The deliberate motion to obfuscate supply code refers back to the intentional transformation of programmatic logic right into a kind that’s exceedingly tough for people to interpret, whereas remaining functionally equivalent from the standpoint of machine execution. This method, whereas deceptively easy in conceptual premise, occupies an important place on the intersection of cybersecurity, mental property safety, and strategic enterprise operations within the digital age.
Obfuscation shouldn’t be encryption, although the 2 are sometimes conflated. Whereas encryption renders knowledge completely unreadable till decrypted—thereby necessitating further runtime processes to revive operability—obfuscation preserves the code’s machine operability whereas concurrently degrading its legibility to human observers. It’s, in essence, a type of uneven info structure: intelligible to the machine, opaque to the adversary.
Builders and expertise companies make use of code obfuscation for quite a lot of interrelated functions. Primarily, it serves to safeguard proprietary logic from reverse engineering, thereby impeding mental property theft. It additionally introduces substantial obstacles to tampering and unauthorized modification—notably necessary in contexts the place software program is deployed in hostile or semi-trusted environments. Moreover, obfuscation can obscure business-critical algorithms, knowledge flows, or safety mechanisms, thus elevating the price of cyber intrusion for would-be attackers.
Within the aggressive milieu of up to date expertise startups—the place first-mover benefit is commonly fleeting and codebases might characterize the totality of a agency’s monetizable belongings—the safety of supply code shouldn’t be merely a technical greatest follow; it’s a fiduciary accountability. The usage of code obfuscation ought to be seen as one part of a broader strategic posture encompassing safe improvement practices, mental property administration, and cybersecurity threat mitigation.
Programmers obfuscate (from the Latin obfuscātus) supply code to stop it from being stolen, make it harder to tamper with, and safe helpful or delicate details about the operate of the code.
In contrast to encryption, obfuscation solely makes knowledge obscure for people. For the reason that knowledge stays machine-readable, obfuscating supply code protects the code from cybercriminals with out including additional steps like de-encryption which will decelerate this system’s run time.
Within the aggressive world of technology-based startups, mental property is commonly the highest-value asset an organization owns. Implementing obfuscation strategies is a necessary step to defending IP from theft by rivals.
Why Is Supply Code So Arduous to Defend?
Sometimes, helpful knowledge and data are protected by proscribing entry.
For instance, delicate consumer recordsdata are stored safe in password-protected, encrypted accounts which are tough or unattainable for criminals to breach.
Nevertheless, supply code is seen to anybody utilizing a program, so entry prevention strategies can’t be used to safe the code or any info saved inside it.
As an alternative, programmers can “disguise” the code through obfuscation in order that it seems to be nonsensical to people however remains to be machine-readable. This can stop hackers from misusing the code whereas permitting this system to run as designed.

Obfuscation software program can be utilized to routinely apply totally different obfuscation strategies to sections of code, or programmers can choose parts of knowledge and obfuscate them by hand.
How you can Obfuscate Supply Code & Information
There are lots of totally different strategies for obfuscating knowledge. To strengthen code protections, programmers can combine and match totally different strategies all through the code to make it much more tough for hackers to learn.
Beneath, we’ve outlined a few of the extra widespread strategies for successfully obfuscating knowledge.
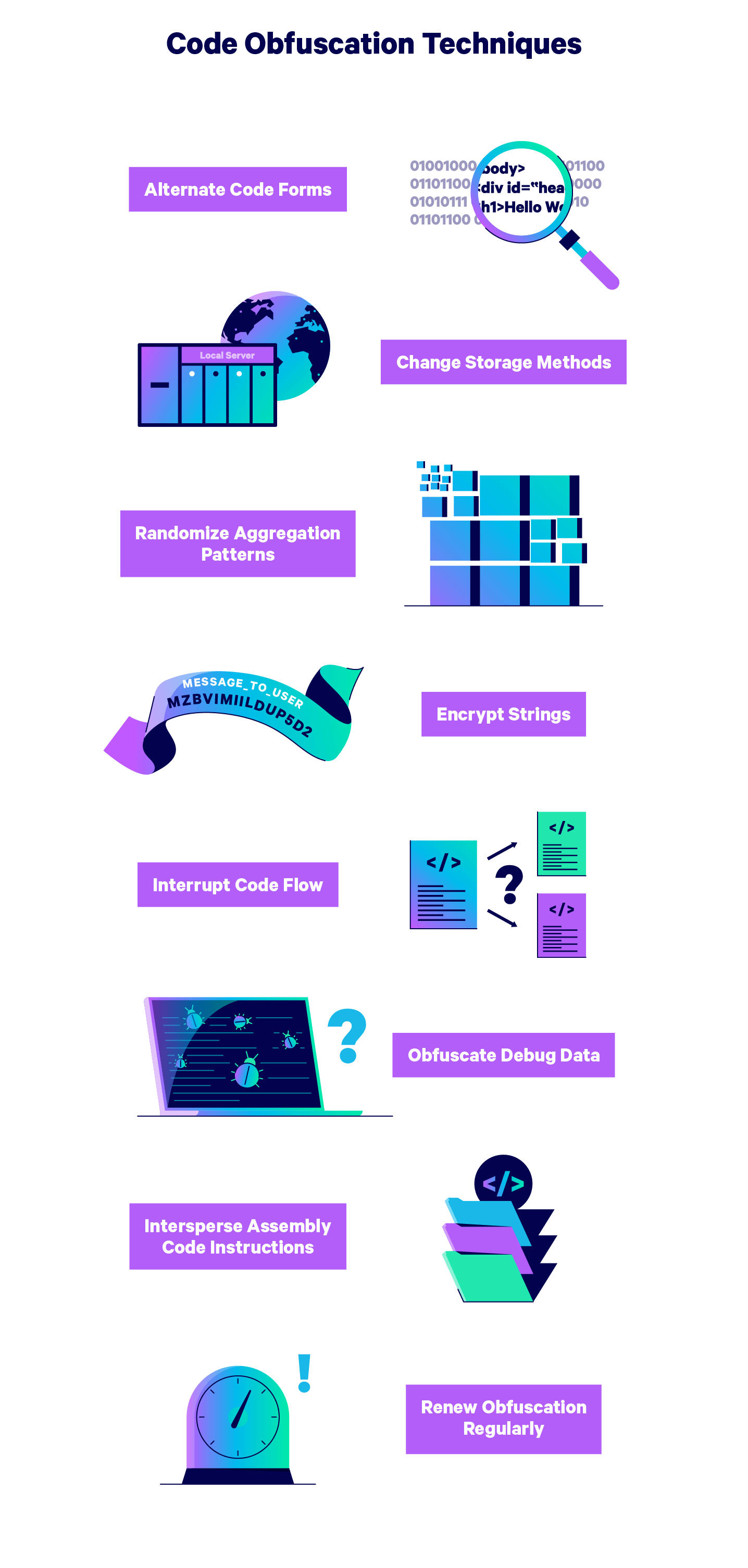
1. Alternate Code Types
Translate brief sections of the code into totally different varieties all through this system to make deciphering it harder with out affecting run time.
For instance, you’ll be able to translate elements of your code to binary language, or change a operate with a desk lookup of all doable values the operate may produce.
2. Change Up Information Storage Strategies
Make your knowledge harder to learn by basically “hiding” your knowledge utilizing totally different reminiscence varieties and areas. Alternate between storing variables domestically and globally to hide how the variables work collectively.
You too can randomize the addresses at which elements of code are positioned to create a further degree of confusion and make the code harder to learn.
3. Randomize Aggregation Patterns
One other approach to confuse hackers is by packaging your knowledge in random sizes. For instance, you may break arrays into an unnecessarily excessive variety of sub-arrays to confuse any reverse engineering makes an attempt.
4. Encrypt Strings
Although encryption isn’t an efficient methodology for safeguarding your total supply code, you should use encryption as a part of the obfuscation course of with out slowing this system.
Choose particular person keys, code strings, and different items of data to encrypt to create hacker “blind spots” within the code.
5. Interrupt Code Stream
Add pointless statements or “useless code” to your program to make it tough to determine what elements of the code include actual knowledge.
Dummy code will also be used to hide the pathways by which program management is handed between sections of the codebase.
6. Take away Debug Information
Debugging info can be utilized by hackers to reverse engineer a program’s supply code, so it’s sensible to obfuscate debug info by altering line numbers and file names.
Alternatively, you’ll be able to completely take away debug info out of your program.
7. Obfuscate Meeting Code
Focus obfuscation efforts on meeting code to make it particularly tough to reverse engineer.
Many programmers like to cover meeting code inside different code in a form of Russian nesting doll sample referred to as the “jump-in-the-middle” method, which is able to stop a disassembler from producing the proper outputs.
8. Renew Obfuscation Techniques Often
Make use of a schedule of obfuscation tactic renewal and refresh the strategies you’ve used all through the code.
Fluctuate the items of data you’ve hidden and encrypted, and alternate between ways in several parts of the code.
Utilizing a number of ways to completely obfuscate supply code and refreshing obfuscation commonly will shield your startup’s IP from nearly all of potential hacks.
Nevertheless, no safety measure can assure your startup’s security, which is why it’s necessary to enrich your cybersecurity precautions with complete tech insurance coverage that ought to embody cyber legal responsibility, tech errors & omissions, and business crime insurance coverage to guard your tech startup from all doable types of cyberattacks.
By pairing your programmer’s assault prevention efforts with safety towards a worst-case state of affairs, you’ll have the ability to preserve your organization secure it doesn’t matter what occurs.
To study extra concerning the insurance policies which are proper for your enterprise, try Embroker’s digital insurance coverage platform.


