
A newly recognized cybercrime service generally known as 1Campaign is enabling risk actors to run malicious Google Adverts that stay on-line for prolonged intervals whereas evading scrutiny from safety researchers.
1Campaign is a cloaking service that passes Google’s screening course of and reveals malicious content material solely to actual potential victims. Safety researchers and automatic scanners are served benign white pages.
The operation has been energetic for no less than three years and is managed by a developer utilizing the identify ‘DuppyMeister,’ based on a report from information safety firm Varonis.
“The software passes Google’s screening, filters out safety researchers, and retains phishing and crypto drainer pages on-line for so long as attainable, funneling actual customers to attacker-controlled websites,” the researchers say.
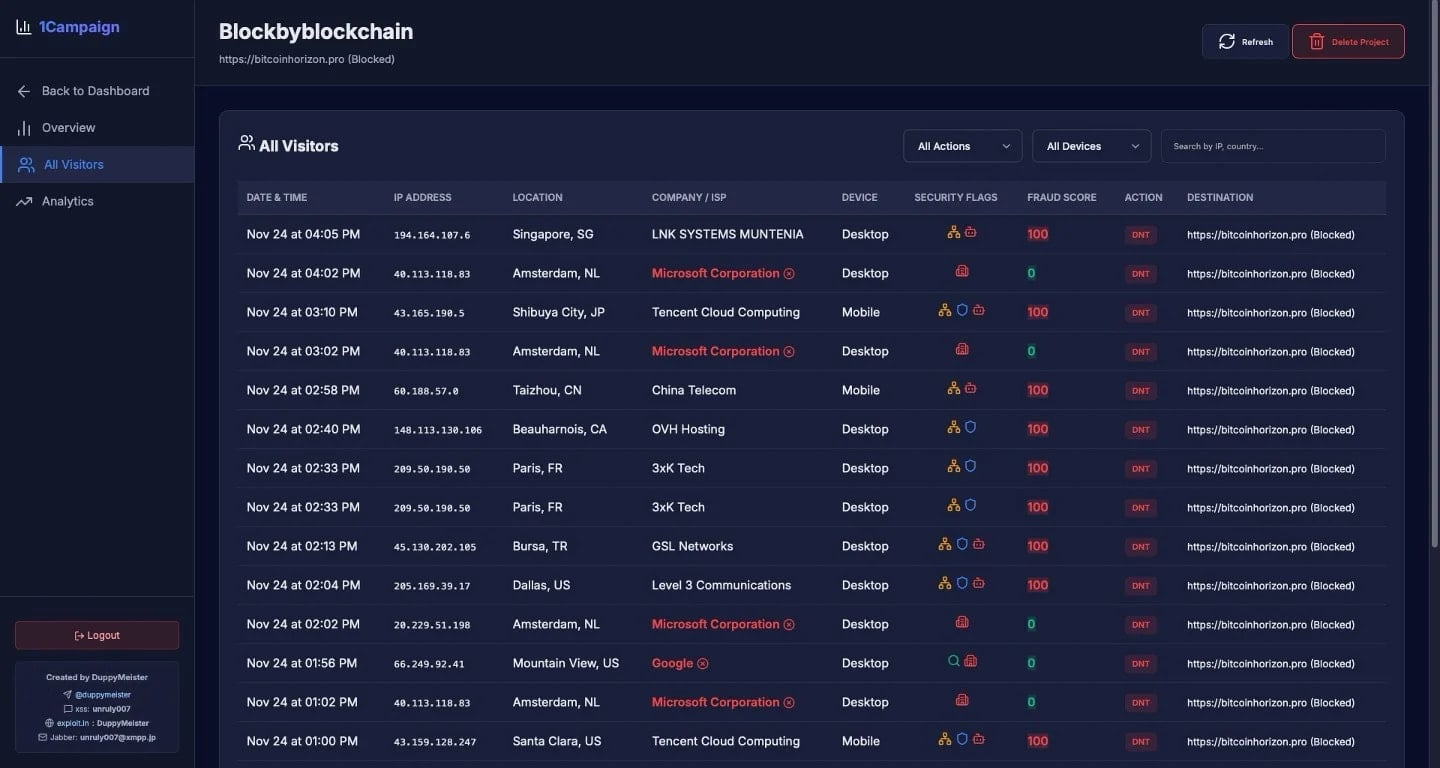
1Campaign supplies “prospects” with a user-friendly dashboard the place they will get an outline of their operations and set the parameters for his or her campaigns.

Supply: Varonis
The platform can filter guests in actual time, directing site visitors to touchdown pages primarily based on predefined standards, together with geography, web service supplier (ISP), and system traits.
The researchers say that this focused strategy permits attackers to focus on customers in areas the place the phishing lure is related, whereas filtering out site visitors from nations with the next chance of safety scrutiny or scanning exercise.
In a single occasion, Varonis noticed aggressive filtering that blocked 99.4% of 1,676 guests accessing the malicious adverts. This interprets into successful price of simply 0.6%, or 10 guests.
Supply: Varonis
The system evaluates every customer and assigns a fraud threat rating between 0 and 100. This displays the chance of non-genuine guests, and is derived from checking infrastructure particulars corresponding to cloud suppliers, information facilities, VPNs, and safety distributors.
“Guests from Microsoft Company, Google, Tencent Cloud Computing, OVH Internet hosting, and different cloud suppliers are robotically flagged with excessive fraud scores and blocked,” Varonis says in a report right this moment.
Primarily based on IP handle ranges, ISP, and behavioral patterns, the system may decide if the malicious adverts are accessed by safety scanners.
Varonis has noticed site visitors linked to 1Campaign being distributed in the US, Canada, the Netherlands, China, Germany, France, Japan, Hungary, and Albania.
The cybercrime platform additionally affords a Google Adverts launcher software that helps operators launch each malicious and benign campaigns. The developer claims that this software allows bypassing Google’s coverage limitations and impersonating legit manufacturers in adverts.
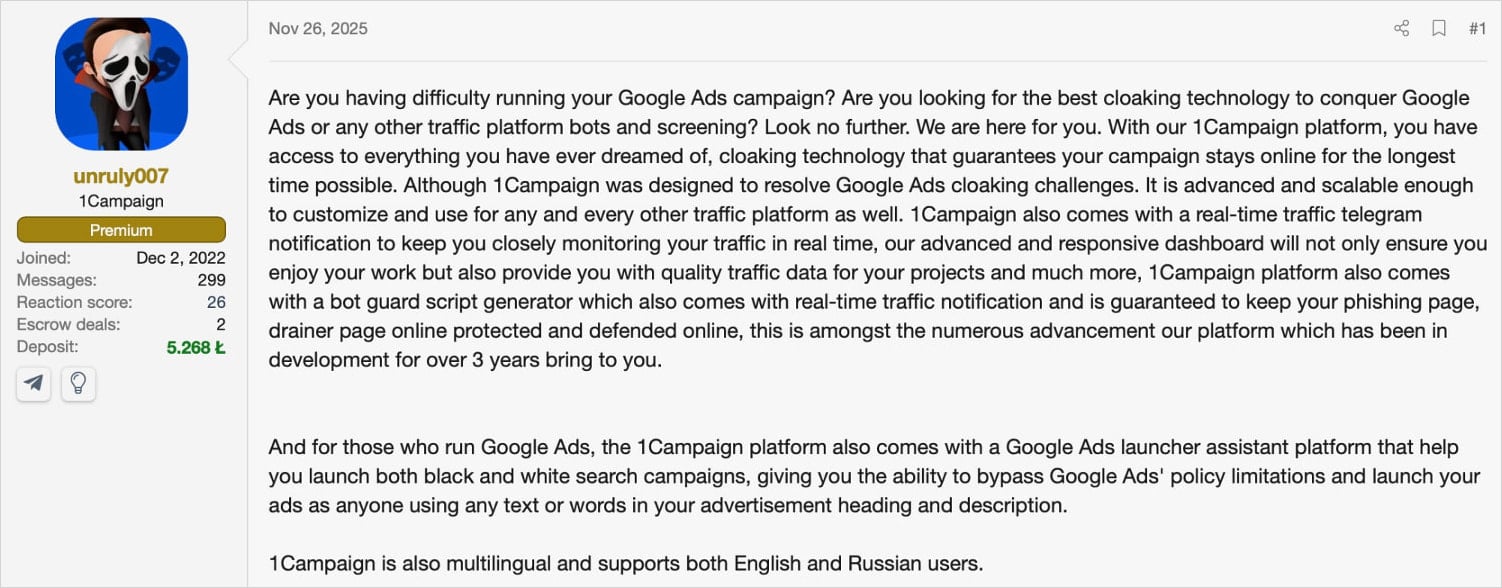
Regardless of Google introducing a number of safeguards, its advert platform remains to be used to advertise fraud, malware, and crypto-drainers. 1Campaign stands out, although, as it’s designed particularly to launch malicious adverts that move Google’s automated inspection and certain survive till victims report them or the marketing campaign is reported manually.
Such a cloaking system makes static URL scanning much less efficient. Varonis says that utilizing life like browser fingerprints and patterns that mimic human interplay would render higher evaluation and detection outcomes.
For automated detection, Varonis recommends rotating by a various IP pool and user-agent configurations to keep away from constant fingerprinting.
Customers are suggested to keep away from promoted search outcomes, or no less than deal with them with suspicion, and bookmark official software program distribution channels.
Double-checking the URL within the handle bar can also be advisable earlier than getting into account credentials or different delicate data.




