
A brand new dropper-as-a-service (DaaS) cybercrime operation named ‘SecuriDropper’ has emerged, utilizing a way that bypasses the ‘Restricted Settings’ characteristic in Android to put in malware on units and procure entry to Accessibility Companies.
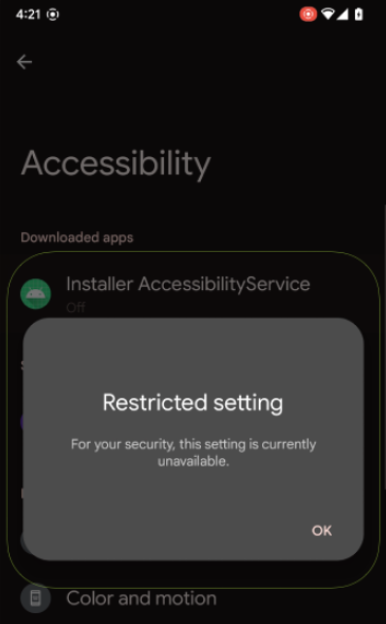
Restricted Settings is a safety characteristic launched with Android 13 that forestalls side-loaded functions (APK recordsdata) put in from outdoors Google Play to entry highly effective options just like the Accessibility settings and Notification Listener.
The 2 permissions are generally abused by malware, so the characteristic was supposed to guard customers by blocking the approval of requests by displaying a warning when these permissions are requested.
(ThreatFabric)
Accessibility will be abused to seize on-screen textual content, granting extra permissions, and performing navigation actions remotely, whereas the Notification Listener can be utilized to steal one-time passwords.
In August 2022, ThreatFabric reported that malware builders have been already adjusting their ways to this new measure by means of a new dropper named ‘BugDrop.’
Based mostly on its observations, the agency created a proof-of-concept (PoC) dropper to showcase that the bypass was attainable.
The trick is to make use of the session-based set up API for the malicious APK (Android bundle) recordsdata, which installs them in a number of steps, involving a “base” bundle and varied “break up” information recordsdata.
When the actual API is used as an alternative of the non-session technique, Restricted Settings is bypassed, and customers will not be proven the ‘Restricted setting’ dialog that forestalls them from granting the malware entry to harmful permissions.
BleepingComputer has confirmed that the safety subject remains to be current in Android 14, and, in line with a brand new ThreatFabric report, SecuriDropper follows the identical approach to side-load malware on course units and provides them entry to dangerous sub-systems.
That is the primary noticed case of this technique being utilized in cybercrime operations focusing on Android customers.
Android Dropper-as-a-Service operations
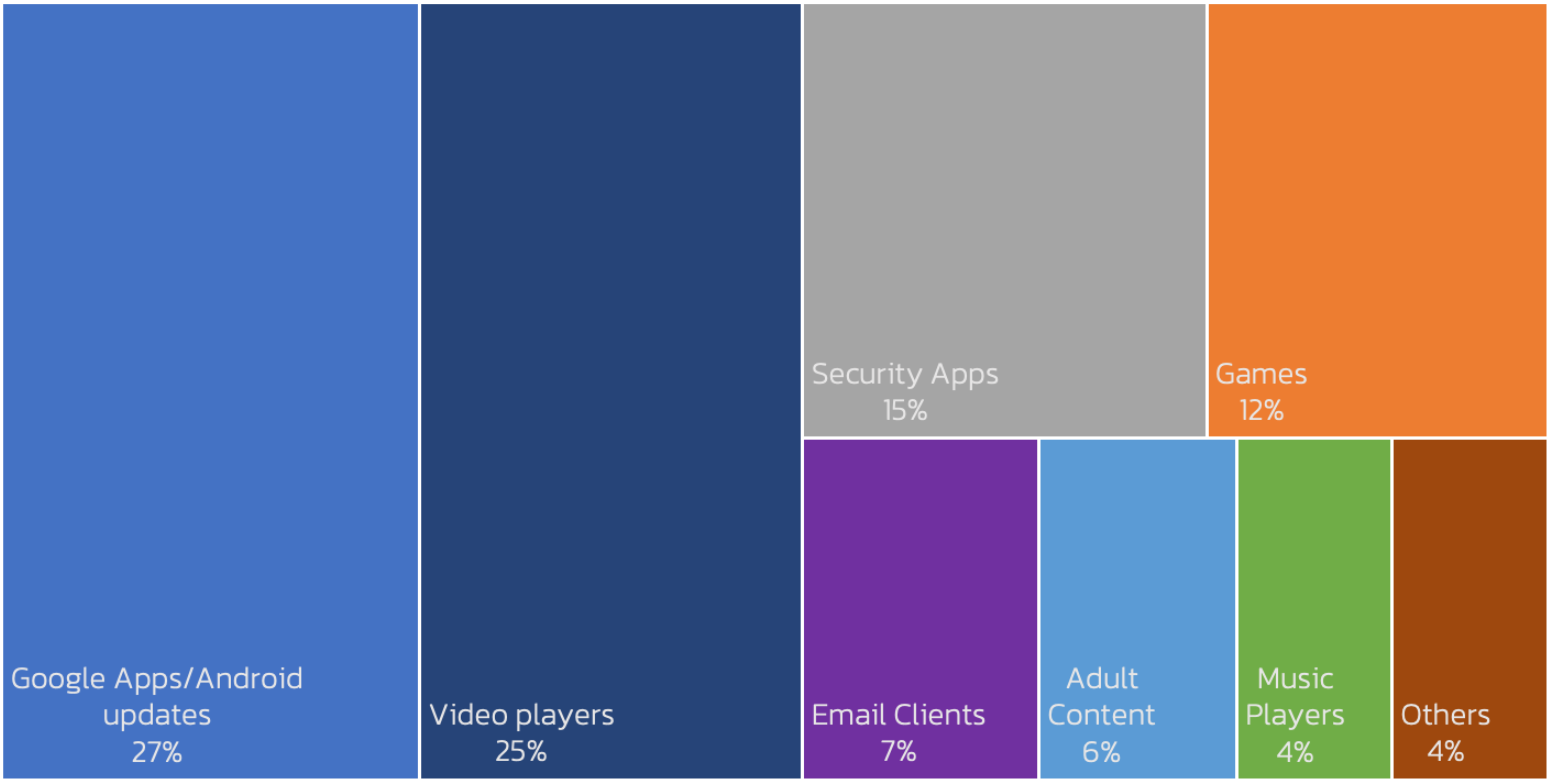
SecuriDropper infects Android units posing as a professional app, most frequently impersonating a Google app, Android replace, video participant, safety app, or a recreation, after which putting in a second payload, which is a few type of malware.
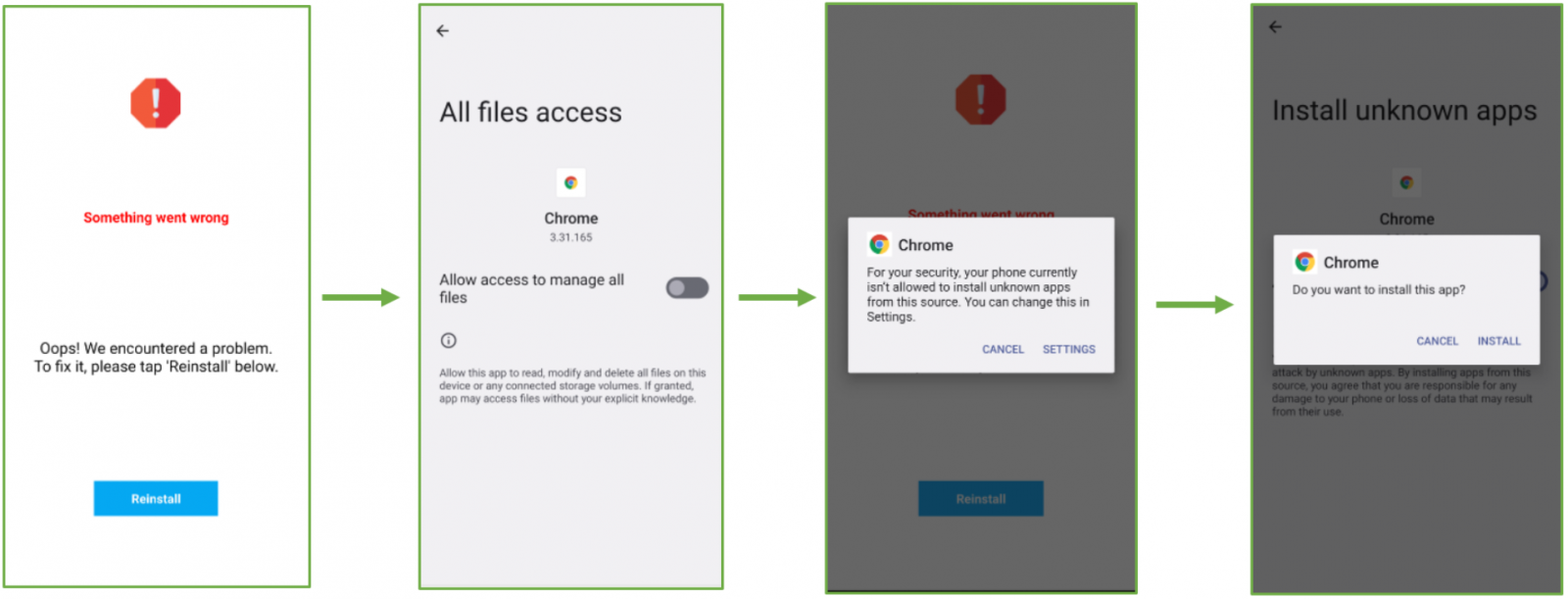
The dropper achieves this by securing entry to the “Learn & Write Exterior Storage” and “Set up & Delete Packages” permissions upon set up.
The second-stage payload is put in by means of person deception and interface manipulation, prompting customers to click on a “Reinstall” button after displaying bogus error messages in regards to the dropper app’s set up.
ThreatFabric has seen SpyNote malware distributed by means of SecuriDropper disguised as a Google Translate app.
In different circumstances, SecuriDropper was seen distributing banking Ermac trojans disguised because the Chrome browser, focusing on a whole lot of cryptocurrency and e-banking functions.
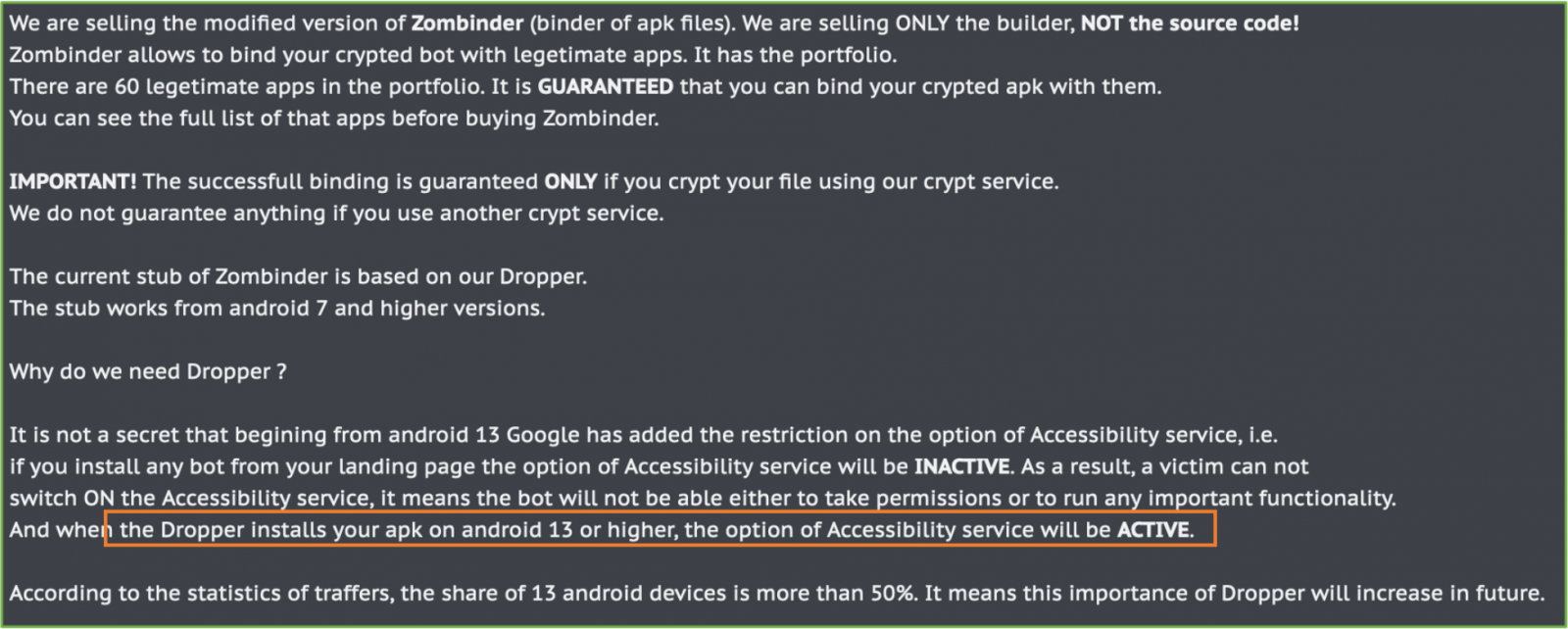
ThreatFabric additionally studies on the re-surfacing of Zombinder, a DaaS operation first documented in December 2022. This service “glues” malicious payloads with professional apps to contaminate Android units with info-stealers and banking trojans.
Worryingly, Zombinder’s current commercials spotlight the identical Restricted Settings bypass technique beforehand mentioned, so the payloads are granted permission to make use of Accessibility settings upon set up.
To guard towards these assaults, Android customers ought to keep away from downloading APK recordsdata from obscure sources or publishers they do not know and belief.
Entry to permissions for any put in app will be reviewed and revoked by going to Settings → Apps → [select an app] → Permissions.
Replace 11/6: In response to a request for a remark by BleepingComputer, a Google spokesperson has despatched us the next assertion:
Restricted settings add an additional layer of safety on high of the person affirmation that’s required for apps to entry Android settings/permissions.
As a core safety, Android customers are all the time in command of which permissions they grant to an app.
Customers are additionally protected by Google Play Shield, which might warn customers or block apps identified to exhibit malicious habits on Android units with Google Play Companies.
We’re consistently reviewing assault strategies and enhancing Android’s defenses towards malware to assist hold customers secure.


