
CISA warned on Wednesday that attackers are actively exploiting two safety vulnerabilities in N‑in a position’s N-central distant monitoring and administration (RMM) platform.
N-central is usually utilized by managed providers suppliers (MSPs) and IT departments to observe, handle, and preserve shopper networks and gadgets from a centralized web-based console.
In line with CISA, the 2 flaws can enable menace actors to achieve command execution through an insecure deserialization weak point (CVE-2025-8875) and inject instructions by exploiting an improper sanitization of person enter vulnerability (CVE-2025-8876).
Though N-able has but to verify CISA’s report that the safety bugs are actually being exploited within the wild, the corporate patched them in N-central 2025.3.1. It additionally urged admins to safe their programs earlier than additional data on the bugs is launched.
“This launch features a important safety repair for CVE-2025-8875 and CVE-2025-8876. These vulnerabilities require authentication to take advantage of. Nevertheless, there’s a potential danger to the safety of your N-central surroundings, if unpatched,” N-able mentioned in a Wednesday advisory.
“You have to improve your on-premises N-central to 2025.3.1. (Particulars of the CVEs will probably be printed three weeks after the discharge as per our safety practices.)”
Whereas the U.S. cybersecurity company has not but shared particulars concerning the assaults exploiting these N-central safety bugs, it said that there is no proof that they are being utilized in ransomware assaults.
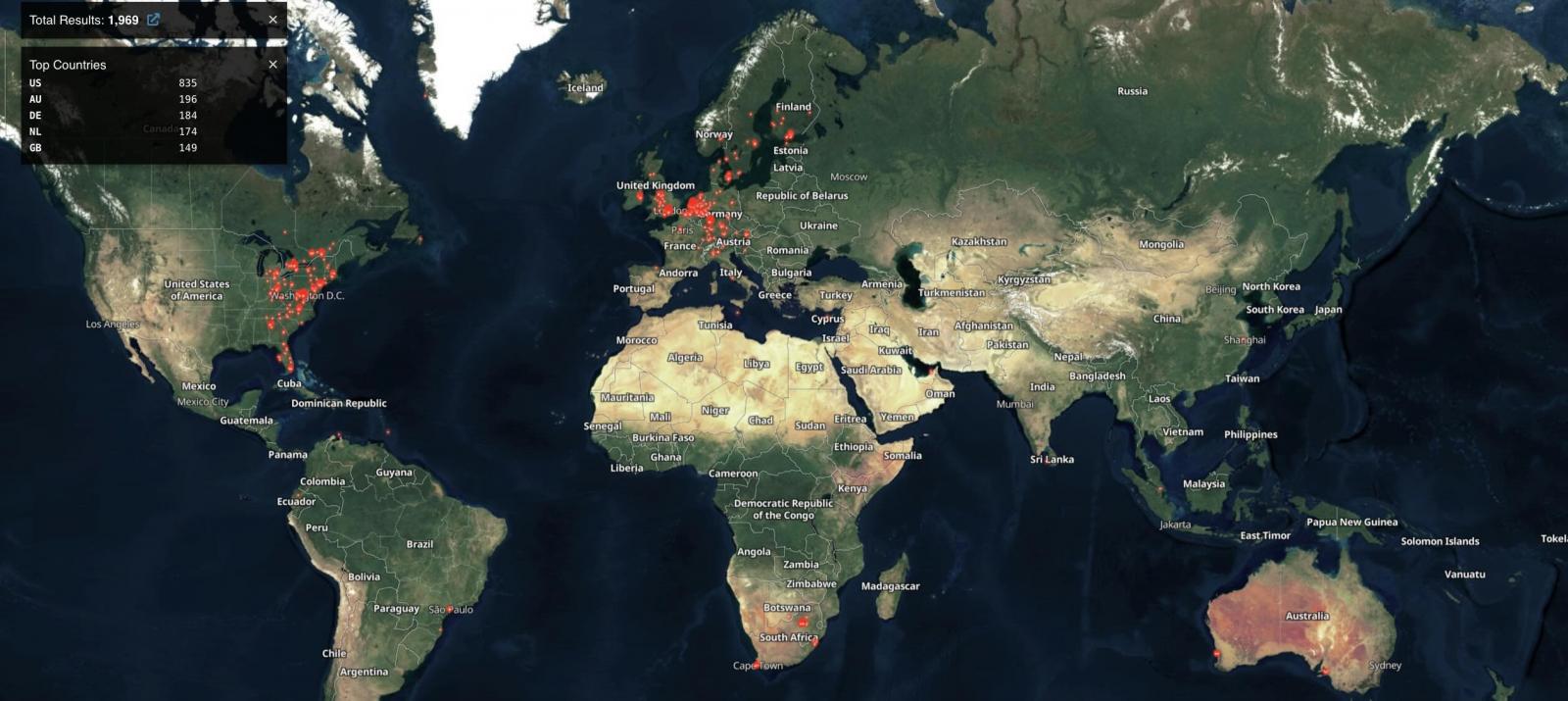
In line with Shodan searches, roughly 2,000 N-able N-central situations are uncovered on-line (a few of that are seemingly already patched), with the bulk originating from america, Australia, and Germany.
CISA has additionally added the issues to its Identified Exploited Vulnerabilities Catalog, giving Federal Civilian Government Department (FCEB) businesses only one week to patch their programs by August 20, as mandated by the November 2021 Binding Operational Directive (BOD) 22-01.
Regardless that BOD 22-01 primarily targets U.S. federal businesses, CISA inspired all organizations, together with these within the non-public sector, to prioritize securing their gadgets in opposition to this actively exploited safety flaw as quickly as doable.
“Apply mitigations per vendor directions, comply with relevant BOD 22-01 steerage for cloud providers, or discontinue use of the product if mitigations are unavailable,” CISA cautioned on Monday.
“A majority of these vulnerabilities are frequent assault vectors for malicious cyber actors and pose vital dangers to the federal enterprise.”
Final week, CISA issued an emergency directive ordering non-military businesses inside the U.S. govt department to mitigate a important Microsoft Alternate hybrid vulnerability (CVE-2025-53786) by 9:00 AM ET on Monday morning.



