
Knowledge-wiping assaults have gotten extra frequent on Israeli computer systems as researchers found variants of the BiBi malware household that destroys knowledge on each Linux and Home windows techniques.
Over the weekend, Israel’s CERT revealed an alert with guidelines that would assist organizations establish or forestall the risk actors’ exercise.
The assaults are half of a bigger cyber offensive that targets Israeli organizations, together with within the training and know-how sectors.
The company recommends organizations to make use of the supplied identifiers for all company safety techniques (e.g. safety data and occasion administration – SIEM, Endpoint Detection and Response (EDR), and antivirus).
The federal government additionally asks corporations to tell the nationwide cyber system in the event that they discover a number of identifiers on the company hosts.
An evaluation of the assaults from researchers at Palo Alto Networks Unit42 attributes the information wiping assaults to a risk actor that has “sturdy connections to an Iranian-backed APT group” tracked as Agonizing Serpens (a.okay.a. Agrius, BlackShadow, Pink Sandstorm, and DEV-0022).
Wiper malware disables restoration choices
Variations of the BiBi wiper was seen in late October by researchers at cybersecurity corporations ESET and SecurityJoes, who famous that it was launched by pro-Hamas hacktivists.
‘BiBi-Linux’ was found by the Safety Joes’ Incident Response group, who reported on October 30 that it was possible deployed by pro-Hamas hacktivists to trigger irreversible knowledge corruption and operational disruption.
ESET researchers introduced the subsequent day that they found the Home windows variant of the malware being deployed by a Hamas-backed hacktivist group they monitor as BiBiGun.
The malware achieves its aim by merely overwriting information and there’s no knowledge exfiltration, encryption, or a ransom demand concerned.
On Friday, BlackBerry’s risk intelligence group revealed a technical evaluation of the Home windows variant for the BiBi-Linux malware. The researchers discovered the variant a day after SecurityJoes posted their findings on the brand new Linux wiper.
The malware is packed in a small 203KB 64-bit executable. When launched, it profiles the host’s processor to find out the variety of threads it could possibly leverage for quick data-wiping assaults, supporting as much as 12 threads on eight cores. The same multi-thread and queuing logic was seen within the Linux variant.
In line with the researchers, the risk actor used the straightforward right-to-left method to bypass sample detection guidelines which are frequent in legacy antivirus merchandise.
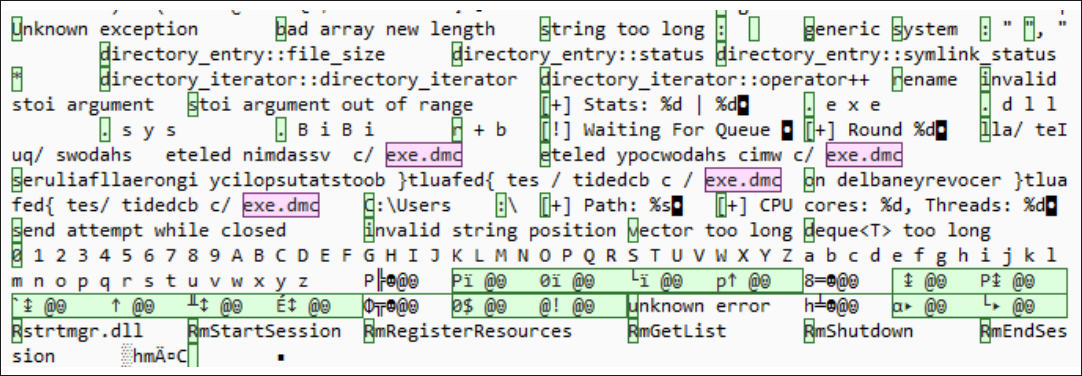
BiBi for Home windows targets all file sorts apart from .EXE, .DLL, and .SYS information, possible as a result of destroying them would render the pc unusable, and the hacktivists would not be capable to relay their message.
The focused information have their content material overwritten with random bytes to make them unrecoverable, and are renamed utilizing a ten-character lengthy sequence of random letters adopted by an alphanumerical extension containing the “BiBi” string.
For instance, a file initially named “doc.txt” is likely to be renamed to “asdzxcqwer.BiBi3” after the malware assault.
This course of is unpredictable, obscuring the unique filenames and additional complicating knowledge restoration efforts.
To forestall straightforward system restoration, the malware additionally deletes the shadow copies that maintain system snapshots from an earlier state and are sometimes used to get well knowledge and settings.
Moreover, BiBi turns off the ‘Error Restoration’ mode on system boot and deactivates the ‘Home windows Restoration’ function.
BlackBerry says that the preliminary an infection vector stays unknown on the time.
Safety Joes posted a brand new, extra complete report late final week, wanting deeper into the marketing campaign and the Karma hacktivist group chargeable for its orchestration.
The report presents some overlaps of Karma with beforehand identified Iranian hacktivist teams akin to ‘Moses Employees,’ beforehand identified for launching ransom-less knowledge encrypting assaults.
SecurityJoes and BlackBerry present YARA guidelines [1, 2] for detecting the 2 presently identified variants of the BiBi wiper together with hashes for the 2 executables. One other set of identifiers [TXT, CVS] for the BiBi risk exercise is offered from Israel’s CERT authority.


