
A not too long ago found worm that researchers name LittleDrifter has been spreading over USB drives infecting methods in a number of nations as a part of a marketing campaign from the Gamaredon state-sponsored espionage group.
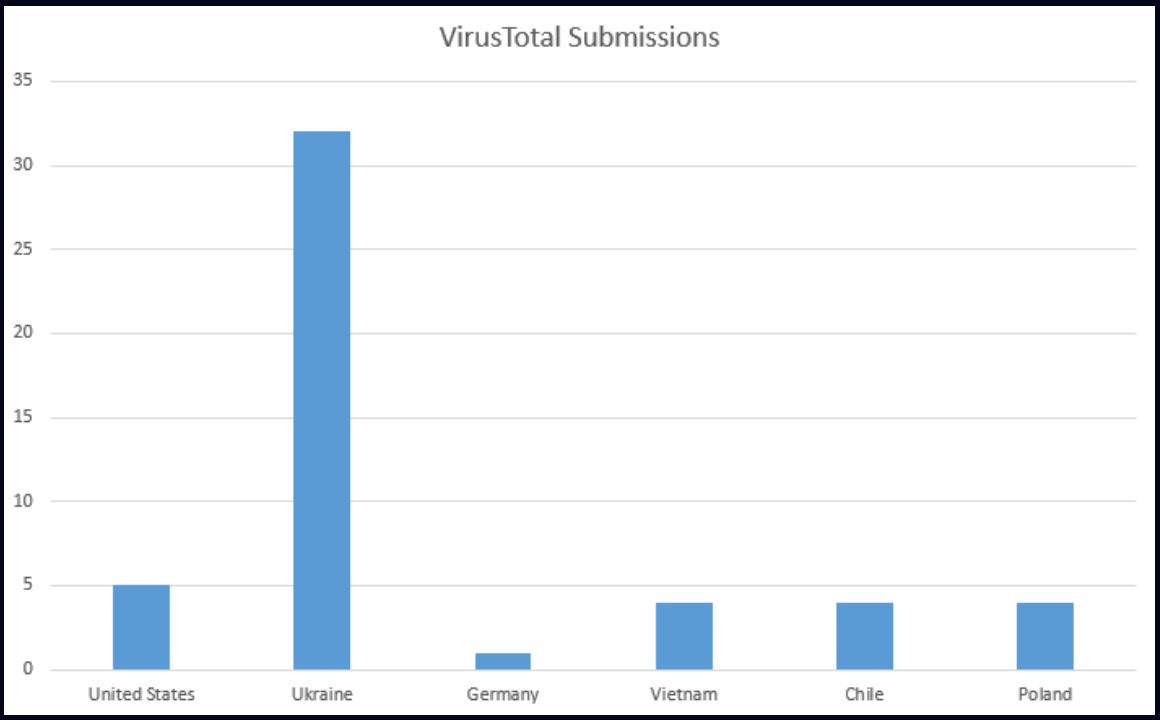
Malware researchers noticed indications of compromise in the US, Ukraine, Germany, Vietnam, Poland, Chile, and Hong Kong, which means that the menace group misplaced management of LittleDrifter, which reached unintended targets.
In line with analysis from Test Level, the malware is written in VBS and was designed to propagate via USB drives, as an evolution of Gamaredon’s USB PowerShell worm.
Gamaredon, also referred to as Shuckworm, Iron Tilden, and Primitive Bear is a cyber espionage menace group related to Russian that for at the least a decade has focused organizations in Ukraine from a number of sectors, together with authorities, protection, and important infrastructure.
LitterDrifter particulars
LitterDrifter’s goal is to ascertain communications with the menace group’s command and management (C2) server and to unfold over USB drives.
To attain its purpose, the malware makes use of two separate modules, that are executed by the closely obfuscated VBS element trash.dll.
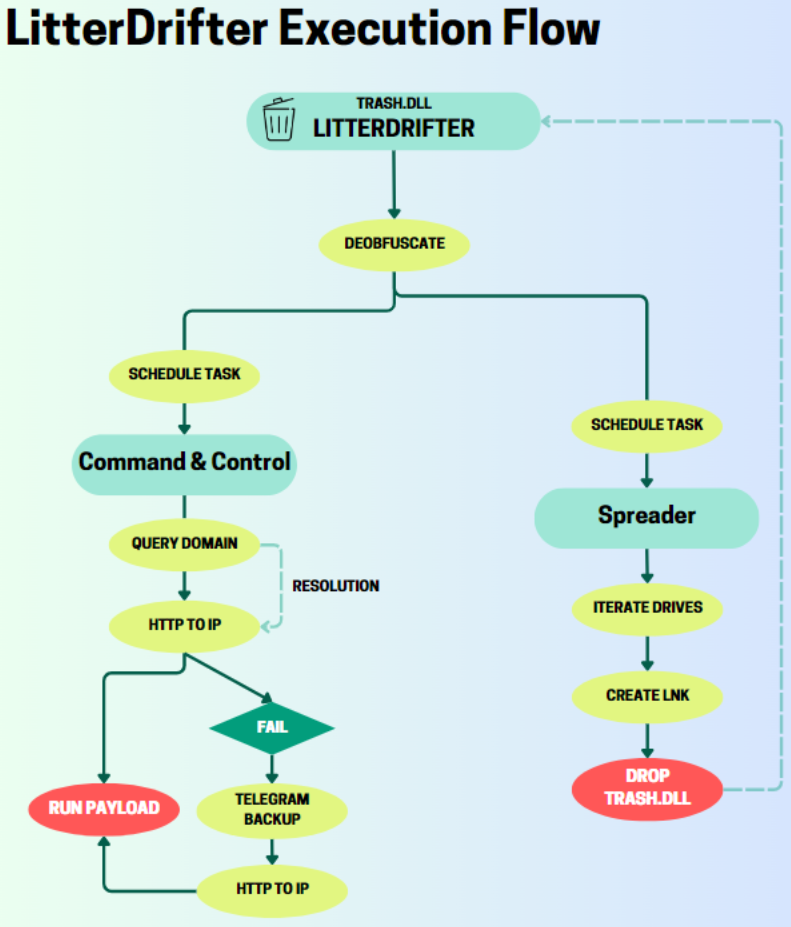
LitterDrifter and all its parts nest within the consumer’s “Favorites” listing and set up persistence by including scheduled duties and registry keys.
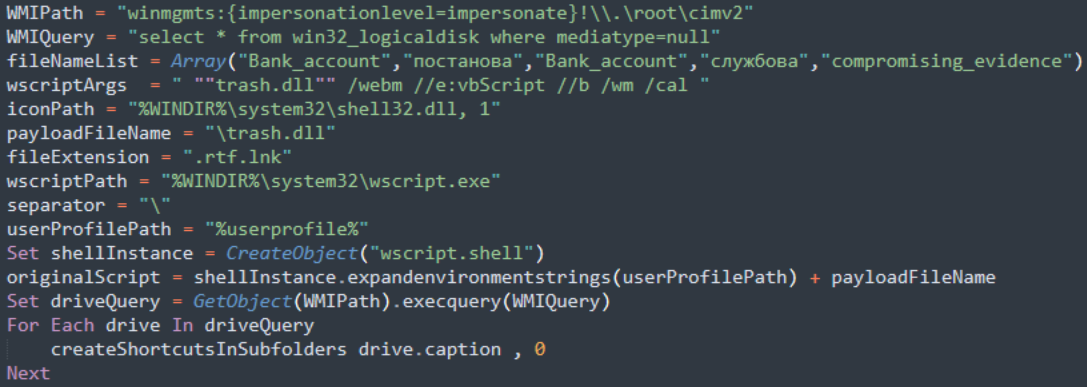
The module chargeable for propagation to different methods screens for newly inserted USB drives and creates misleading LNK shortcuts together with a hidden copy of the “trash.dll.”
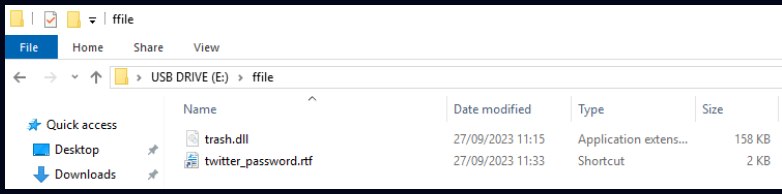
The malware makes use of the Home windows Administration Instrumentation (WMI) administration framework to establish goal drives and creates shortcuts with random names to execute malicious scripts.
The researchers clarify that Gamaredon makes use of domains as placeholder for the IP addresses the place the C2 servers are. From this angle, the menace group has a “moderately distinctive” method.
Earlier than making an attempt to contact the C2 server, the malware appears within the momentary folder for a configuration file. If such a file doesn’t exist, LittleDrifter pings one in every of Gamaredon’s domains utilizing a WMI question.
The reply to the question comprises the area’s IP handle, which is saved to a brand new configuration file.
Test Level notes that each one domains utilized by the malware are registered underneath ‘REGRU-RU’ and use the ‘.ru’ top-level area, which is in line with previous reviews on Gamaredon exercise.
The standard lifespan of every IP handle that acts as a C2 in LitterDrifter operations is about 28 hours, however the addresses might change a number of occasions per day to evade detection and blocking.
The C2 might ship extra payloads that LitterDrifter makes an attempt to decode and execute on the compromised system. CheckPoint clarifies that no extra payloads had been downloaded generally, which can point out that the assaults are extremely focused.
As a backup choice, the malware may retrieve the C2 IP handle from a Telegram channel.
LitterDrifter is probably going a part of the primary stage of an assault, making an attempt to ascertain persistence on the compromised system and ready for the C2 to ship new payloads that may additional the assault.
The malware is characterised by simplicity and doesn’t depend on novel strategies but it surely seems to be efficient.
Test Level’s report offers hashes for nearly two dozen LittleDrifter samples in addition to domains related to Gamaredon’s infrastructure.


