
Phishing stays one among cybersecurity’s most enduring threats, not as a result of defenders aren’t evolving, however as a result of attackers are adapting even sooner.
Right this moment’s only campaigns aren’t simply constructed on spoofed emails or shady domains. They exploit one thing way more insidious: belief within the instruments and companies we use day by day, resulting in zero-hour phishing.
The Rise of ChainLink Phishing
Conventional phishing relied on simply identifiable pink flags comparable to suspicious senders and questionable URLs. However trendy phishing has matured.
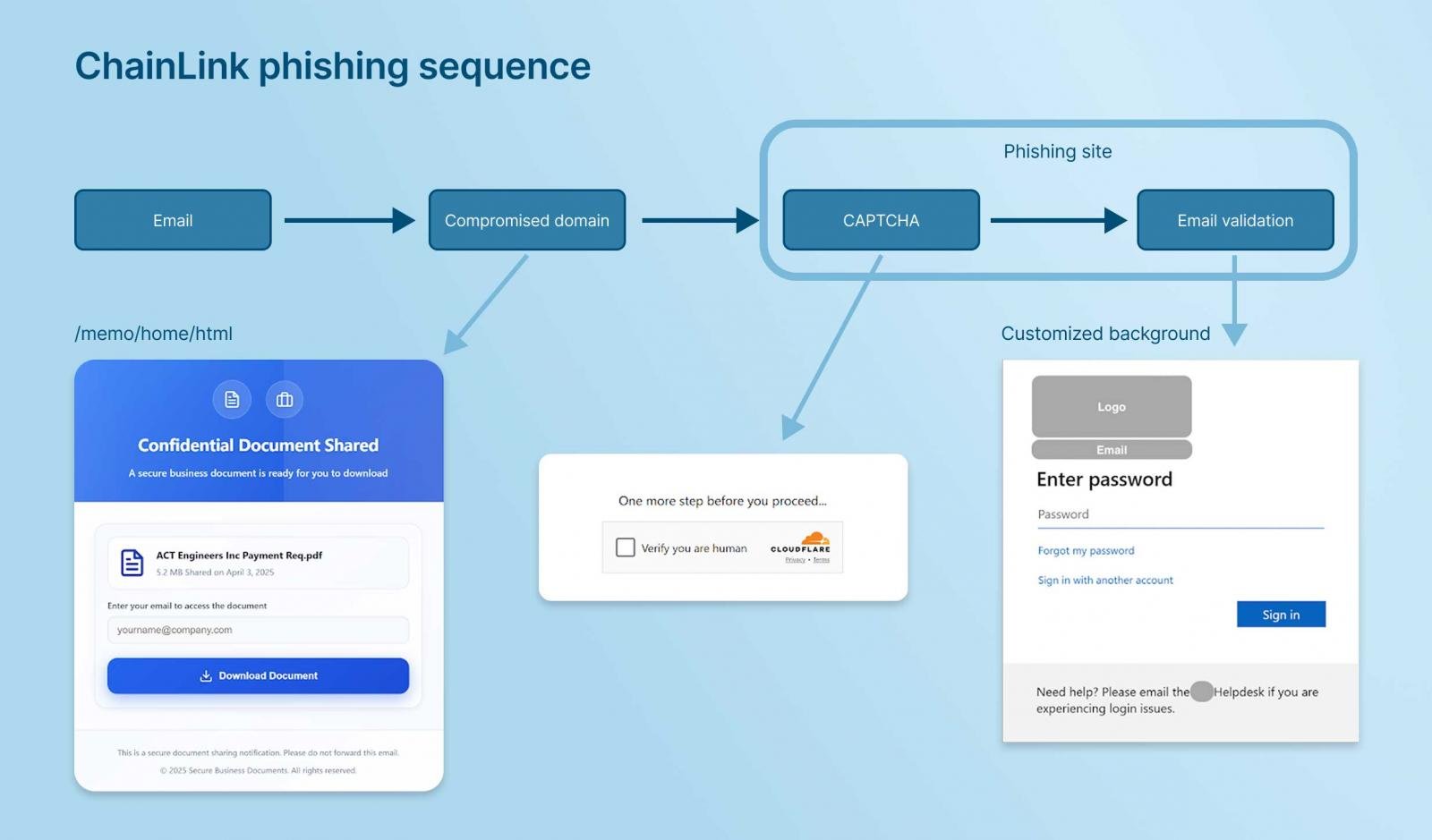
Attackers now deploy chained sequences, funneling a sufferer from electronic mail by way of trusted infrastructure earlier than harvesting credentials.
An worker would possibly obtain a hyperlink from what seems to be Google Drive or Dropbox. At first look, there’s nothing uncommon. However after the preliminary click on, the person is quietly routed by way of a sequence of prompts, every wanting credible on respected websites, till they unknowingly hand over business-essential credentials to an attacker.
This method, which we name ChainLink Phishing, depends on leveraging the respectable platforms and respected domains that enterprise instruments permit and that IT safety groups are oblivious to.
Preserve Conscious stops phishing assaults in real-time the place they begin: contained in the browser.
By analyzing person conduct, kind submissions, and web site context, not simply URLs, Preserve Conscious shuts down threats earlier than credentials ever depart the web page. Equip your safety staff with exact visibility, coverage enforcement, and quick risk response all from inside the current internet browsers throughout the group.
Why These Assaults Are So Efficient
The browser has turn out to be the middle of the data employee’s universe. From code opinions to HR duties, almost each motion begins and ends in a browser tab.
This centralization provides attackers a singular floor to use, but it has been vastly underprotected.
Even probably the most security-aware workers could be deceived when a hyperlink seems to return from a recognized area and follows the anticipated conduct. The person typically believes they’re participating in regular exercise till it’s too late.
Through the use of respectable hyperlinks, passing electronic mail authentication checks, and even inserting CAPTCHAs alongside the way in which, attackers sidestep conventional defenses and allow zero-hour phishing to succeed undetected.
CAPTCHAs and verification steps at the moment are so widespread in on a regular basis searching that attackers exploit them as social engineering ways, not solely in phishing campaigns, but in addition in different browser-based threats like ClickFix.
“Identified Good” Is No Longer Secure
This shift highlights a painful fact: “recognized good” is now not a dependable safety sign. In reality, it’s turn out to be the right disguise for dangerous actors.
To really tackle threats like ChainLink Phishing, we have to transfer past static blocklists and domain-based filtering. The way forward for phishing safety lies in real-time evaluation of internet pages and customers’ interactions with them.

When the Safety Stack Can’t See the Menace
A phishing hyperlink that originates from a trusted service will typically sail previous electronic mail and community filters. Site visitors to the phishing web site is allowed unimpeded as a result of the area isn’t on an intel feed and its status is undamaged. And since no malware is deployed, simply credential harvesting, endpoint instruments don’t have anything to detect.
Regardless of having layered defenses like:
- Safe electronic mail gateways (SEGs)
- DNS filtering
- Safe internet gateways (SWGs)
- EDR/AV
- Native browser protections
… Most organizations stay weak. Why? As a result of these instruments are designed to dam recognized malicious internet conduct and endpoint options are oblivious to credential-harvesting internet kinds. The refined misuse of respectable domains, mixed with further evasive methods, results in customers falling sufferer to zero-hour phishing.
Defend The place Phishing Actually Strikes
These sequenced assaults exploit trusted pathways, main customers to phishing websites that simply bypass conventional defenses. By the point credentials are entered, it’s typically too late—and most organizations by no means noticed it coming. To successfully mitigate these threats, safety must shift to the place the danger materializes: the browser. It’s time to cease phishing on the root supply, not simply on the perimeter.
To grasp how these chained phishing sequences work, and find out how to detect and cease them earlier than harm is finished, watch Preserve Conscious’s newest on-demand webinar:
ChainLink Phishing: The Chained Sequences of Trendy Phishing
Sponsored and written by Preserve Conscious.


