
Wynn Resorts has confirmed {that a} hacker stole worker knowledge from its programs after the corporate was listed on the ShinyHunters extortion gang’s knowledge leak website.
In a press release shared at present, the corporate stated it activated its incident response procedures and launched an investigation, with help from exterior cybersecurity consultants, after discovering the breach.
“We’ve discovered that an unauthorized third celebration acquired sure worker knowledge,” reads a press release shared with BleepingComputer.
“Upon discovery, we instantly activated our incident response protocols and launched a radical investigation with the assistance of exterior cybersecurity consultants.”
Whereas Wynn has not acknowledged whether or not it paid a ransom to forestall the info leak, the corporate stated the attackers confirmed the stolen knowledge had been deleted. In previous extortion instances, menace actors have usually solely claimed knowledge was deleted after reaching an settlement with a sufferer.
“The unauthorized third celebration has acknowledged that the stolen knowledge has been deleted. We’re monitoring and to this point haven’t seen any proof that the info has been revealed or in any other case misused,” the assertion continued.
The corporate added that the incident didn’t impression visitor operations or its bodily properties, which stay absolutely operational, and that it’s providing complimentary credit score monitoring and id safety providers to staff.
ShinyHunters leak website itemizing
This assertion comes after Wynn Resorts appeared on the ShinyHunters knowledge leak website on Thursday.
Within the menace actors’ put up, the group claimed it had stolen “PII (SSNs, and so on) and worker knowledge” and warned the corporate to make contact earlier than February 23, 2026, or the info could be revealed.
“Over 800k information containing PII(SSNs, and so on) and worker knowledge have been compromised,” reads the now-deleted put up on ShinyHunters knowledge leak website.
“It is a closing warning to achieve out by 23 Feb 2026 earlier than we leak together with a number of annoying (digital) issues that’ll come your means. Make the appropriate choice, do not be the subsequent headling.”
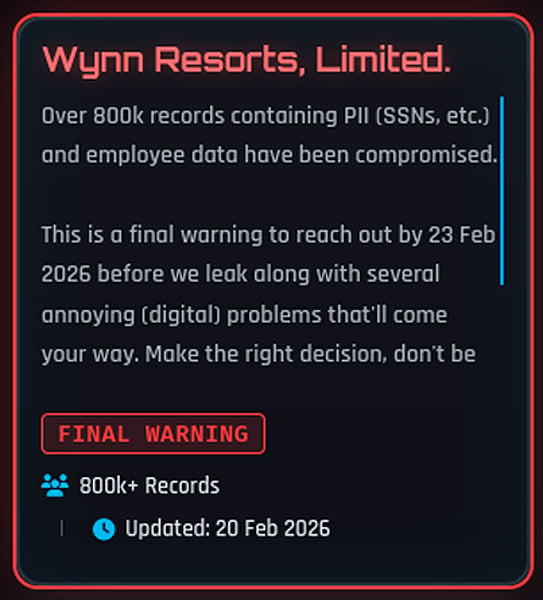
Shortly after, the Wynn entry was faraway from the location, a transfer that always happens when negotiations are underway or claims are disputed.
Wynn Resorts didn’t reply questions on whether or not a ransom was paid or how many individuals had been affected. Equally, ShinyHunters informed BleepingComputer that they’d no touch upon whether or not they acquired a fee.
Nevertheless, the menace actors did beforehand declare to have stolen the info from the corporate’s Oracle PeopleSoft surroundings.
ShinyHunters is an information extortion group recognized for breaching organizations and threatening to publish stolen knowledge until a ransom is paid.
The group has beforehand claimed duty for a number of high-profile knowledge theft incidents and has operated throughout varied underground boards and extortion portals over time.
Final yr, ShinyHunters carried out a widespread marketing campaign to steal Salesforce knowledge, focusing on quite a few firms by social engineering and stolen third-party OAuth tokens.
In latest weeks, ShinyHunters has claimed duty for a wave of different safety breaches, together with Panera Bread, Betterment, SoundCloud, Canada Goose, PornHub, and on-line relationship large Match Group.
A few of the victims had been compromised by voice phishing (vishing) assaults focusing on single sign-on (SSO) accounts at Google, Microsoft, and Okta, the place the menace actors posed as IT assist workers to trick staff into coming into credentials and multi-factor authentication (MFA) codes on phishing websites.
As BleepingComputer first reported, the ShinyHunters group extra not too long ago adopted system code vishing to acquire Microsoft Entra authentication tokens.
After stealing their targets’ credentials and auth codes, the menace actors hijack the victims’ SSO accounts to steal knowledge from related SaaS purposes equivalent to Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, and plenty of others.
Trendy IT infrastructure strikes quicker than handbook workflows can deal with.
On this new Tines information, learn the way your workforce can scale back hidden handbook delays, enhance reliability by automated response, and construct and scale clever workflows on prime of instruments you already use.




