Background
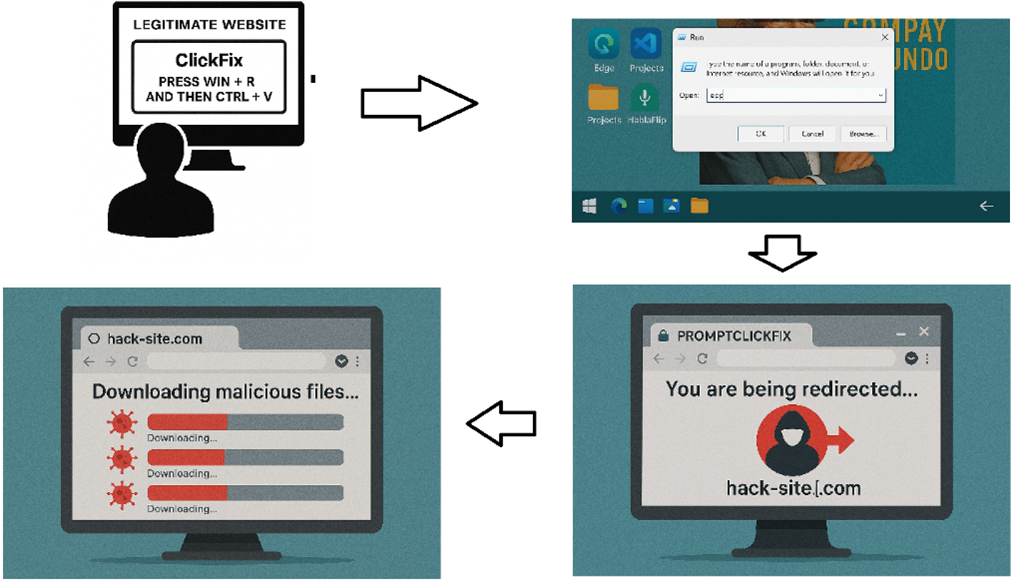
ClickFix has shortly change into a rampant social-engineering tactic. First noticed again in October 2023, it goals to trick customers into pasting instructions into the run dialog field beneath the guise of verifying the person’s connection and authenticity to the area. Given its ease of use and skill to bypass technical safety measures, adoption of ClickFix has been rising at an alarming charge. [1]
Government Abstract
This investigation started after a person was noticed navigating to a respectable web site that prompted the person with a faux Captcha immediate. As soon as the Pretend Captcha immediate directions had been carried out, a curl command to a malicious area led to malicious scripts and file downloads on the person’s asset. A menace actor is then noticed performing area degree reconnaissance from the person’s machine earlier than being caught and locked out by the LevelBlue MDR SOC group. This menace actor has been related to the Interlock ransomware group, with Indicators of Compromise recognized by the LevelBlue Open Menace Trade (OTX) and different Open-Supply Intelligence (OSI) sources equivalent to Sekoia.
The Interlock ransomware group was first noticed in September 2024. In contrast to most ransomware teams seen right now that make use of Ransomware as a Service (RaaS) fashions, this was an impartial group. They gained notoriety again in October 2024 after they claimed accountability for the Texas Tech College Well being Sciences Middle incident that compromised the info of roughly 1.5 million sufferers.
In January 2025, researchers at Sekoia noticed Interlock increasing their techniques and leveraging the Social Engineering approach now referred to as ClickFix. [2]
Investigation
The Stage Blue MDR group noticed two alarms on the identical endpoint from Sentinel One which prompted additional investigation. Through the investigation, our analysts uncovered the menace actors’ techniques, methods, and procedures (TTPs) and recognized indicators of compromise (IOCs) related to the Interlock ransomware group. As a result of swift motion of the LevelBlue MDR group, the assault was contained, and the hashes from the investigation have been added to the blocklist inside SentinelOne. Click on right here to learn the complete weblog and study key takeaways from LevelBlue’s investigation, together with suggestions to stop these assaults from affecting your group.
[2] https://weblog.sekoia.io/interlock-ransomware-evolving-under-the-radar
The content material offered herein is for normal informational functions solely and shouldn’t be construed as authorized, regulatory, compliance, or cybersecurity recommendation. Organizations ought to seek the advice of their very own authorized, compliance, or cybersecurity professionals relating to particular obligations and danger administration methods. Whereas LevelBlue’s Managed Menace Detection and Response options are designed to assist menace detection and response on the endpoint degree, they don’t seem to be an alternative choice to complete community monitoring, vulnerability administration, or a full cybersecurity program.


