
Professors on the College of South Australia and Charles Sturt College have developed an algorithm to detect and intercept man-in-the-middle (MitM) assaults on unmanned navy robots.
MitM assaults are a sort of cyberattack the place the info site visitors between two events, on this case, the robotic and its professional controllers, is intercepted both to eavesdrop or to inject false knowledge within the stream.
Such malicious assaults goal to interrupt the operation of unmanned autos, modify the transmitted directions, and, in some instances, even assume management, instructing the robots to take harmful actions.
“The robotic working system (ROS) is extraordinarily prone to knowledge breaches and digital hijacking as a result of it’s so extremely networked,” feedback Professor Anthony Finn, who participated within the examine.
“The appearance of Trade 4, marked by the evolution in robotics, automation, and the Web of Issues, has demanded that robots work collaboratively, the place sensors, actuators, and controllers want to speak and alternate info with each other by way of cloud providers.”
“The draw back of that is that it makes them extremely weak to cyberattacks.”
The college researchers developed an algorithm utilizing machine studying strategies to detect these makes an attempt and shut them down in seconds.
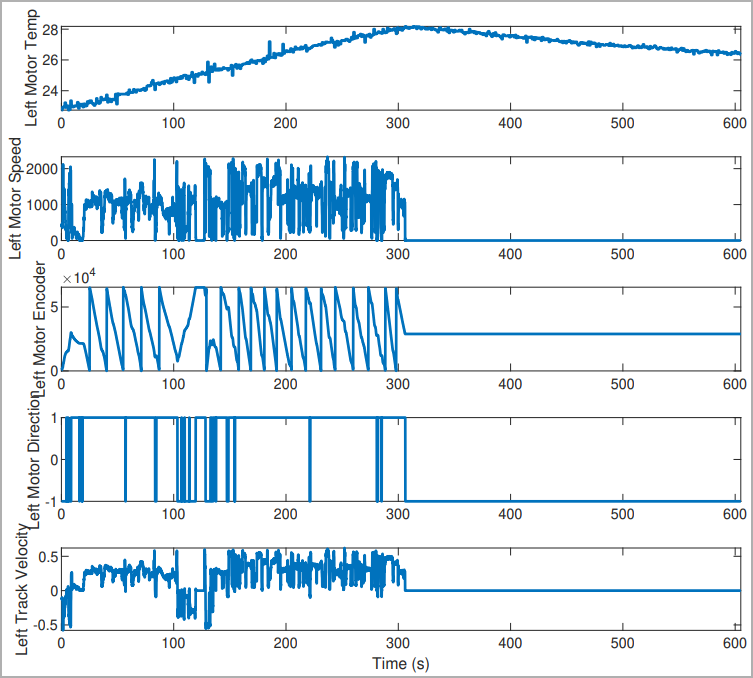
The algorithm was examined in a reproduction of the GVR-BOT utilized by the U.S. Military (TARDEC), and recorded profitable assault prevention 99% of the time, with false positives occurring in lower than 2% of the examined instances.

Discerning MitM assaults
Detecting MitM focusing on crewless autos and robots is complicated as these methods function underneath fault-tolerant modes, so distinguishing between regular operations and fault circumstances may be hazy.
Additionally, robotic methods may be compromised at varied ranges, from the core system to its sub-systems and their sub-components, inflicting an operational downside that might render the robotic dysfunctional..
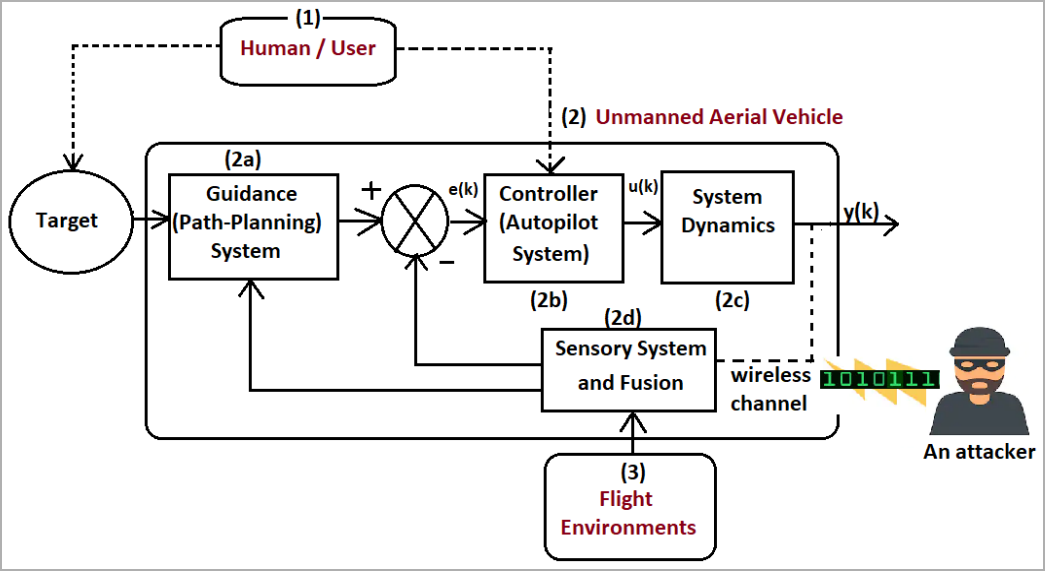
The college researchers developed a system that analyzed the robotic’s community site visitors knowledge to detect makes an attempt to compromise it. This technique makes use of node-based strategies, scrutinizes packet knowledge, and makes use of a flow-statistic-based system that reads metadata from the packet header.
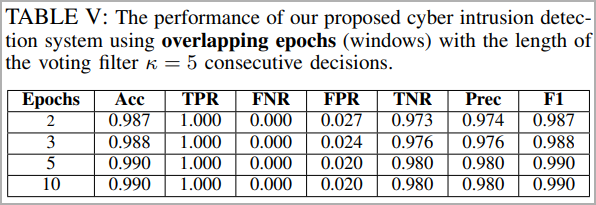
The detailed technical paper launched by the researchers delves into the specifics of the deep studying CNN (convolutional neural community) mannequin that was developed for this function, comprising a number of layers and filters that increase the reliability of the cyberattack detection consequence.
Actual assessments performed on the reproduction bot with simulated cyber-attacks focusing on varied methods produced wonderful outcomes and excessive identification accuracy even after solely 2-3 epochs of mannequin coaching.
Optimized variations of this novel safety system might discover purposes in related however extra demanding robotic purposes, like unmanned plane.
“We’re additionally fascinated about investigating the efficacy of our intrusion detection system on completely different robotic platforms, reminiscent of unmanned aerial autos, whose dynamics are fairly sooner and extra complicated in comparison with a floor robotic,” concludes the paper printed on IEEE’s portal.


