Hackers have stolen $4.4 million in cryptocurrency on October twenty fifth utilizing non-public keys and passphrases saved in stolen LastPass databases, based on analysis by crypto fraud researchers who’ve been researching related incidents.
The information comes from ZachXBT and MetaMask developer Taylor Monahan, who’ve been monitoring these crypto thefts.
“We frequently have individuals attain out by way of DM who’ve had their crypto property stolen. We additionally method victims we uncover on-chain,” ZachXBT advised BleepingComputer.
“We ask potential LastPass victims a number of questions and usually have discovered one commonality between all of them being LastPass.”
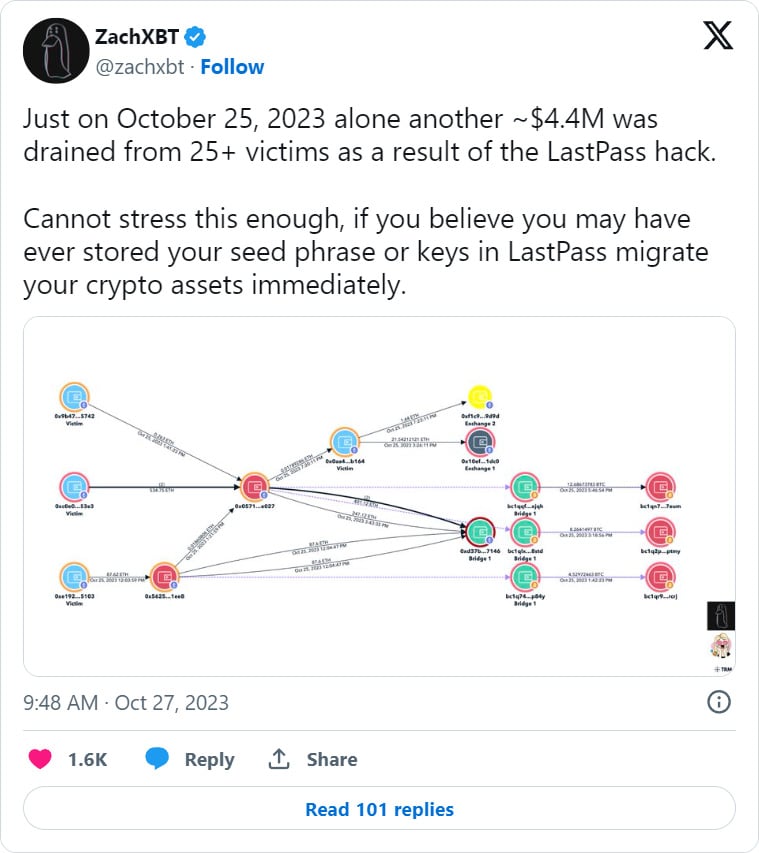
In keeping with a tweet by ZachXBT on X, the risk actors stole $4.4 million from 25+ victims because of a LastPass breach in 2022.
The LastPass breach
In 2022, LastPass suffered two breaches that finally allowed risk actors to steal supply code, buyer knowledge, and manufacturing backups saved in cloud providers that included encrypted password vaults.
On the time, LastPass CEO Karim Toubba mentioned that whereas the encrypted vaults had been stolen, solely prospects knew the grasp password required to decrypt them.
Due to this fact, in the event you had been following password finest practices really helpful by LastPass, your vaults needs to be secure.
Nevertheless, LastPass warned that for these utilizing weaker passwords, it was suggested to reset the grasp password.
“Relying on the size and complexity of your grasp password and iteration depend setting, you could wish to reset your grasp password,” reads a LastPass help bulletin concerning the cyberattack.
This suggestion was given as a result of a weaker password can extra simply be cracked utilizing specialised applications that make the most of a GPU to brute power easy-to-crack passwords.
In keeping with analysis carried out by Monahan and ZachXBT, it’s believed that the risk actors are cracking these stolen password vaults to achieve entry to saved cryptocurrency pockets passphrases, credentials, and personal keys.
As soon as they acquire entry to this data, they’ll load the wallets onto their very own gadgets and drain them of all funds.
In keeping with a report by Brian Krebs on this analysis, Monahan and different researchers have generated a novel signature that hyperlinks the theft of over $35 million to the identical risk actors.
“At this level I am additionally assured in saying that, in most of those instances, the compromised keys had been stolen from LastPass,” tweeted Monahan in August.
“The variety of victims who solely had the particular group of seeds/keys that had been drained saved in LastPass is just too a lot to disregard.”
It’s turning into more and more clear that the risk actors behind the LastPass assault have efficiently cracked the passwords for vaults and are utilizing the stolen data to gasoline their very own assaults.
Due to this fact, if you’re a LastPass person who had an account throughout the August and December 2022 breaches, it’s strongly instructed that you just reset all your passwords, together with your password.