
Cisco is warning of 5 new Catalyst SD-WAN Supervisor merchandise vulnerabilities with probably the most vital permitting unauthenticated distant entry to the server.
Cisco Catalyst SD-WAN Supervisor for WAN is community administration software program permitting admins to visualise, deploy, and handle gadgets on vast space networks (WAN).
Probably the most extreme of the disclosed flaws impacting the product is CVE-2023-20252 (CVSS v3.1: 9.8), which permits unauthorized entry as a consequence of points with the Safety Assertion Markup Language (SAML) APIs.
“A vulnerability within the Safety Assertion Markup Language (SAML) APIs of Cisco Catalyst SD-WAN Supervisor might enable an unauthenticated, distant attacker to realize unauthorized entry to the appliance as an arbitrary consumer,” warns the safety bulletin.
The flaw could be leveraged by sending specifically crafted requests on to the SAML APIs, which generate arbitrary authorization tokens that enable unconditional entry to the appliance.
Exploitation of CVE-2023-20252 has the potential for consumer impersonation, unauthorized information entry/modification/deletion, and repair disruption.
The remaining 4 vulnerabilities are much less extreme:
- CVE-2023-20253 (CVSS v3.1: 8.4): Unauthorized configuration rollback as a consequence of CLI vulnerabilities.
- CVE-2023-20034 (CVSS v3.1: 7.5): Data disclosure vulnerability in Elasticsearch entry management.
- CVE-2023-20254 (CVSS v3.1: 7.2): Authorization bypass within the session administration system. (requires multi-tenant characteristic enabled)
- CVE-2023-20262 (CVSS v3.1: 5.3): DoS vulnerability within the SSH service. (impacts SSH entry solely)
It’s value noting that CVE-2023-20034 can also be remotely exploitable with out requiring authentication. Nevertheless, its severity is mitigated by the truth that entry is restricted to the Elasticsearch database with the privileges of the Elasticsearch consumer.
The 5 flaws affect varied variations of Cisco Catalyst SD-WAN Supervisor, with extra particulars on the impacted and goal improve variations beneath:
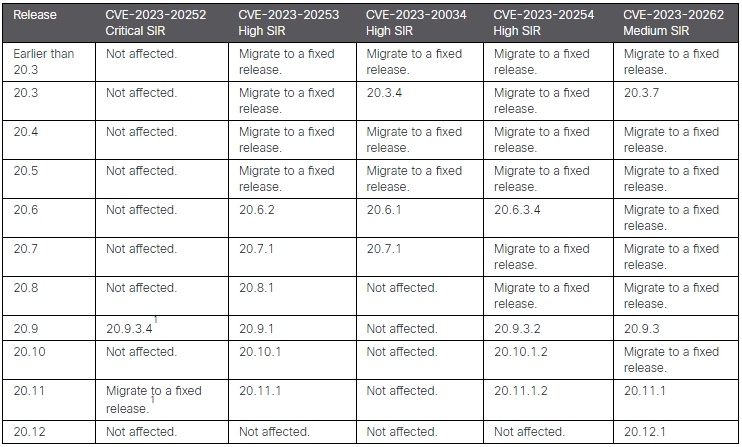
CVE-2023-20252, which is probably the most pressing to repair, impacts releases 20.9.3.2 and 20.11.1.2 however doesn’t have an effect on older releases within the 20.9 and 20.11 branches.
Catalyst SD-WAN Supervisor model 20.12, the most recent out there launch, will not be impacted by any flaws aside from the medium severity one (fastened in 20.12.1), so that is the most secure model to improve to if potential.
Cisco has shared no workarounds for the fastened flaws this time, so the one really helpful motion is upgrading to a patched launch.
The seller clarifies that IOS XE Software program, SD-WAN cEdge Routers, and SD-WAN vEdge Routers should not susceptible.
Not one of the flaws are reported as actively exploited, but upgrading to the really helpful variations needs to be handled with urgency.


