The LostTrust ransomware operation is believed to be a rebrand of MetaEncryptor, using virtually similar knowledge leak websites and encryptors.
LostTrust started attacking organizations in March 2023 however didn’t turn out to be extensively identified till September, once they started using a knowledge leak web site.
Presently, the info leak web site lists 53 victims worldwide, with some having their knowledge leaked already for not paying a ransom.
It’s unclear if the ransomware gang solely targets Home windows gadgets or in the event that they make the most of a Linux encryptor as nicely.
A rebrand of MetaEncryptor
MetaEncryptor is a ransomware operation that’s believed to have launched in August 2022, amassing twelve victims on their knowledge leak web site by way of July 2023, after which no new victims had been added to the location.
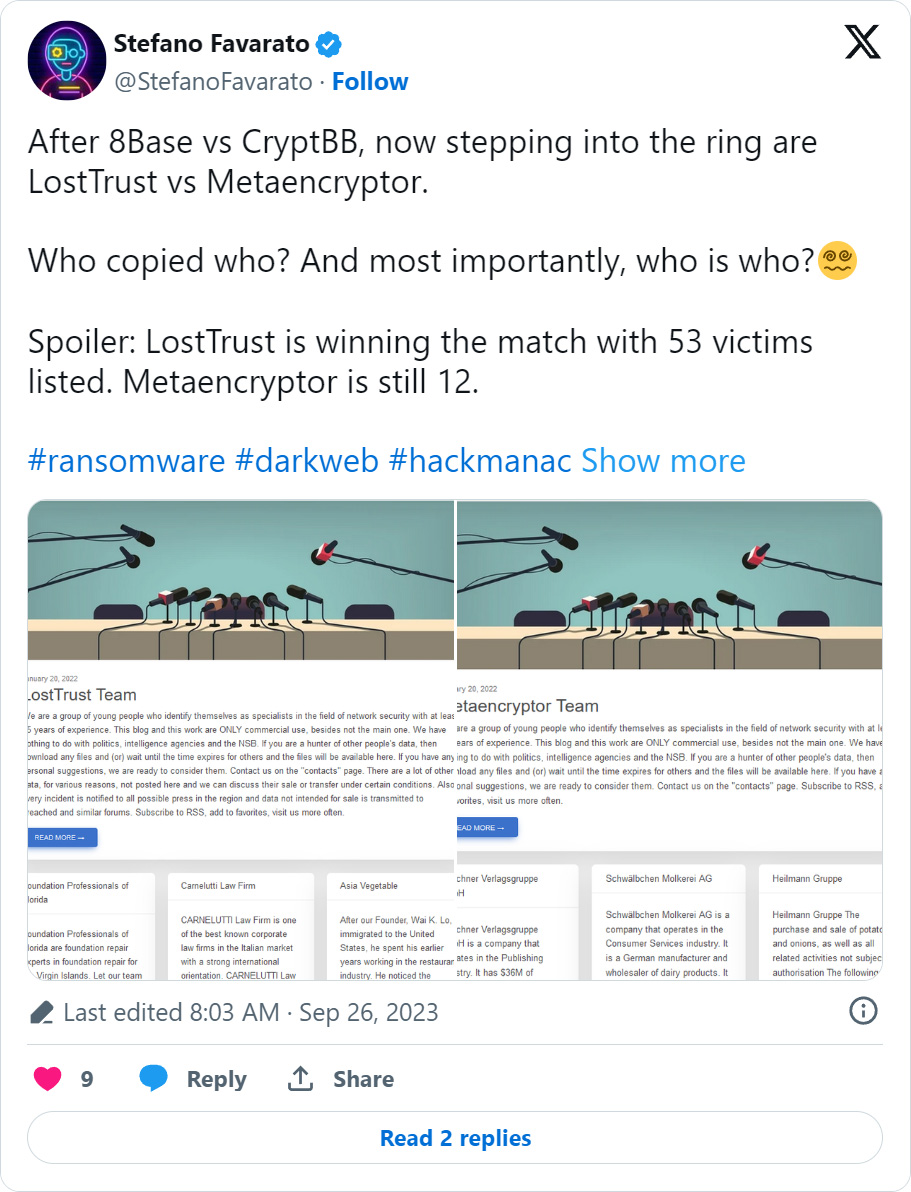
This month, a brand new knowledge leak web site for the ‘LostTrust’ gang was launched, with cybersecurity researcher Stefano Favarato rapidly noticing it makes use of the identical precise template and bio as MetaEncryptor’s knowledge leak web site.
“We’re a bunch of younger individuals who establish themselves as specialists within the subject of community safety with at the very least 15 years of expertise,” reads an outline on each the MetaEncryptor and LostTrust knowledge leak websites.
“This weblog and this work are ONLY industrial use, moreover not the primary one. We’ve nothing to do with politics, intelligence businesses and the NSB.”
BleepingComputer additionally discovered that each the LostTrust [VirusTotal] and MetaEncryptor [VirusTotal] encryptors are just about similar, with some minor adjustments to ransom notes, embedded public keys, ransom be aware names, and encrypted file extensions.
Moreover, cybersecurity researcher MalwareHunterTeam informed BleepingComputer that LostTrust and MetaEncryptor are based mostly on the SFile2 ransomware encryptor. This relation is additional backed up by an Intezer scan exhibiting numerous code overlap between the LostTrust and SFile encryptors.
Because of the vital overlap between the 2 operations, it’s believed that LostTrust is a rebrand of the MetaEncryptor operation.
The LostTrust encryptor
BleepingComputer discovered a pattern of the LostTrust encryptor and carried out a quick evaluation beneath.
The encryptor will be launched with two elective command line arguments, –onlypath (encrypt a selected path) and –enable-shares (encrypt community shares).
When launched, the encryptor will open a console displaying the present state of the encryption course of, as proven beneath.
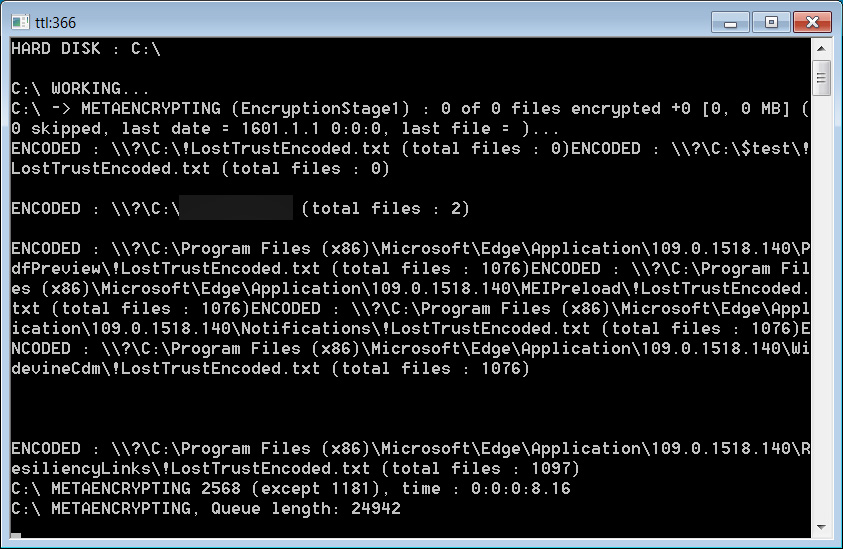
Supply:BleepingComputer
Word the ‘METAENCRYPTING‘ string within the encryptor, indicating it’s a modified MetaEncryptor encryptor.
When executed, LostTrust will disable and cease quite a few Home windows companies to make sure all recordsdata will be encrypted, together with any companies containing the Firebird, MSSQL, SQL, Trade, wsbex, postgresql, BACKP, tomcat, SBS, and SharePoint strings.
The encryptor may also disable and cease further companies related to Microsoft Trade.
When encrypting recordsdata, the encryptor will append the .losttrustencoded extension to encrypted file’s names, as illustrated beneath.
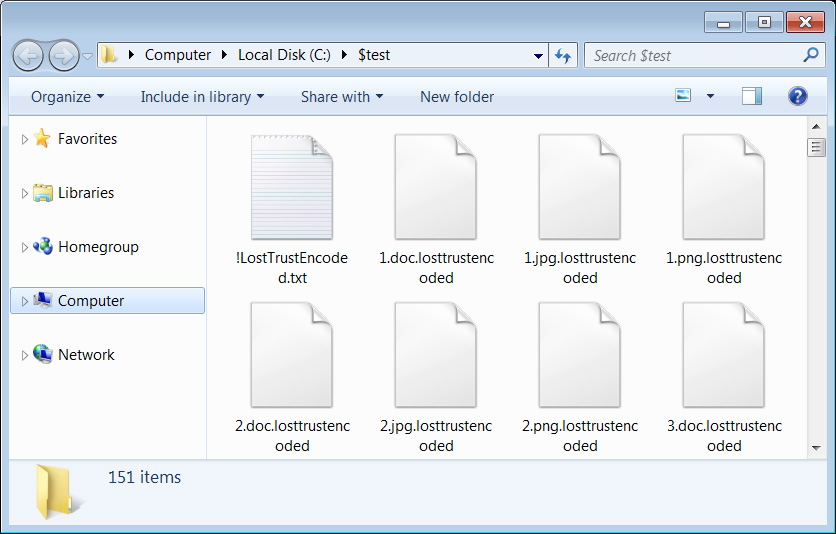
Supply: BleepingComputer
Ransom notes named !LostTrustEncoded.txt can be created in each folder on the machine, with the menace actors introducing themselves as prior white hat hackers. Nevertheless, after being poorly paid, they determined to modify to cybercrime.
“Our group has an in depth background in authorized and so known as white hat hacking. Nevertheless, purchasers often thought-about the discovered vulnerabilities to be minor and poorly paid for our companies,” reads the LostTrust ransom be aware.
“So we determined to vary our enterprise mannequin. Now you perceive how necessary it’s to allocate a superb funds for IT safety.”
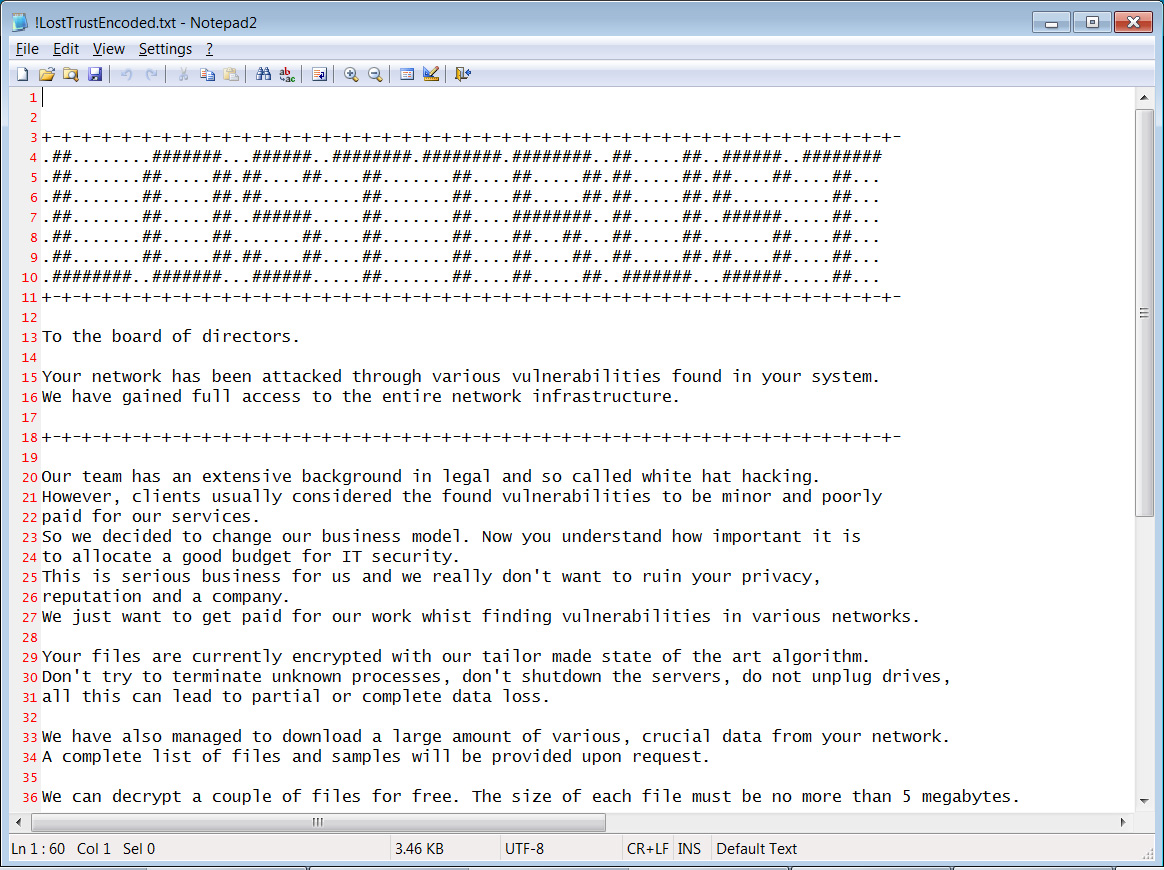
Supply: BleepingComputer
These ransom notes comprise data on what occurred to the corporate’s recordsdata and embrace a novel hyperlink to the ransomware gang’s Tor negotiation web site.
The negotiation web site is naked bones, with solely a chat characteristic permitting firm representatives to barter with the menace actors.
Supply: BleepingComputer
BleepingComputer was informed that ransom calls for for LostTrust assaults vary from $100,000 to tens of millions.
Information leak web site used to extort victims
Like different ransomware operations, LostTrust makes use of a Tor knowledge breach web site that’s used to extort firms by threatening to leak their stolen knowledge if a ransom is just not paid.
LostTrust has 53 victims on their knowledge leak web site, with some firms already having their knowledge leaked.
Supply: BleepingComputer
At the moment, it isn’t identified if paying a ransom demand will result in the deletion of knowledge and a working decryptor.