
A most severity vulnerability within the FreeScout helpdesk platform permits hackers to attain distant code execution with none consumer interplay or authentication.
The flaw is tracked as CVE-2026-28289 and bypasses a repair for an additional distant code execution (RCE) safety situation (CVE-2026-27636) that may very well be exploited by authenticated customers with add permissions.
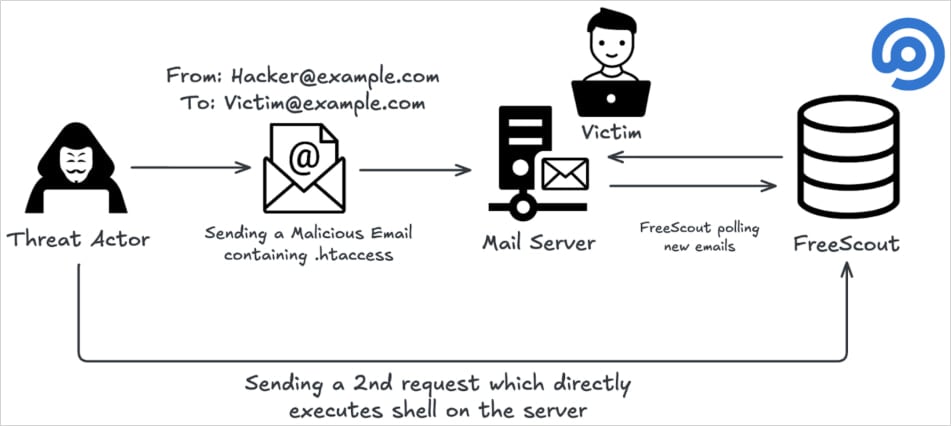
Researchers at OX Safety, an organization that secures functions from code to runtime, say that an attacker can exploit the brand new vulnerability by “sending a single crafted e mail to any deal with configured in FreeScout.”
In accordance with them, the repair tried to dam harmful file uploads by modifying filenames with restricted extensions or these beginning with a dot.
The OX Analysis crew found {that a} zero-width area (Unicode U+200B) may very well be positioned earlier than the filename to bypass the just lately launched validation mechanism, for the reason that character is just not handled as seen content material.
Subsequent processing removes that character, permitting the file to be saved as a dotfile, and therefore, nonetheless triggering CVE-2026-27636 exploitation by fully bypassing the newest safety checks.
Supply: OX Analysis
Making issues worse, CVE-2026-28289 could be triggered by a malicious e mail attachment delivered to a mailbox configured in FreeScout, the researchers say.
This system shops the attachment in “/storage/attachment/…,” enabling the attacker to entry the uploaded payload by the online interface and execute instructions on the server with out authentication or consumer interplay, making it a zero-click vulnerability.
“A patch bypass vulnerability in FreeScout 1.8.206 permits any authenticated consumer with file add permissions to attain Distant Code Execution (RCE) on the server by importing a malicious .htaccess file utilizing a zero-width area character prefix to bypass the safety verify,” the seller says in a safety bulletin.
FreeScout is an open-source assist desk and shared mailbox platform utilized by organizations to handle buyer assist emails and tickets. It’s a self-hosted different to Zendesk or Assist Scout.
The challenge’s GitHub repository has 4,100 stars and over 620 forks, and OX Analysis experiences that its Shodan scans returned 1,100 publicly uncovered cases, indicating it’s a broadly used answer.
CVE‑2026‑28289 impacts all FreeScout variations as much as and together with 1.8.206 and was patched in model 1.8.207, launched 4 days in the past.
The FreeScout crew warned that profitable exploitation of CVE‑2026‑28289 might end in full server compromise, knowledge breaches, lateral motion into inside networks, and repair disruption. Therefore, quick patching is suggested.
OX Analysis has additionally beneficial disabling ‘AllowOverrideAll’ within the Apache configuration on the FreeScout server, even when on model 1.8.207.
No energetic exploitation of CVE‑2026‑28289 has been noticed within the wild as of scripting this, however given the character of this flaw, the hazard of malicious exercise beginning quickly could be very excessive.



