The U.S. Division of Well being and Human Providers (HHS) warned hospitals this week to patch the crucial ‘Citrix Bleed’ Netscaler vulnerability actively exploited in assaults.
Ransomware gangs are already utilizing Citrix Bleed (tracked as CVE-2023-4966) to breach their targets’ networks by circumventing login necessities and multifactor authentication protections.
HHS’ safety crew, the Well being Sector Cybersecurity Coordination Middle (HC3), issued a sector alert on Thursday urging all U.S. healthcare organizations to safe weak NetScaler ADC and NetScaler Gateway gadgets in opposition to ransomware gangs’ assaults.
“The Citrix Bleed vulnerability is being actively exploited, and HC3 strongly urges organizations to improve to stop additional harm in opposition to the Healthcare and Public Well being (HPH) sector. This alert comprises info on assault detection and mitigation of the vulnerability,” HC3 warned.
“HC3 strongly encourages customers and directors to overview these really useful actions and improve their gadgets to stop severe harm to the HPH sector.”
Earlier than this, Citrix issued two warnings asking admins to right away patch their home equipment. It additionally reminded admins to kill all energetic and protracted classes to stop attackers from stealing authentication tokens even after putting in the safety updates.
Not too long ago, CISA and the FBI additionally cautioned concerning the LockBit ransomware gang becoming a member of the assaults. One among their victims, aerospace big Boeing, shared particulars on how a LockBit affiliate breached its community in October utilizing a Citrix Bleed exploit.
1000’s of servers uncovered, many already breached
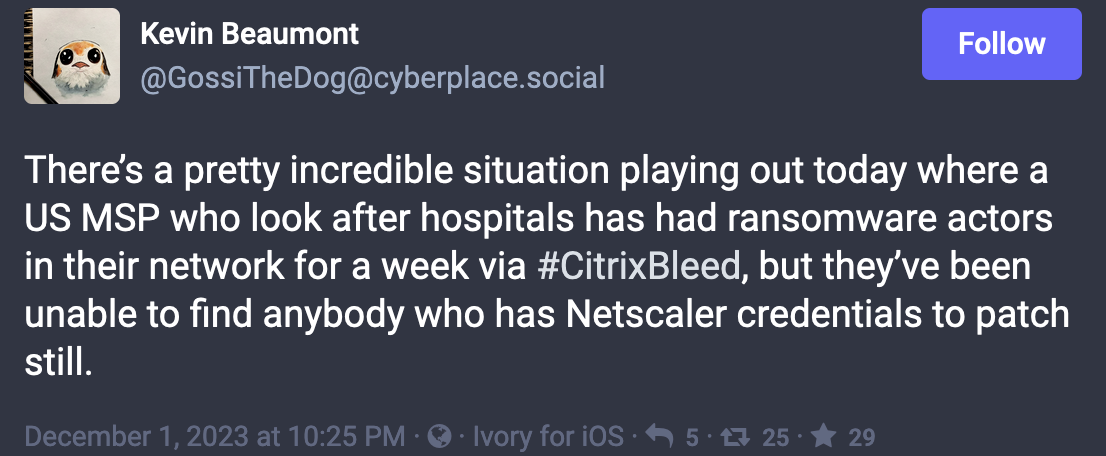
Cybersecurity knowledgeable Kevin Beaumont has been monitoring and analyzing cyberattacks in opposition to varied victims worldwide, together with Boeing, the Industrial and Industrial Financial institution of China (ICBC), DP World, and Allen & Overy, and located they have been all doubtless breached utilizing Citrix Bleed exploits.
Beaumont revealed on Friday that a U.S.-based managed service supplier (MSP) suffered a ransomware assault by a gaggle exploiting a Citrix Bleed vulnerability over every week in the past.
The MSP remains to be working to safe its weak Netscaler home equipment, which may doubtlessly expose its shoppers’ networks and knowledge to additional assaults.
Citrix patched the flaw in early October, however Mandiant later revealed that it has been underneath energetic exploitation as a zero-day since at the least late August 2023.
On October 25, exterior assault floor administration firm AssetNote launched a CVE-2023-4966 proof-of-concept exploit exhibiting how session tokens could be stolen from unpatched Citrix home equipment.
In mid-November, Japanese risk researcher Yutaka Sejiyama informed BleepingComputer that over 10,000 Citrix servers (lots of them belonging to crucial organizations in lots of nations) have been nonetheless weak to Citrix Bleed assaults, a couple of month after the crucial flaw was patched.
“This pressing warning by HC3 signifies the seriousness to the Citrix Bleed vulnerability and the pressing must deploy the prevailing Citrix patches and upgrades to safe our programs,” mentioned John Riggi, a cybersecurity and danger advisor for the American Hospital Affiliation, a healthcare trade commerce group that represents 5,000 hospitals and healthcare suppliers throughout the U.S.
“This case additionally demonstrates the aggressiveness by which overseas ransomware gangs, primarily Russian-speaking teams, proceed to focus on hospitals and well being programs. Ransomware assaults disrupt and delay well being care supply, inserting affected person lives at risk.”