
Google’s Risk Intelligence Group (GTIG), Mandiant, and companions disrupted a worldwide espionage marketing campaign attributed to a suspected Chinese language menace actor that used SaaS API calls to cover malicious site visitors in assaults concentrating on telecom and authorities networks.
The marketing campaign has been lively since not less than 2023 and has impacted 53 organizations in 42 nations, with suspected infections in not less than 20 extra nations.
The preliminary entry vector is unknown, however the researchers be aware that the menace actor, which Google tracks internally as UNC2814, has beforehand gained entry by exploiting flaws in internet servers and edge techniques.
.jpg)
Supply: Google
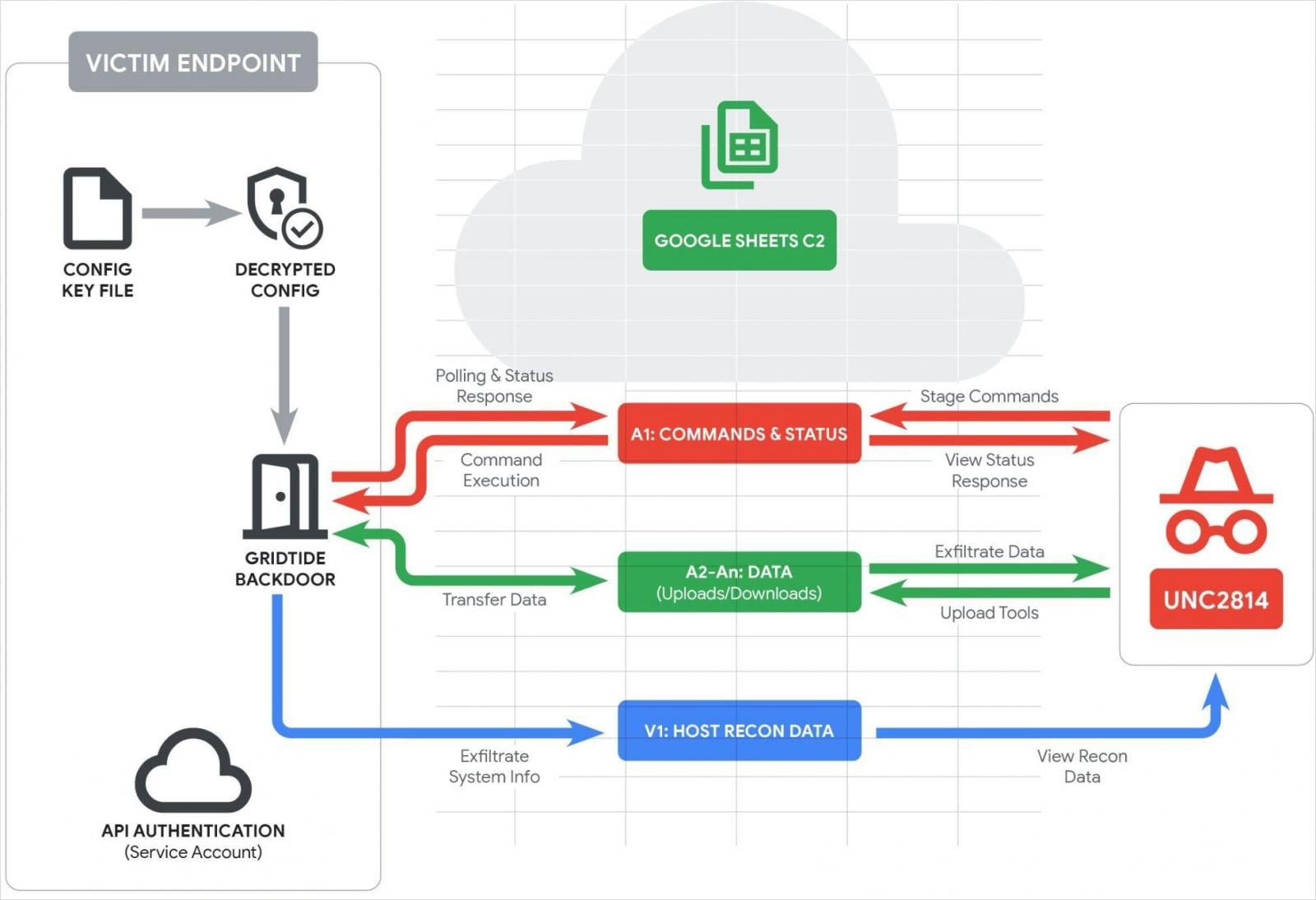
Google says that within the just lately disrupted marketing campaign, the actor deployed a brand new C-based backdoor named ‘GRIDTIDE,’ which abuses the Google Sheets API for evasive command-and-control (C2) operations.
GRIDTIDE authenticates to a Google Service Account utilizing a hardcoded personal key, and upon launch, it sanitizes the spreadsheet by deleting rows 1-1000 and columns from A to Z.
It then performs host reconnaissance, accumulating the username, hostname, OS particulars, native IP, locale, and timezone, and logging the info in cell V1.
The primary cell within the spreadsheet, A1, is the command/standing cell, which GRIDTIDE polls continuously to obtain directions.
If any exist, the malware overwrites them with a standing string. If empty, the malware retries each second for 120 occasions, then switches to random 5-10-minute checks to scale back noise.
The instructions supported by GRIDTIDE are:
- C – execute Base64-encoded bash instructions, write output to the sheet
- U – add: take knowledge in A2:A<arg_2> and reconstruct/write file at encoded filepath <arg_1>
- D – obtain: learn native file <arg_1> on endpoint, ship contents in ~45 KB fragments into A2:An
The A2-An cells are used for writing the command output, exfiltrated information, and importing instruments.
Google stories that GRIDTIDE’s exchanges with the C2 depend on a URL-safe base64 encoding scheme that evades detection by internet monitoring instruments and blends with regular site visitors.
Supply: Google
In not less than one case, Google confirmed that GRIDTIDE was deployed on a system that contained delicate personally identifiable info (PII). Nevertheless, the researchers didn’t immediately observe knowledge exfiltration.
Google, Mandiant, and companions took coordinated motion to disrupt the marketing campaign by terminating all Google Cloud initiatives managed by UNC2814, disabling recognized infrastructure, revoking Google Sheets API entry, and disabling all cloud initiatives utilized in C2 operations. Present and historic domains have been sinkholed.
Organizations impacted by GRIDTIDE have been notified immediately, and help was provided to scrub the infections.
Google has listed detection guidelines on the backside of the report, in addition to indicators of compromise (IoCs).
Regardless that the disruption to the marketing campaign was complete, Google expects UNC2814 to renew exercise utilizing new infrastructure within the close to future.
Fashionable IT infrastructure strikes quicker than handbook workflows can deal with.
On this new Tines information, find out how your group can scale back hidden handbook delays, enhance reliability via automated response, and construct and scale clever workflows on high of instruments you already use.




