
A important severity vulnerability in a WordPress plugin with greater than 90,000 installs can let attackers acquire distant code execution to totally compromise weak web sites.
Often known as Backup Migration, the plugin helps admins automate website backups to native storage or a Google Drive account.
The safety bug (tracked as CVE-2023-6553 and rated with a 9.8/10 severity rating) was found by a crew of bug hunters generally known as Nex Staff, who reported it to WordPress safety agency Wordfence underneath a not too long ago launched bug bounty program.
It impacts all plugin variations as much as and together with Backup Migration 1.3.6, and malicious actors can exploit it in low-complexity assaults with out person interplay.
CVE-2023-6553 permits unauthenticated attackers to take over focused web sites by gaining distant code execution by means of PHP code injection through the /consists of/backup-heart.php file.
“This is because of an attacker with the ability to management the values handed to an embody, and subsequently leverage that to attain distant code execution. This makes it potential for unauthenticated menace actors to simply execute code on the server,” Wordfence stated on Monday.
“By submitting a specially-crafted request, threat-actors can leverage this situation to incorporate arbitrary, malicious PHP code and execute arbitrary instructions on the underlying server within the safety context of the WordPress occasion.”
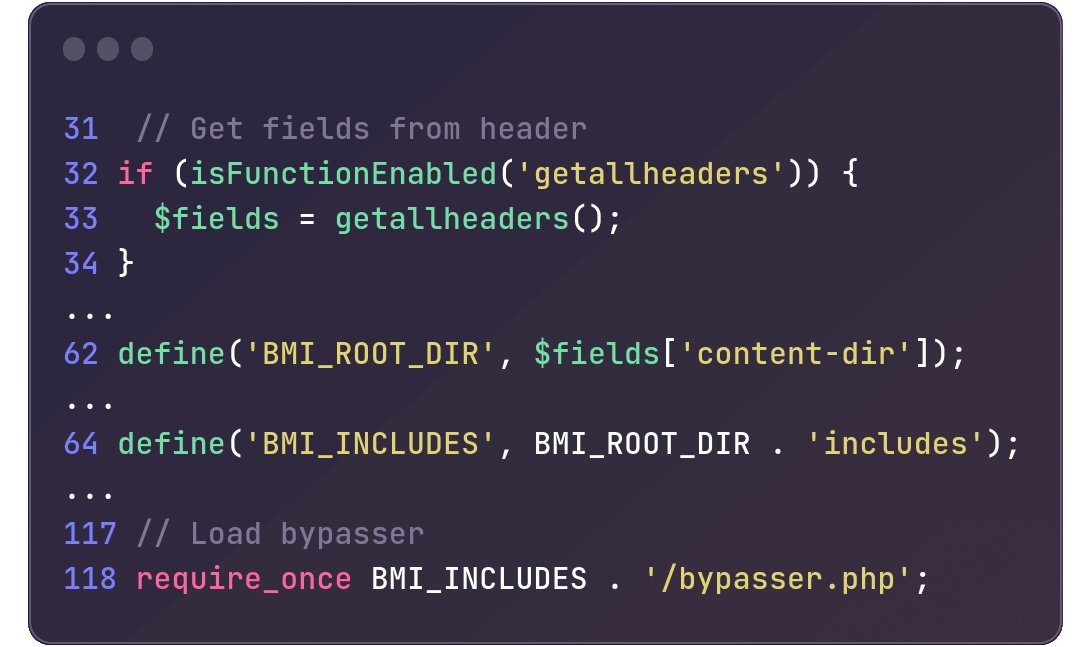
Within the /consists of/backup-heart.php file utilized by the Backup Migration plugin, an try is made to include bypasser.php from the BMI_INCLUDES listing (outlined by merging BMI_ROOT_DIR with the consists of string) at line 118.
Nonetheless, BMI_ROOT_DIR is outlined by means of the content-dir HTTP header discovered on line 62, thereby making BMI_ROOT_DIR topic to person management.
Patch launched inside hours
Wordfence reported the important safety flaw to BackupBliss, the event crew behind the Backup Migration plugin, on December 6, with the builders releasing a patch hours later.
Nonetheless, regardless of the discharge of the patched Backup Migration 1.3.8 plugin model on the day of the report, nearly 50,000 WordPress web sites utilizing a weak model nonetheless need to be secured practically one week later, as WordPress.org org obtain stats present.
Admins are strongly suggested to safe their web sites in opposition to potential CVE-2023-6553 assaults, on condition that it is a important vulnerability that unauthenticated malicious actors can exploit remotely.
WordPress directors are additionally being focused by a phishing marketing campaign trying to trick them into putting in malicious plugins utilizing faux WordPress safety advisories for a fictitious vulnerability tracked as CVE-2023-45124 as bait.
Final week, WordPress additionally mounted a Property Oriented Programming (POP) chain vulnerability that would enable attackers to realize arbitrary PHP code execution underneath sure circumstances (when mixed with some plugins in multisite installations).


