
A brand new ransomware-as-a-service model named Hunters Worldwide has emerged utilizing code utilized by the Hive ransomware operation, resulting in the legitimate assumption that the previous gang has resumed exercise below a unique flag.
This idea is supported by evaluation of the brand new encryptor revealing a number of code overlaps between the 2 ransomware gangs.
Hunters in denial
Safety researchers analyzing a pattern of the Hunters Worldwide malware found a placing resemblance to the code utilized in Hive ransomware assaults.
Extra particularly, malware analyst and reverse engineer rivitna, who first noticed the brand new encryptor, got here to the conclusion that Hunters Worldwide malware was a pattern of Hive ransomware model 6.
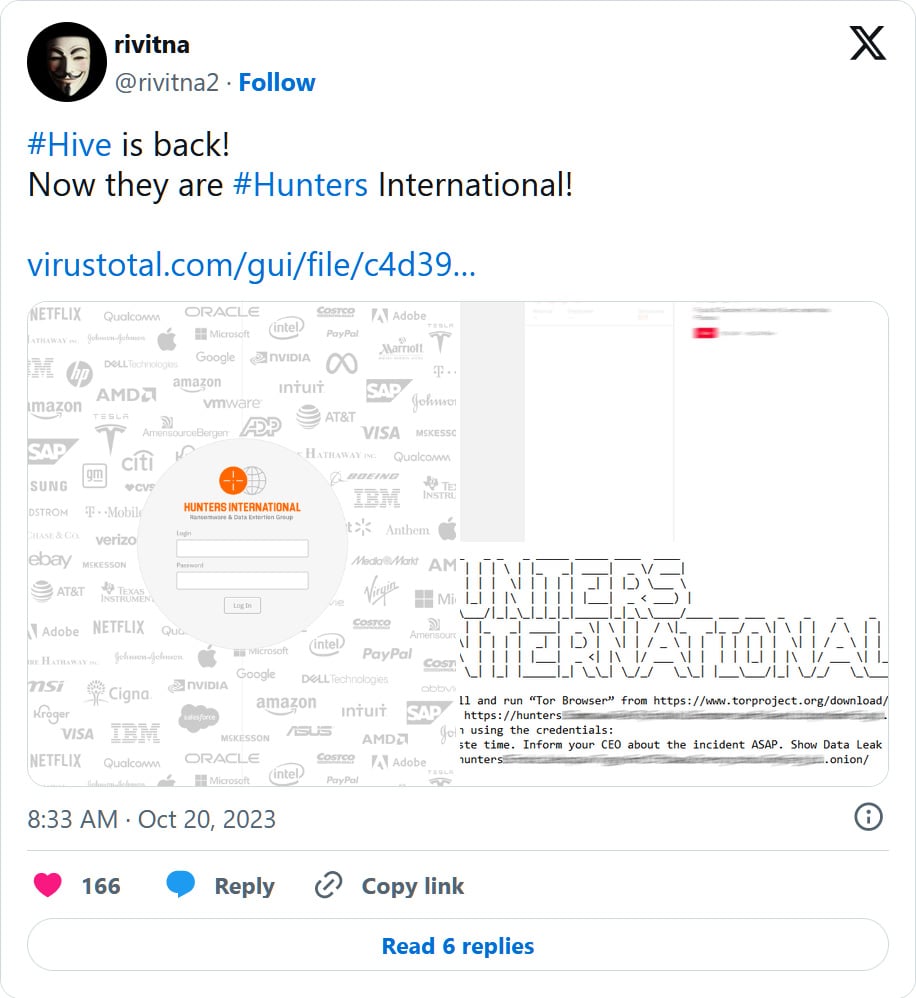
supply: rivitna
In replies to the tweet above, safety researcher Will Thomas shares that he discovered “some maintained Hive ransomware strings” within the Hunters Worldwide code.
Trying nearer on the Hunters Worldwide pattern, the researcher found code overlaps and similarities that match greater than 60% of the code in Hive ransomware.
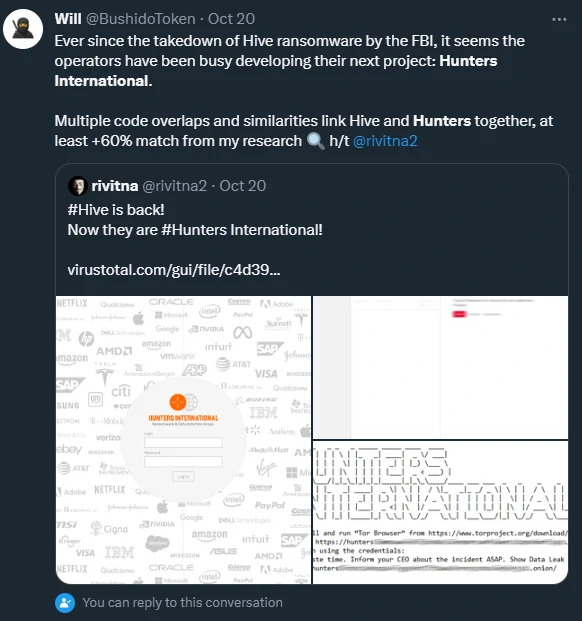
supply: Bushido Token
Nonetheless, the Hunters Worldwide group is denying the researchers’ “allegations” saying that they’re a brand new service on the ransomware scene who bought the encryptor supply code from the Hive builders.
“The entire Hive supply codes had been offered together with the web site and previous Golang and C variations and we’re those that bought them,” the Hunters Worldwide gang says.
Hive Worldwide claims that Hive’s code contained “quite a lot of errors that brought about unavailability for decryption in some circumstances” however they mounted it.
Moreover, the brand new gang says that encryption shouldn’t be the primary aim of their operation, as an alternative specializing in stealing information as leverage when extorting victims into paying a ransom demand.
The Hunters Worldwide encryptor
From evaluation by BleepingComputer, Hunters Worldwide’s encryptor appends the “.LOCKED” extension to the processed recordsdata.
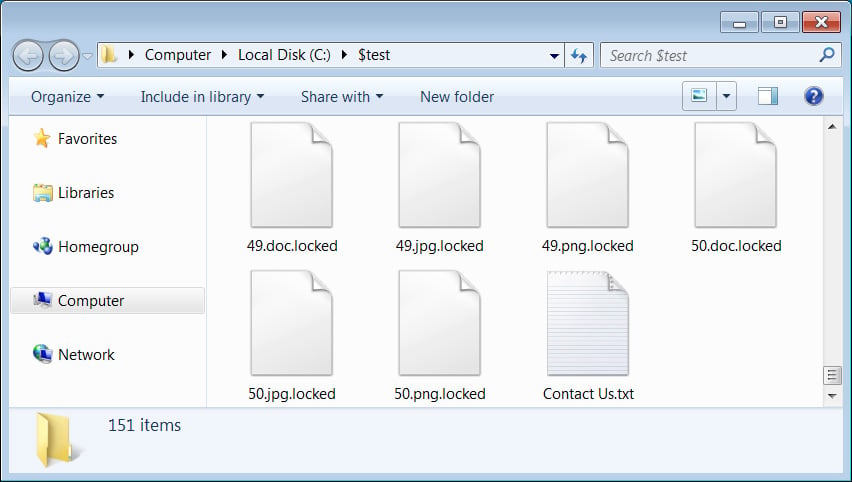
supply: BleepingComputer
The malware leaves in every listing a plaintext file named “Contact Us.txt” with directions for the sufferer to contact the attacker over Tor, by way of a chat web page that’s protected by a login particular for every sufferer.
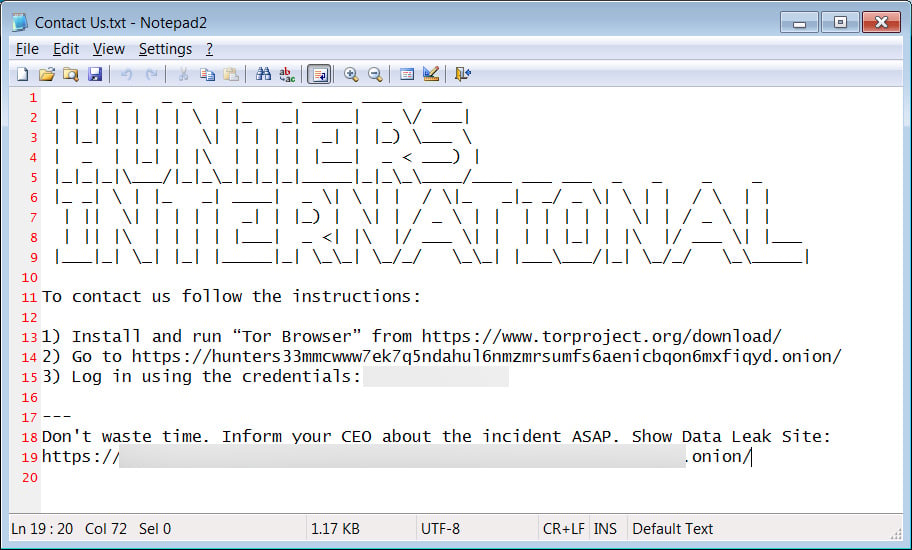
supply: BleepingComputer
In the meanwhile, their information leak website lists just one sufferer, a faculty within the UK, from the place the attackers declare to have stolen virtually 50,000 recordsdata consisting of knowledge about college students and lecturers together with community and net credentials.
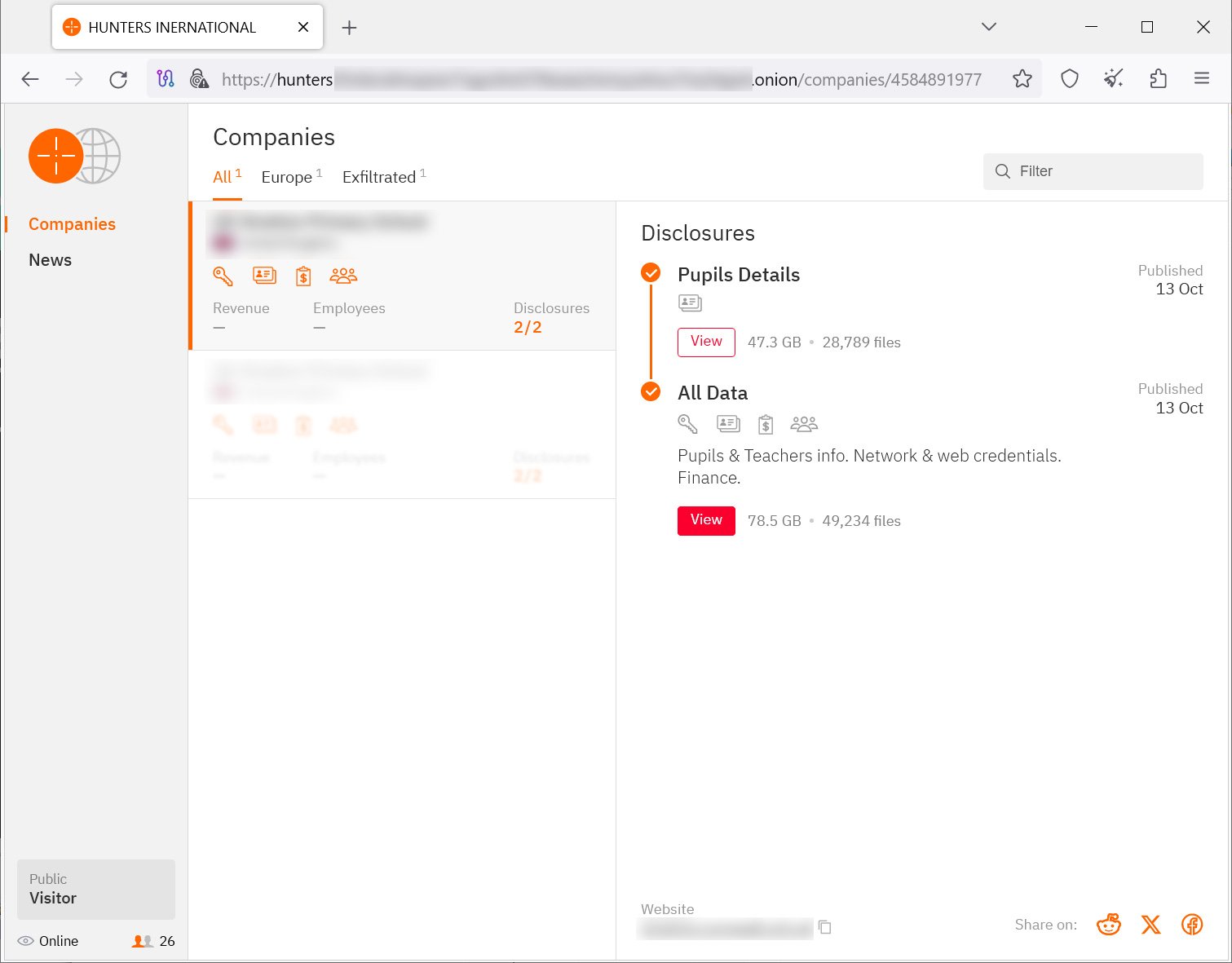
supply: BleepingComputer
As noticed by MalwareHunterTeam, Hunters Worldwide’s information leak website exhibits a set of messages, seemingly in an try to share with the world that they imply critical enterprise and “looking” for victims and extorting them is their major function.
It stays to be seen what destiny awaits Hunters Worldwide’s however with one sufferer printed on their information leak website, the group doesn’t look like too lively.
Hive ransomware’s demise
Whether or not Hive ransomware offered the supply code to different cybercriminals or not, stays unknown for the time being however the gang’s operations got here to a sudden cease after its Tor cost and information leak website had been seized in a world operation in January.
Disrupting the ransomware operation, which had 250 associates, was potential after the FBI had infiltrated the gang’s infrastructure and monitored the exercise for six months, since July 2022.
In response to the FBI, the gang breached greater than 1,300 firms and recived ransom funds of about $100 million.
The company’s exercise allowed it to offer greater than 1,300 decryption keys to Hive ransomware victims that had been encrypted earlier than and after the FBI gained entry to the attacker’s environments.


