The Android banking trojan referred to as SpyNote has been dissected to disclose its various information-gathering options.
Usually unfold by way of SMS phishing campaigns, assault chains involving the spy ware trick potential victims into putting in the app by clicking on the embedded hyperlink, in keeping with F-Safe.
Apart from requesting invasive permissions to entry name logs, digital camera, SMS messages, and exterior storage, SpyNote is thought for hiding its presence from the Android dwelling display screen and the Recents display screen in a bid to make it tough to keep away from detection.
“The SpyNote malware app may be launched by way of an exterior set off,” F-Safe researcher Amit Tambe stated in an evaluation printed final week. “Upon receiving the intent, the malware app launches the principle exercise.”
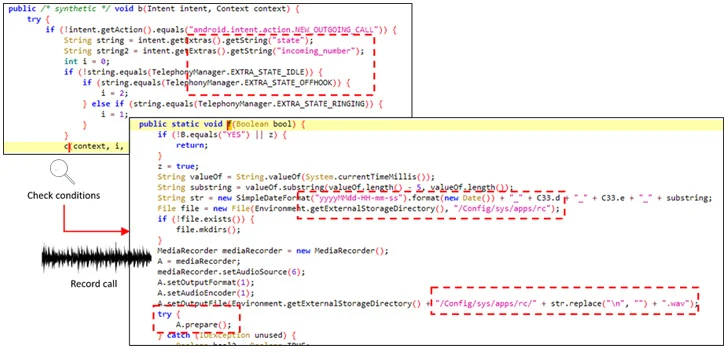
However most significantly, it seeks accessibility permissions, subsequently leveraging it to grant itself extra permissions to document audio and cellphone calls, log keystrokes, in addition to seize screenshots of the cellphone by way of the MediaProjection API.
A better examination of the malware has revealed the presence of what are referred to as diehard providers that goal to withstand makes an attempt, both made by the victims or by the working system, at terminating it.
That is completed by registering a broadcast receiver that is designed to restart it robotically at any time when it’s about to be shut down. What’s extra, customers who try and uninstall the malicious app by navigating to Settings are prevented from doing so by closing the menu display screen by way of its abuse of the accessibility APIs.
“The SpyNote pattern is spy ware that logs and steals quite a lot of info, together with key strokes, name logs, info on put in functions, and so forth,” Tambe stated. “It stays hidden on the sufferer’s system making it difficult to note. It additionally makes uninstallation extraordinarily difficult.”
“The sufferer is ultimately left solely with the choice of performing a manufacturing facility reset, shedding all knowledge, thereby, within the course of.”
The disclosure comes because the Finnish cybersecurity agency detailed a bogus Android app that masquerades as an working system replace to entice targets into granting it accessibility providers permissions and exfiltrate SMS and financial institution knowledge.