The Glassworm marketing campaign, which first emerged on the OpenVSX and Microsoft Visible Studio marketplaces in October, is now in its third wave, with 24 new packages added on the 2 platforms.
OpenVSX and the Microsoft Visible Studio Market are each extension repositories for VS Code–suitable editors, utilized by builders to put in language assist, frameworks, tooling, themes, and different productiveness add-ons.
The Microsoft market is the official platform for Visible Studio Code, whereas OpenVSX is an open, vendor-neutral various utilized by editors who cannot or do not use Microsoft’s proprietary retailer.
First documented by Koi Safety on October 20, Glassworm is a malware that makes use of “invisible Unicode characters” to cover its code from evaluate.
As soon as builders set up it of their environments, it makes an attempt to steal GitHub, npm, and OpenVSX accounts, in addition to cryptocurrency pockets information from 49 extensions.
Furthermore, the malware deploys a SOCKS proxy to route malicious visitors by means of the sufferer’s machine and installs the HVNC consumer to provide operators stealthy distant entry.
Though the preliminary an infection was cleaned from the extension repositories, the malware returned to each websites shortly after with new extensions and writer accounts.
Previous to this, Open VSX had declared the incident absolutely contained, with the platform rotating compromised entry tokens.
The re-emergence of Glassworm was found by Safe Annex’s researcher, John Tuckner, who stories that the package deal names point out a broad concentrating on scope masking common instruments and developer frameworks like Flutter, Vim, Yaml, Tailwind, Svelte, React Native, and Vue.
Supply: Safe Annex
Safe Annex has now discovered that the third wave makes use of the packages listed under.
VS Market
- iconkieftwo.icon-theme-materiall
- prisma-inc.prisma-studio-assistance
- prettier-vsc.vsce-prettier
- flutcode.flutter-extension
- csvmech.csvrainbow
- codevsce.codelddb-vscode
- saoudrizvsce.claude-devsce
- clangdcode.clangd-vsce
- cweijamysq.sync-settings-vscode
- bphpburnsus.iconesvscode
- klustfix.kluster-code-verify
- vims-vsce.vscode-vim
- yamlcode.yaml-vscode-extension
- solblanco.svetle-vsce
- vsceue.volar-vscode
- redmat.vscode-quarkus-pro
- msjsdreact.react-native-vsce
Open VSX
- bphpburn.icons-vscode
- tailwind-nuxt.tailwindcss-for-react
- flutcode.flutter-extension
- yamlcode.yaml-vscode-extension
- saoudrizvsce.claude-dev
- saoudrizvsce.claude-devsce
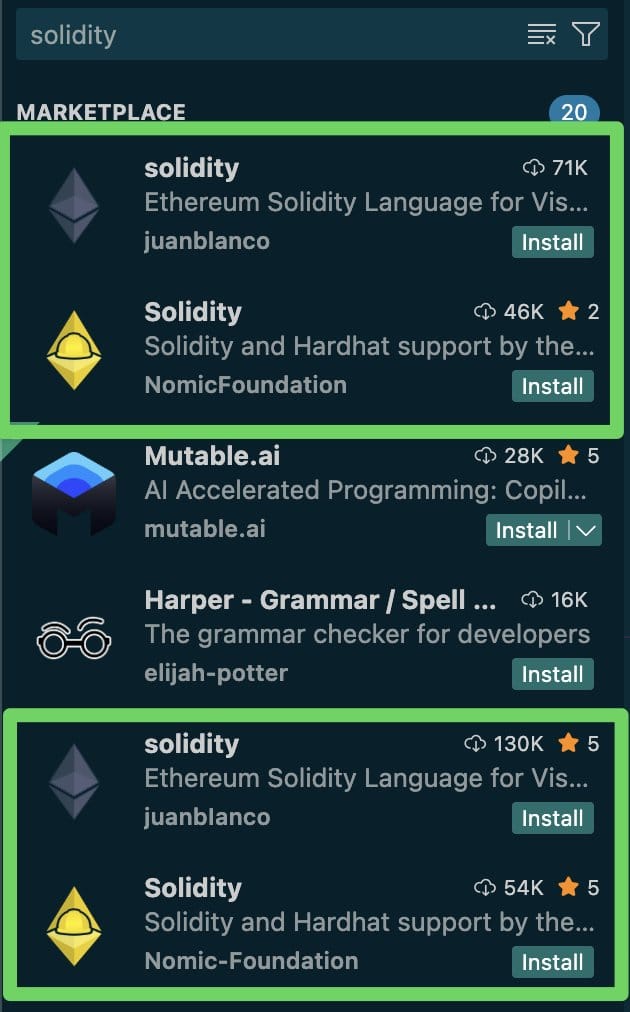
- vitalik.solidity
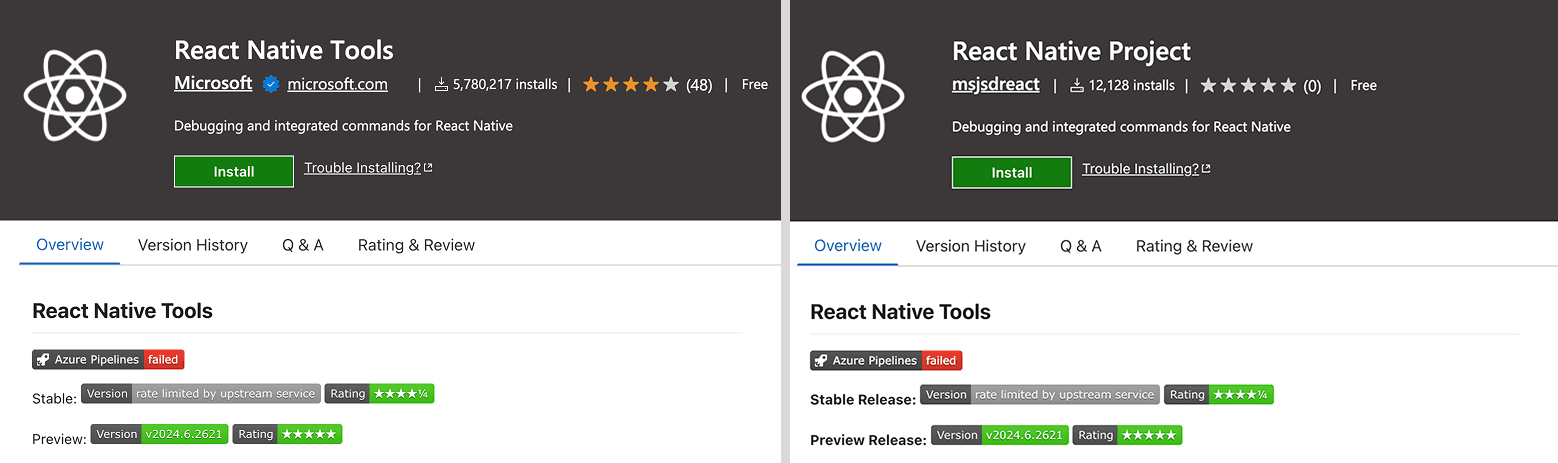
As soon as the packages are accepted on the marketplaces, the publishers push an replace that introduces the malicious code, then inflate their obtain counts to make them seem authentic and reliable.
Additionally, artificially rising obtain counts can manipulate search outcomes, with the malicious extension showing increased within the outcomes, typically very near the authentic initiatives it impersonates.
Supply: Safe Annex
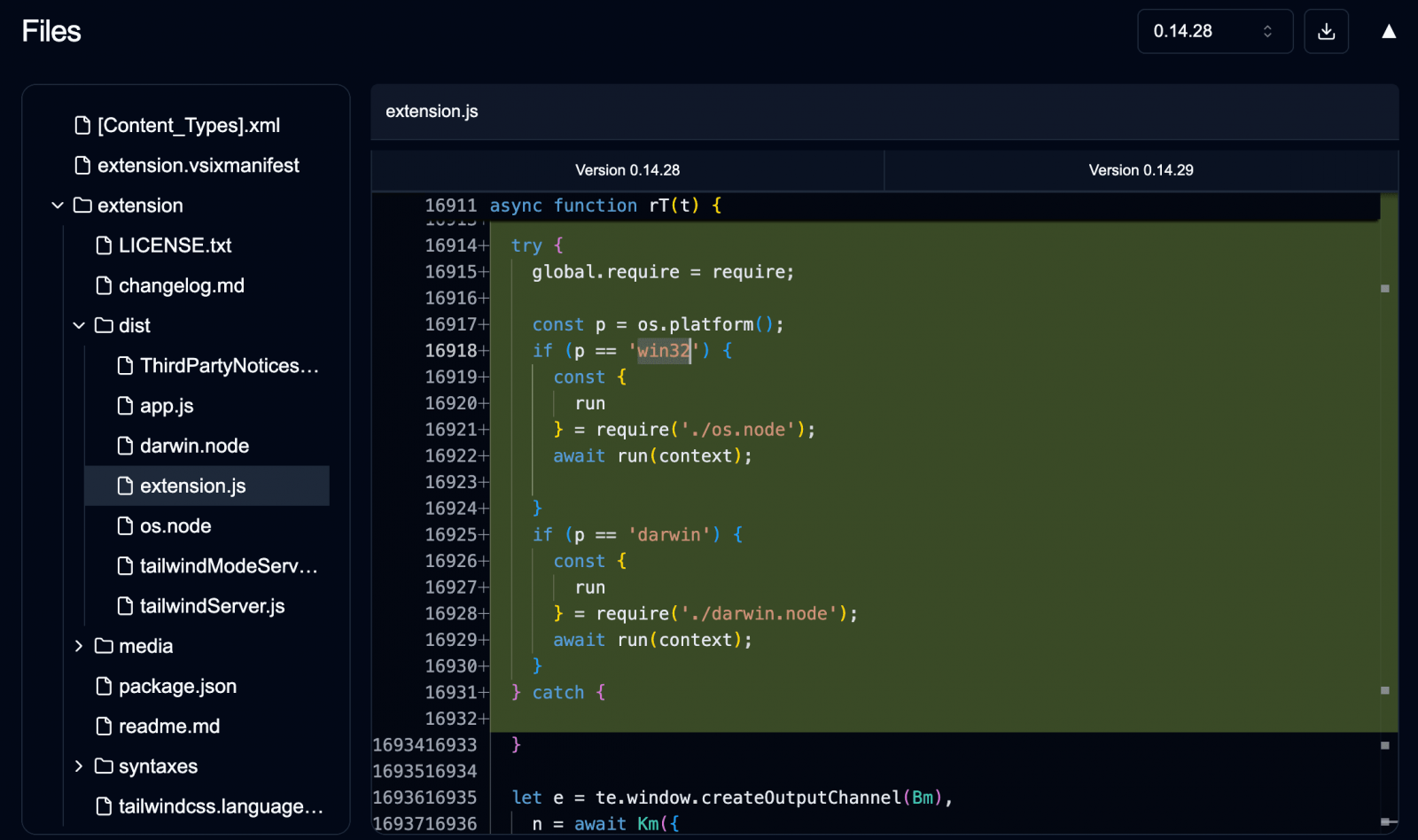
The researcher stories that Glassworm has advanced on the technical aspect as nicely, now utilizing Rust-based implants packaged contained in the extensions. The invisible Unicode trick can also be nonetheless utilized in some circumstances.
Supply: Safe Annex
BleepingComputer has contacted each OpenVSX and Microsoft relating to Glassworm’s continued potential to bypass their defenses, and we’ll replace this put up with their responses as soon as obtained.
Replace 12/2 – Microsoft despatched BleepingComputer the next assertion:
“We proceed to evaluate and enhance our scanning and detections to stop abuse. Microsoft encourages customers to flag suspicious content material by means of a “Report Abuse” hyperlink discovered on each extension web page.”
Damaged IAM is not simply an IT drawback – the influence ripples throughout your complete enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with trendy calls for, examples of what “good” IAM appears to be like like, and a easy guidelines for constructing a scalable technique.



