Data is energy and collaboration is essential for organizations to repeatedly adapt and enhance their safety measures as a way to keep forward of cybercriminals. An efficient strategy to keep forward is by enhancing a company’s safety posture by way of cybersecurity menace intelligence sharing. By exchanging details about potential and current cyber threats with different organizations, people, or entities, organizations can higher perceive the menace panorama and make knowledgeable choices about their safety methods. On this article, we’ll discover what menace intelligence sharing is and supply steering on beginning your individual program.
How menace intelligence sharing works
Risk intelligence sharing may be in comparison with a neighborhood watch program, the place neighborhood members collaborate and share details about suspicious actions, potential threats, and crime incidents to enhance the general security and safety of the neighborhood.
Equally, menace intelligence sharing is a collaborative course of that permits organizations to alternate data resembling indicators of compromise (IoCs), ways, methods, and procedures (TTPs), and vulnerabilities between one another. It entails gathering menace intelligence from numerous sources, resembling inside community logs, safety instruments, open-source intelligence (OSINT), industrial menace intelligence feeds, and industry-specific sharing communities like Data Sharing and Evaluation Facilities (ISACs).
The collected information is then analyzed to establish patterns, traits, and actionable insights, which assist organizations perceive the menace panorama and make knowledgeable choices about their safety methods.
Addressing menace intelligence sharing authorized, regulatory, and privateness considerations
To take care of privateness and foster collaboration, organizations ought to set up clear tips and use standardized protocols like Structured Risk Data Expression (STIX) or Trusted Automated eXchange of Indicator Data (TAXII) when sharing menace intelligence exterior the corporate. This collaborative method will finally enhance the safety posture of all taking part organizations.
Additionally, taking part organizations ought to work intently with authorized and compliance groups to grasp the necessities and set up tips for sharing menace intelligence whereas adhering to information privateness laws and industry-specific compliance requirements. Pointers ought to embrace sanitization, anonymization, and encryption methods to guard delicate data from being publicly disclosed.
How menace intelligence information is structured
Standardized codecs and languages, resembling STIX or TAXII, are used to construction the info, guaranteeing consistency, readability, and straightforward processing by totally different instruments and methods. Organizations share this menace intelligence by way of numerous channels, together with e mail, file transfers, net platforms, or automated protocols like STIX and TAXII. Shared intelligence is then consumed, and applicable countermeasures are applied based mostly on the insights gained.
Organizations collaboratively and repeatedly monitor the effectiveness of their menace intelligence sharing efforts, offering suggestions to one another and refining their processes to enhance the standard and relevance of the shared information.
Advantages of taking part in menace intelligence sharing
Simply as neighborhood watch packages promote involvement by way of neighborhood constructing, shared accountability, and mutual profit, menace intelligence sharing packages encourage participation by doing the next:
- Elevating consciousness of the significance of collaboration and data sharing in enhancing a company’s safety posture.
- Establishing communication channels and platforms for sharing menace intelligence, resembling emails, net platforms, or automated protocols.
- Present steering and help to individuals by way of designated groups or people accountable for managing the menace intelligence sharing program.
- Providing coaching and academic supplies on menace intelligence sharing finest practices, instruments, and frameworks.
- Constructing relationships with {industry} companions like ISAC, or different menace intelligence sharing communities to alternate data and be taught from one another’s experiences.
- Encourages collaboration by pooling sources, information, and experience, collectively.
By enhancing group’s menace detection and response capabilities, their total safety posture and resilience towards cyberattacks will increase.
What the menace intelligence sharing course of seems like
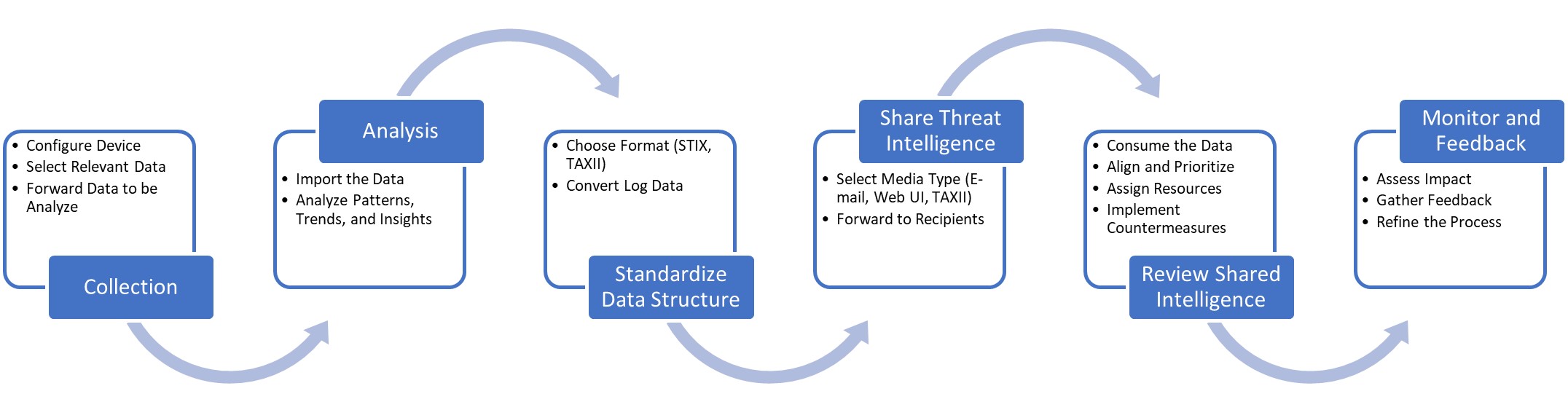
Assortment
The method begins with the gathering of menace intelligence from a variety of sources, together with inside community logs, safety instruments, open-source intelligence (OSINT), industrial menace intelligence feeds, and industry-specific sharing communities or Data Sharing and Evaluation Facilities (ISACs).
Evaluation
The collected information is then analyzed to establish patterns, traits, and actionable insights, serving to organizations higher perceive the menace panorama and make knowledgeable choices about their safety methods.
Standardize information construction
To make sure consistency, readability, and straightforward processing by totally different instruments and methods, the menace intelligence information is structured utilizing standardized codecs and languages, resembling STIX or TAXII.
Share menace intelligence
Organizations improve their cybersecurity efforts by way of sharing menace intelligence. They’ll alternate data by way of numerous channels, resembling e mail, file transfers, net platforms, or automated protocols.
Overview shared intelligence
The shared intelligence is built-in into the receiving group’s safety infrastructure, resembling Safety Incident and Occasion Administration “SIEM” methods, Intrusion Detection System/Intrusion Prevention System “IDS/IPS”, or Risk Intelligence Platforms “TIP”, and is used to tell safety methods, prioritize sources, and implement countermeasures.
Monitor and suggestions
Lastly, organizations repeatedly monitor the effectiveness of their menace intelligence sharing efforts, present suggestions to their companions, and refine their processes to enhance the standard and relevance of the shared information.
Beginning your individual menace intelligence sharing program
Implementing a menace intelligence sharing program strategically bolsters the group’s safety posture and resilience towards evolving cyber threats. The next steps can be utilized as a framework create a menace intelligence sharing program:
- Perceive the basics of menace intelligence sharing, together with widespread frameworks and requirements like STIX and TAXII.
- Outline roles and duties, workflows, and communication channels to raised implement and handle the menace intelligence sharing program.
- Assess your group’s particular menace intelligence sharing necessities, resembling the kind of menace information you wish to share, the sources of this information, and the specified stage of automation for sharing and consuming menace intelligence.
- Establish potential companions for sharing menace intelligence, resembling {industry} friends, ISACs, or industrial menace intelligence suppliers.
- Combine menace intelligence sharing capabilities into your current safety infrastructure, resembling safety data and occasion administration (SIEM) methods, intrusion detection and prevention methods (IDS/IPS), or menace intelligence platforms (TIPs).
- Develop inside processes and tips for creating, sharing, and consuming menace intelligence inside your group, together with roles and duties, workflows, and communication channels.
- Constantly monitor the effectiveness of your menace intelligence sharing efforts, collect suggestions from individuals, and refine your processes to enhance the standard and relevance of the shared information.
Overcoming the challenges of beginning a menace intelligence program
A number of {industry} requirements and compliance frameworks have revealed or constructed into their packages the flexibility to soundly set up a menace intelligence sharing program for a company. NIST, ISO, FIRST, ENISA, and CIS all have insights, tips, and finest practices associated to cybersecurity collaboration and data sharing that may complement and help a company establishing a menace intelligence sharing program.
One of many key challenges is elevating consciousness and understanding of the advantages of menace intelligence sharing, together with the most effective practices, instruments, and frameworks out there. Organizations can deal with this by way of complete coaching and academic supplies for his or her safety groups and stakeholders.
Organizations can foster a tradition of belief and collaboration by creating partnerships with {industry} friends, ISACs, or different menace intelligence sharing communities, emphasizing the mutual advantages of sharing and collaboration. Allocating essential sources, resembling personnel, expertise, and funding, is essential for establishing a sturdy menace intelligence sharing program. This may occasionally require acquiring govt sponsorship and help to make sure organizational dedication and ample useful resource allocation.
Organizations deal with integration points by deciding on instruments and platforms which can be appropriate with their present methods and help standardized codecs like STIX or TAXII. Additionally, organizations ought to spend money on adopting and implementing standardized frameworks, guaranteeing constant and readable information throughout totally different instruments and methods.
Making certain the standard and relevance of shared information may be addressed by implementing processes to filter out noise, validate the accuracy of shared information, and prioritize probably the most related threats. As well as, organizations that set up a steady suggestions loop to enhance the menace intelligence sharing program is crucial. That is achieved by monitoring the effectiveness of this system, gathering suggestions from individuals, and refining processes to enhance the standard and relevance of the shared information.
Conclusion
Cybersecurity menace intelligence sharing is a robust software for organizations to collaboratively deal with the challenges posed by an ever-evolving menace panorama. Just like the neighborhood watch, fostering a way of neighborhood, shared accountability, and mutual profit, creates a robust and efficient menace intelligence sharing program that enhances everybody’s total safety posture and resilience towards cyber threats.