestrator is answerable for command and management server (C2) communications, utilizing two modules for the duty, ‘Timer’ and ‘Community.’
If the backdoor fails to determine communications with the C2 server after a decided interval, it triggers a self-removal mechanism to stop its evaluation by researchers and cybersecurity specialists.
A modular malware
The Deadglyph malware is modular, that means it should obtain new modules from the C2 that include totally different shellcodes to be executed by the Executor part.
Utilizing a modular method permits the risk actors to create new modules as wanted to tailor assaults, which might then be pushed right down to victims to carry out extra malicious performance.
These modules have Home windows and customized Executor APIs at their disposal, with the latter providing 39 capabilities that make it doable to carry out file operations, load executables, entry Token Impersonation, and carry out encryption and hashing.
ESET believes there are 9 to 14 totally different modules however might solely receive three: a course of creator, an information collector, and a file reader.
The knowledge collector makes use of WMI queries to feed the Orchestrator with the next details about the compromised system:
- working system
- community adapters
- put in software program
- drives
- providers
- drivers
- processes
- customers
- setting variables
- safety software program
The method creator is a command execution software that executes specified instructions as a brand new course of and offers the outcome to the Orchestrator.
The file reader module reads the content material of information and passes it to the Orchestrator, whereas it additionally offers the operators the choice to delete the file after studying.
Though ESET was solely capable of uncover solely a fraction of the malware’s capabilities, it is clear that Stealth Falcon’s Deadglyph is a formidable risk.
With out detailed info relating to the preliminary an infection, providing particular protection methods towards the malware is not possible.
For now, defenders can depend on the present IoCs launched within the report.


