
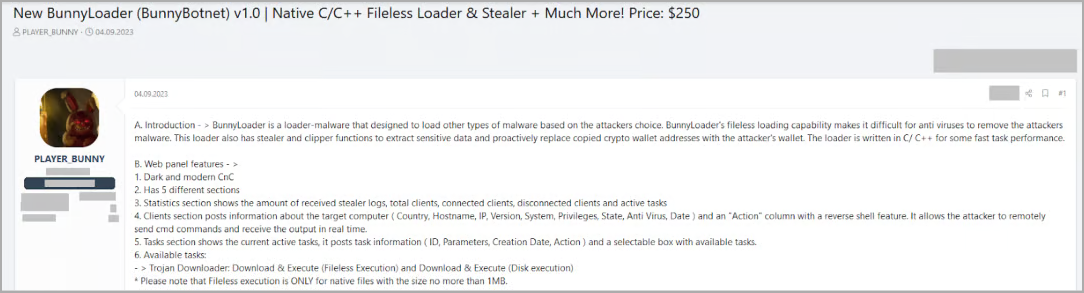
Safety researchers found a brand new malware-as-a-service (MaaS) named ‘BunnyLoader’ marketed on a number of hacker boards as a fileless loader that may steal and change the contents of the system clipboard.
The malware is underneath fast improvement, with updates including new options and bug fixes. It may well presently obtain and execute payloads, log keys, steal delicate knowledge and cryptocurrency, and execute distant instructions.
The primary model of BunnyLoader emerged on September 4. Since then, its builders added extra features, like a number of anti-detection mechanisms and additional info-stealing capabilities, releasing a second main model in direction of the tip of the month.
Researchers at cloud safety firm Zscaler word that BunnyLoader is rapidly turning into well-liked amongst cybercriminals as a feature-rich malware accessible for a low value.
BunnyLoader overview
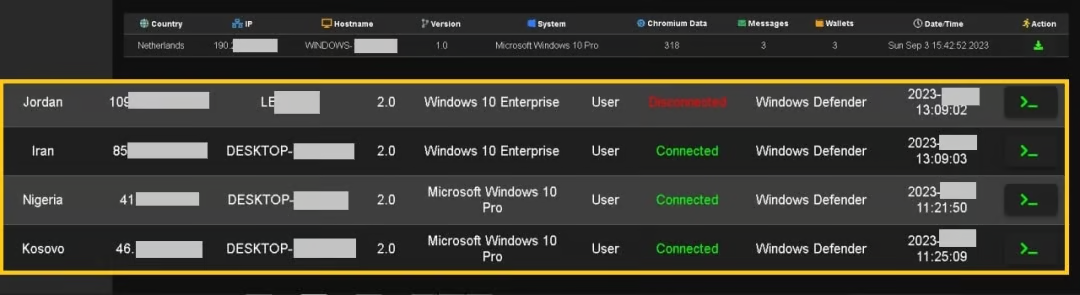
BunnyLoader’s command and management panel permits even low-skilled cybercriminals set a second-stage payload, allow keylogging, credential stealing, clipboard manipulation (for stealing cryptocurrency), and operating distant instructions on contaminated units.
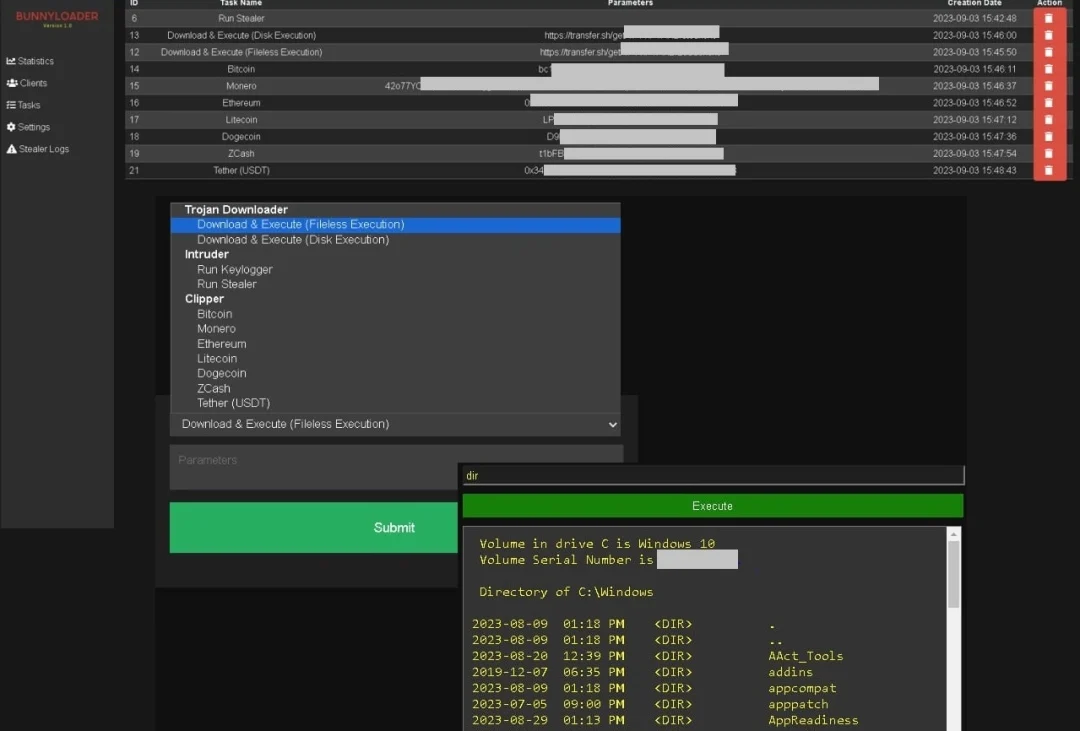
In a current report, researchers say that after being executed on a compromised machine, BunnyLoader creates a brand new worth in the Home windows Registry for persistence, hides its window, units a mutex to keep away from a number of situations of itself, and registers the sufferer into the management panel.
The malware performs a number of checks to find out if it is operating on a sandbox or simulated atmosphere and throws a faux structure incompatibility error if the result’s constructive.
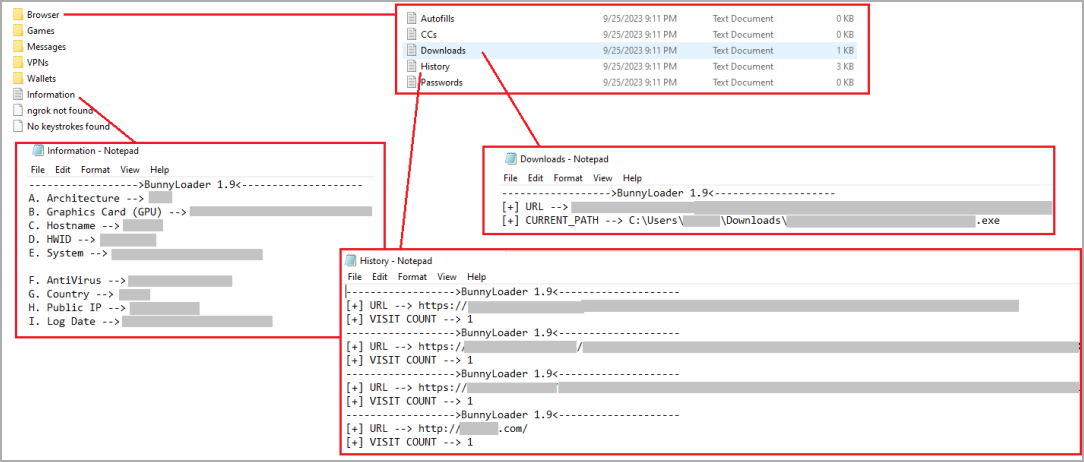
Aside from the talked about features, the malware additionally options modules to steal knowledge saved on net browsers (passwords, bank cards, shopping historical past), cryptocurrency wallets, VPNs, messaging apps, and extra, basically appearing as an ordinary info-stealer.
All stolen knowledge are compressed right into a ZIP archive earlier than they’re exfiltrated to the menace actor’s command and management (C2) server.
In line with the researchers, BunnyLoader helps writing payloads to the disk earlier than executing them, and also can run them from the system memmory (fileless) utilizing the method hollowing method.
Fast improvement
Zscaler monitored the malware’s improvement and bulletins on a number of hacking boards and seen that it went by way of quite a few updates since its preliminary launch.
This is a abstract of BunnyLoader’s improvement timeline:
- v1.0 (Sept 4): Preliminary launch.
- v1.1 (Sept 5): Fastened consumer bug, launched log compression earlier than add, and added ‘pwd’ command for reverse shell.
- v1.2 (Sept 6): Enhanced stealer with browser historical past restoration, NGRok auth-token restoration, and supported extra Chromium browser paths.
- v1.3 (Sept 9): Added bank card restoration for 16 card varieties and glued C2 bugs.
- v1.4 (Sept 10): Carried out AV evasion.
- v1.5 (Sept 11): Launched VPN restoration to stealer, fileless loader bug fixes, and log loading optimizations.
- v1.6 (Sept 12): Added downloads historical past viewer and anti-sandbox methods.
- v1.7 (Sept 15): Enhanced AV evasion.
- v1.8 (Sept 15): Carried out keylogger performance and resolved numerous bugs.
- v1.9 (Sept 17): Enhanced stealer with sport restoration, extra Chromium browser paths, and added a desktop pockets restoration.
- v2.0 (Sept 27): Up to date C2 GUI, mounted important vulnerabilities, together with SQL injection and XSS, launched exploit try detection, and additional optimized stealer and fileless loader functionalities.
In its present state, BunnyLoader is bought for $250, whereas the “non-public stub” model, which options stronger anti-analysis, in-memory injection, AV evasion, and extra persistence mechanisms, sells for $350.
This low value, mixed with the fast improvement cycle, make BunnyLoader a profitable selection for cybercriminals searching for early-bird offers on rising malware initiatives earlier than they achieve prominence and improve their charges.
Zscaler’s report gives technical particulars that may assist detect the malware earlier than it establishes persistence in addition to indicators of compromise that might forestall an an infection.


