
A proof-of-concept exploit was publicly launched for a vital distant code execution vulnerability within the CrushFTP enterprise suite, permitting unauthenticated attackers to entry recordsdata on the server, execute code, and procure plain-text passwords.
The vulnerability was found in August 2023, tracked as CVE-2023-43177, by Converge safety researchers, who responsibly reported it to the seller. The builders launched a repair in a single day in model CrushFTP 10.5.2.
Right this moment, Converge revealed a proof-of-concept exploit for the CVE-2023-43177 flaw, making it vital for CrushFTP customers to put in the safety updates as quickly as attainable.
Exploiting CrushFTP
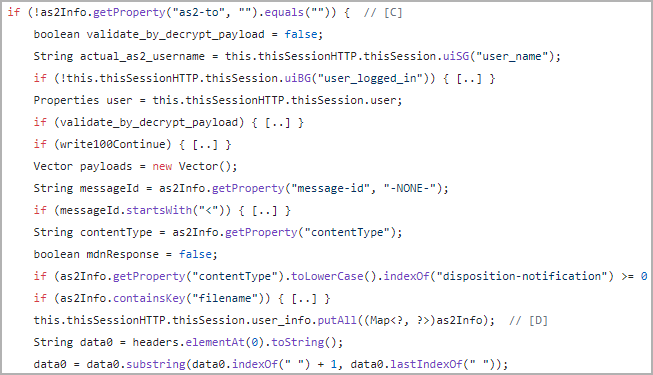
The CrushFTP exploit is performed via an unauthenticated mass-assignment vulnerability, exploiting the AS2 header parsing to manage consumer session properties.
This permits attackers to learn and delete recordsdata, doubtlessly main to finish system management and root-level distant code execution.
The attackers can ship payloads to the CrushFTP service on particular ports (80, 443, 8080, 9090) utilizing net headers, which depart log traces.
Subsequent, the attackers overwrite session information utilizing Java’s ‘putAll()’ operate, enabling the impersonation of ‘directors,’ and leverage the ‘drain_log()’ operate to govern recordsdata as wanted to take care of stealthiness.
Finally, the attackers can leverage the ‘periods. obj’ file in this system’s set up folder to hijack stay consumer periods belonging to admin accounts, primarily attaining privileged escalation.
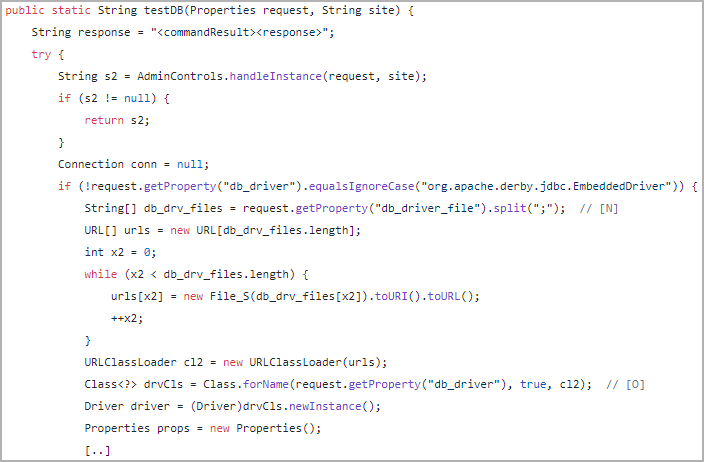
Having established admin entry, the attacker can exploit flaws within the admin panel’s dealing with of SQL driver loading and database configuration testing (testDB) to execute arbitrary Java code.
Converge has revealed an illustration of the video of the PoC exploit in use, as proven under.
1000’s of susceptible gadgets
In line with Converge’s report, there are roughly 10,000 public-facing CrushFTP situations and sure many extra behind company firewalls. The assault floor is sizable though the variety of susceptible situations hasn’t been decided.
File switch merchandise like CrushFTP are significantly engaging to ransomware actors, particularly Clop, identified for leveraging zero-day vulnerabilities in software program just like the MOVEit Switch, GoAnywhere MFT, and Accelion FTA to conduct information theft assaults.
Sadly, the researchers revealed that even making use of the patches would not safe CrushFTP endpoints in opposition to all attainable threats.
“Converge’s menace intelligence signifies that the safety patch has been reverse-engineered, and adversaries have developed proofs of ideas. Due to that, upcoming exploitation is probably going.” – Converge
To successfully mitigate the danger, it is suggested to observe these steps:
- Replace CrushFTP to the most recent model.
- Allow computerized safety patch updates.
- Change the password algorithm to Argon.
- Audit for unauthorized customers and examine for current password adjustments.
- Activate the brand new Restricted Server mode for enhanced safety.
Further measures that may be applied to boost CrushFTP safety additional embody:
- Utilizing a restricted privilege working system service account for CrushFTP.
- Deploying Nginx or Apache as a reverse proxy for public-facing servers.
- Setting firewall guidelines to restrict CrushFTP visitors to trusted IP ranges and hosts.
It is important to implement these safety measures as quickly as attainable, because the publicly disclosed exploit particulars of CVE-2023-43177 are doubtless for use by hackers in opportunistic assaults.


