Public exploit code is now accessible for the vital Cisco IOS XE vulnerability tracked as CVE-2023-20198 that was leveraged as a zero-day to hack tens of hundreds of gadgets.
Cisco launched patches for many releases of its IOS XE software program however hundreds of techniques proceed to be compromised, web scans present.
CVE-2023-20198 exploit particulars
Researchers at Horizon3.ai, an organization offering safety evaluation providers, have shared particulars on how an attacker can bypass authentication on Cisco IOS XE gadgets susceptible to CVE-2023-20198.
In a technical report as we speak, the researchers present how hackers can exploit the utmost severity safety situation to create a brand new person with stage 15 privileges that present full management over the gadget.
The creation of the exploit was doable utilizing data captured from a from a honeypot arrange by SECUINFRA’s staff for digital forensics and incident response engagements.
Horizon3.ai explains that an attacker can encode an HTTP request to the Net Companies Administration Agent (WMSA) service in iosd – a strong binary in Cisco’s IOS XE that may generate the configuration file for OpenResty (an Nginx-based server with help Lua scripting) utilized by the webui service susceptible to CVE-2023-20198.
“The crux of this vulnerability is within the first line of this request POST /%2577ebui_wsma_HTTP. This intelligent encoding of webui_wsma_http bypasses the Nginx matches mentioned within the earlier submit and permits us to succeed in the WMSA service in iosd” – Horizon3.ai
The WSMA permits executing instructions by SOAP requests, together with ones that give entry to the configuration function that permits making a person with full privileges on the system.
Testing their exploit code, the researchers have been in a position to create a brand new person with administrative permissions (stage 15 privileges) seen within the gadget’s administration interface.
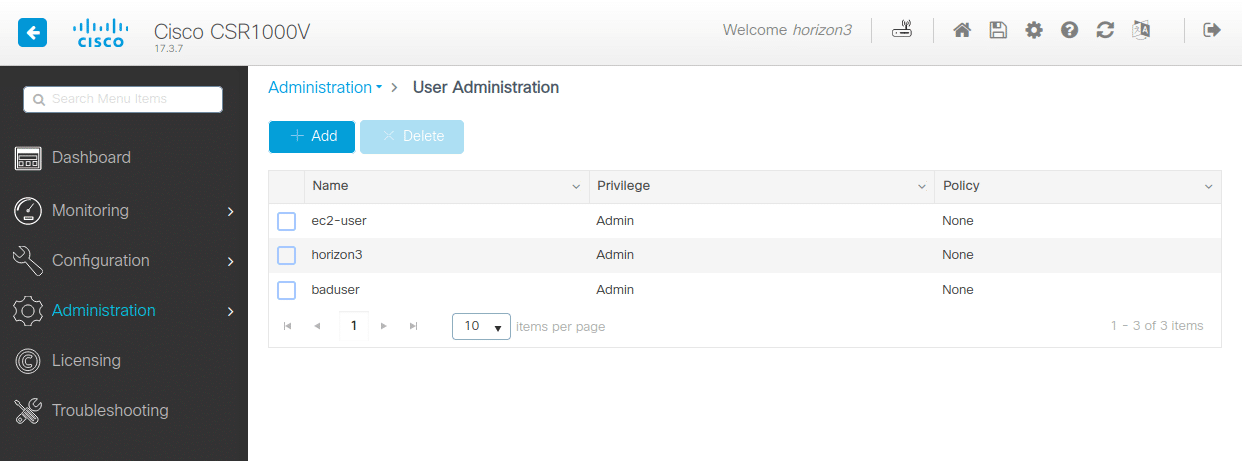
supply: Horizon3.ai
The researchers observe that from this level an attacker has full management over the gadget and will write malicious implants to disk without having to take advantage of one other vulnerability.
Cisco IOS XE backdoors come alive
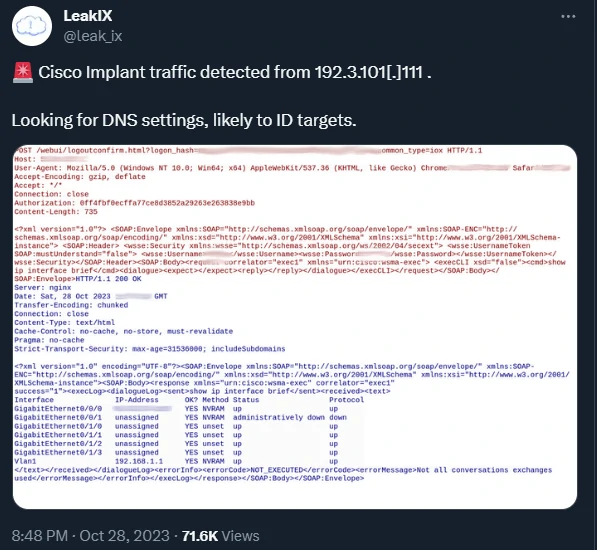
LeakIX, an intelligence platform for uncovered on-line providers, confirmed that the exploit that Secuinfra additionally noticed might efficiently hijack Cisco IOS XE gadgets.
As well as, LeakIX’s Cisco IOS XE honeypots have been awoken by the risk actors, permitting researchers to see instructions executed on gadgets.
In a PCAP file of the session shared with BleepingComputer, we will see the attackers execute the next instructions:
present ip interface temporary
present ip dns view
present ip name-serversThese are all instructions that serve reconnaissance functions, to gather data that will result in the invention of high-value targets
Cisco patches extra IOS XE variations
Cisco has up to date its safety bulletin for CVE-2023-20198 on October 30, saying updates for IOS XE that handle the vulnerability.
In the meanwhile model 17.3 of the software program is the one one nonetheless affected by the safety situation, as a brand new launch is but to turn into accessible. The corporate has additionally addressed the difficulty in Software program Upkeep Updates (SMUs).
| Cisco IOS XE Software program Launch Practice | First Mounted Launch | Obtainable |
|---|---|---|
| 17.9 | 17.9.4a | Sure |
| 17.6 | 17.6.6a | Sure |
| 17.3 | 17.3.8a | TBD |
| 16.12 (Catalyst 3650 and 3850 solely) | 16.12.10a | Sure |
The brand new software program releases can be found from the firm’s Software program Obtain Middle.
Hundreds of gadgets possible nonetheless hacked
Risk actors began exploiting CVE-2023-20198 when it was a zero-day earlier than Cisco disclosed it on October 16.
Ten days after that, the Censys platform for risk searching discovered on October 25 round 28,000 Cisco IOS XE hosts exhibiting indicators of compromise unfold everywhere in the world.
In response to Censys’ findings, lots of the hacked gadgets are at main telecommunications and web suppliers providing their providers country-wide.
Preliminary estimates after Cisco disclosed that the vulnerability was being exploited within the wild counted round 10,000 that have been working a malicious implant.
By the tip of the week, web scans confirmed that the implant was current on about 60,000 Cisco IOS XE gadgets uncovered on the general public net.
The quantity dropped out of the blue shortly after, as lots of the hacked gadgets grew to become invisible when the risk actor altered the malicious code to examine for an Authorization header earlier than responding.
Researchers at cybersecurity firm Fox-IT got here up with a scanning technique adjusted to the change that exposed near 38,000 compromised Cisco IOS XE hosts on October 23.