
A proof-of-concept (PoC) exploit is launched for the ‘Citrix Bleed’ vulnerability, tracked as CVE-2023-4966, that enables attackers to retrieve authentication session cookies from weak Citrix NetScaler ADC and NetScaler Gateway home equipment.
CVE-2023-4966 is a critical-severity remotely exploitable info disclosure flaw Citrix mounted on October 10 with out offering many particulars.
On October 17, Mandiant revealed that the flaw was abused as a zero-day in restricted assaults since late August 2023.
This Monday, Citrix issued a subsequent warning to directors of NetScaler ADC and Gateway home equipment, urging them to patch the flaw instantly, as the speed of exploitation has began to choose up.
At this time, researchers at Assetnote shared extra particulars concerning the exploitation technique of CVE-2023-4966 and printed a PoC exploit on GitHub to exhibit their findings and assist those that need to take a look at for publicity.
The Citrix Bleed flaw
The CVE-2023-4966 Citrix Bleed flaw is an unauthenticated buffer-related vulnerability affecting Citrix NetScaler ADC and NetScaler Gateway, community units used for load balancing, firewall implementation, site visitors administration, VPN, and consumer authentication.
By analyzing the unpatched (13.1-48.47) and patched variations (13.1-49.15) of NetScaler, Assetnote discovered 50 operate adjustments.
Amongst these features, the researchers discovered two (‘ns_aaa_oauth_send_openid_config’ and ‘ns_aaa_oauthrp_send_openid_config’) that featured extra bounds checks previous the era of a response.
These features use ‘snprintf’ to insert the suitable information into the generated JSON payload for the OpenID configuration. Within the pre-patch model, the response is shipped instantly with out checks.
The vulnerability emerges from the return worth of the snprintf operate, which may result in a buffer over-read if exploited.
The patched model ensures {that a} response will solely be despatched if snprintf returns a worth decrease than 0x20000.
Snatching session tokens
Armed with that data, Assetnote’s analysts tried to use weak NetScaler endpoints.
Throughout that course of, they discovered that the hostname worth used for producing the payload comes from the HTTP Host header, so one doesn’t want administrator rights to entry it.
Moreover, the hostname is inserted into the payload six occasions. Therefore, its exploitation makes it doable to exceed the buffer restrict, forcing the endpoint to reply with the buffer’s contents and adjoining reminiscence.
“We might clearly see a number of leaked reminiscence instantly following the JSON payload,” explains Assetnote within the report.
“Whereas a number of it was null bytes, there was some suspicious-looking info within the response.”
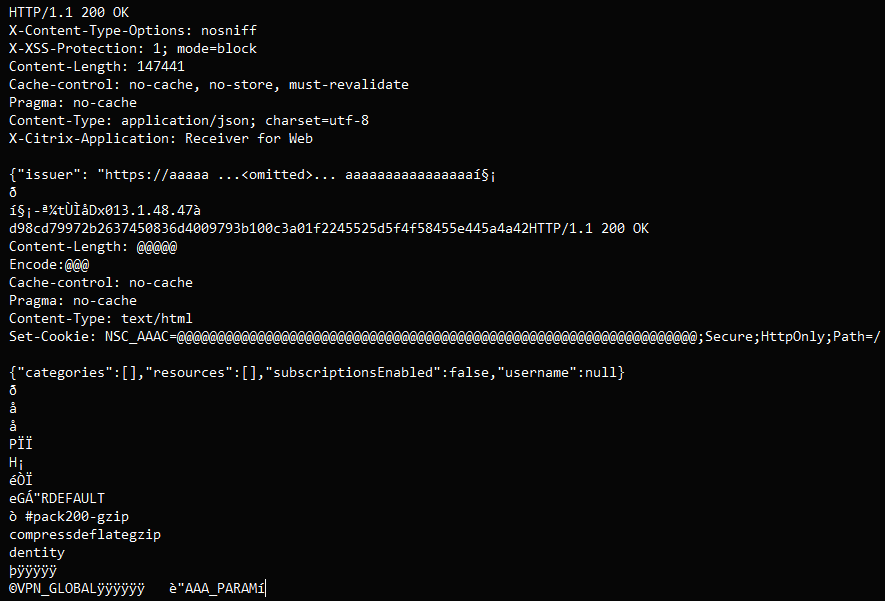
By exploiting the vulnerability hundreds of occasions for testing, the analysts persistently positioned a 32-65 byte lengthy hex string that may be a session cookie.
Retrieving that cookie makes it doable for attackers to hijack accounts and acquire unrestricted entry to weak home equipment.
Now {that a} CVE-2023-4966 exploit is publicly obtainable, it’s anticipated that risk actors will enhance their concentrating on of Citrix Netscaler units to realize preliminary entry to company networks.
Menace monitoring service Shadowserver experiences spikes of exploitation makes an attempt following the publication of Assetnote’s PoC, so the malicious exercise has already began.
As a majority of these vulnerabilities are generally used for ransomware and information theft assaults, it’s strongly suggested that system directors instantly deploy patches to resolve the flaw.


