Extra Put up Contributors: Austin Pham, Tony Iacobelli
Cisco and Splunk, collectively, elevate the SOC’s Incident Detection and Response expertise to the subsequent stage by combining applied sciences from either side that present a good higher single pane of glass view to threats in actual time. Applied sciences similar to Cisco XDR and Safety Cloud and Splunk Enterprise Safety, Splunk Assault Analyzer, and Splunk Cloud are the right pairing to cut back the Imply time to Detect, Reply, Comprise, and Eradicate (MTTx) considerably.
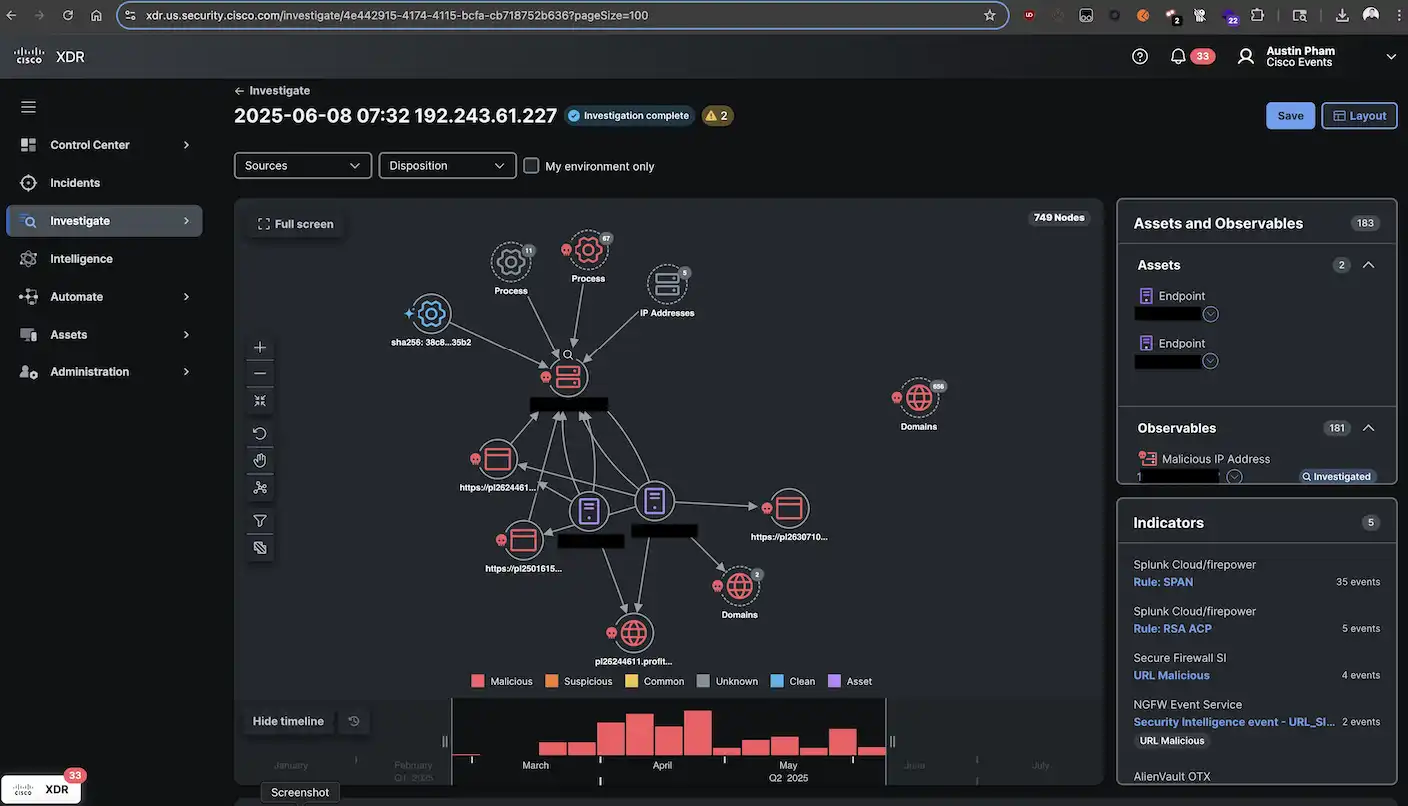
Constructing out a SOC Triage Heart Dashboard (initially created by Matthew Bellezza from the Splunk Heart of Excellence) in Splunk Enterprise Safety that aggregates tens of millions of occasion knowledge from Endace and Cisco community merchandise enable the Cisco Stay San Diego 2025 SOC analyst to really feel extra empowered to shortly triage and reply to safety occasions to defend CLUS attendees and employees from threats – quickly placing a cease to all malicious exercise.
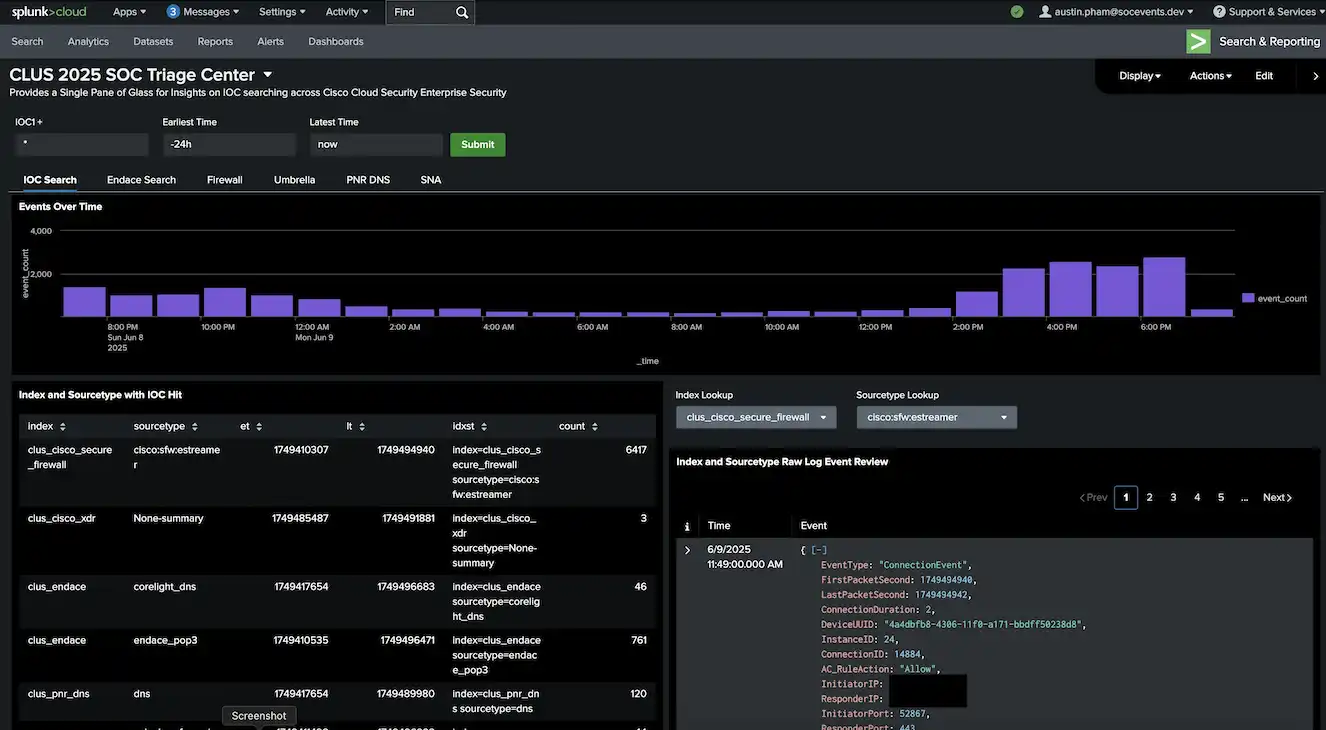
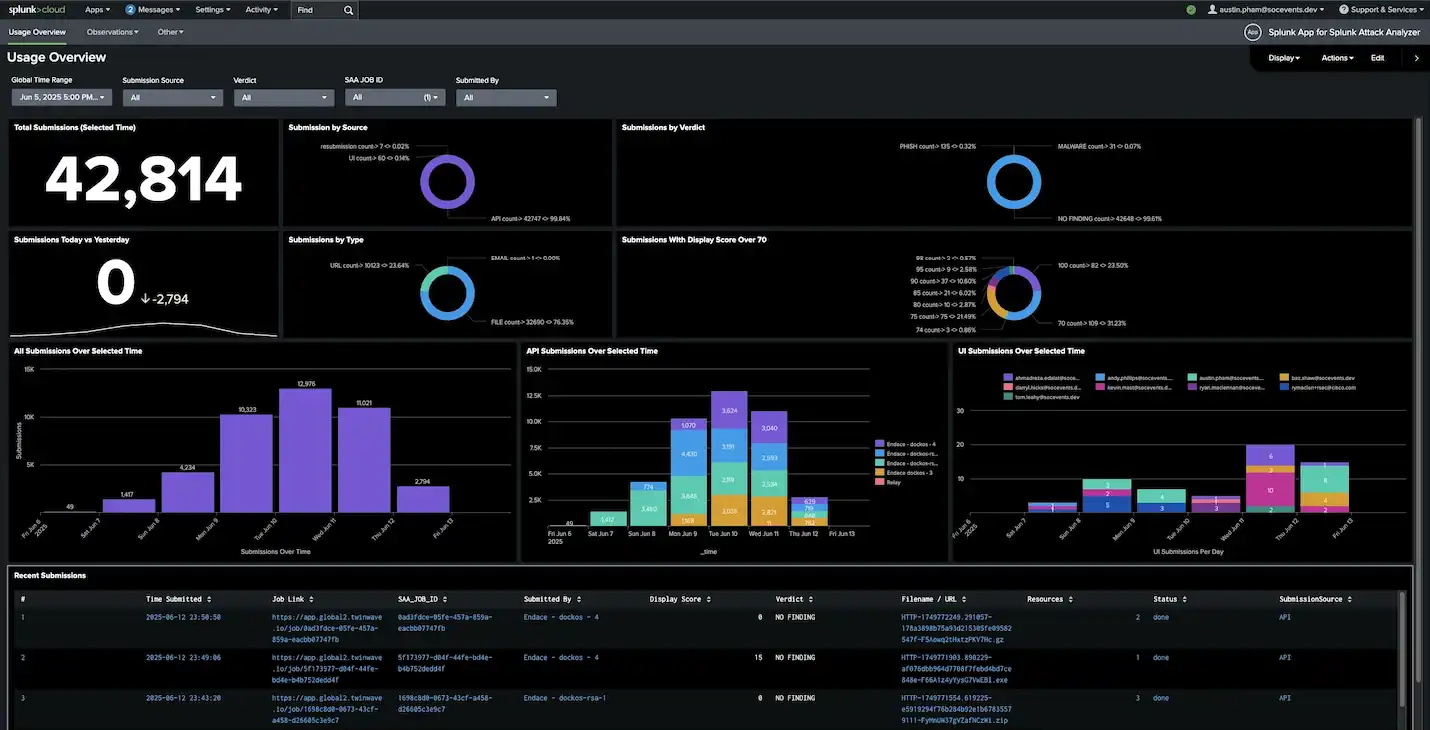
Splunk Assault Analyzer paired with Safe Malware Analytics, using XDR and Endace, gives holistic static and dynamic evaluation in the case of phishing domains, file evaluation, and malware sandbox detonation — streaming the occasions in actual time to the Cisco Stay flooring.
We additionally created a Phished Manufacturers dashboard to determine when attackers have been making an attempt to make use of related showing domains to lure victims into offering their credentials.

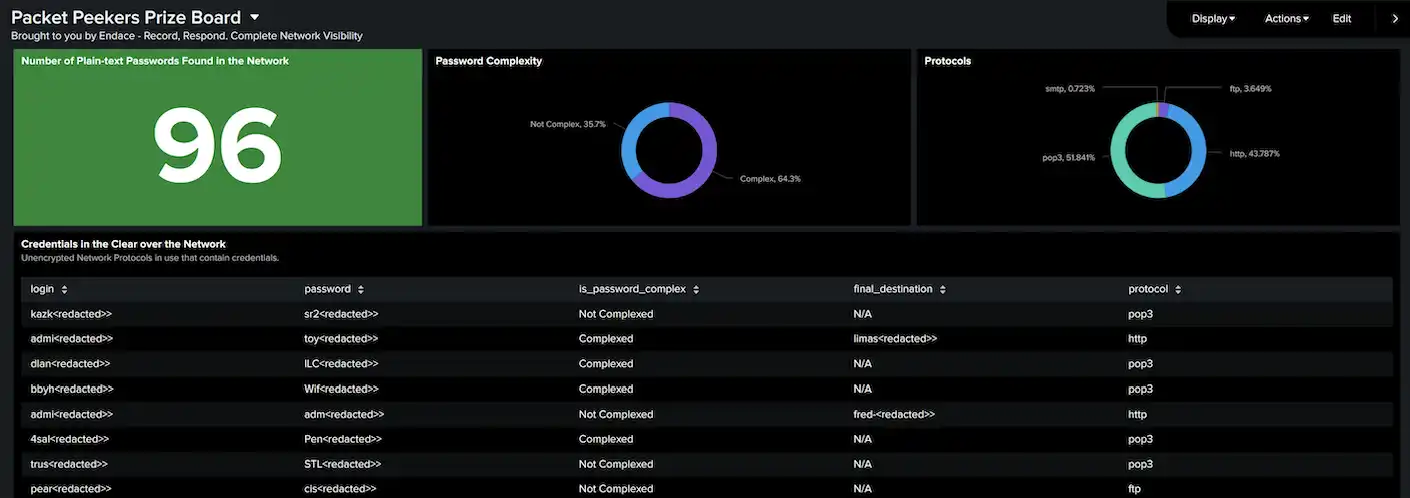
Partnering with Endace and mixing the ability of Splunk Enterprise Safety, we have been in a position to create the ‘Packet Peekers Prize Board’ dashboard to supply a glimpse of all of the unencrypted protocol visitors that contained attendees and exhibiters plain textual content credentials within the community visitors to assist unfold consciousness and encourage using safer protocols for communication through the occasion. The output of those Dashboards will be additional built-in inside SOC workflows through webhooks and different automation playbooks similar to in Splunk SOAR, together with biking the findings again into XDR worklogs or non-public incident communication channels. That is the trendy SOC.
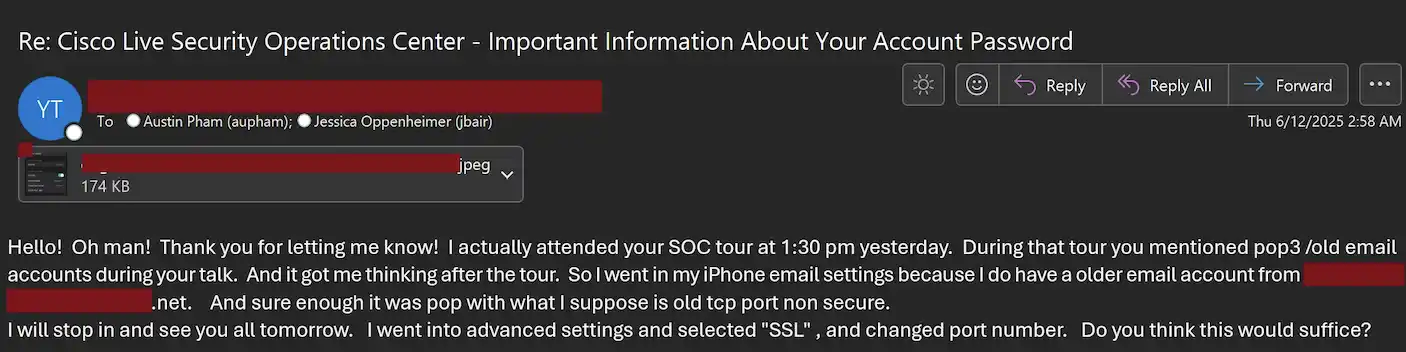
To hold the momentum ahead and drive buyer outcomes with regard of continued success, we reached out to the attendees, contractors, and exhibitors that have been impacted, to tell them and make them conscious of the invention, which we acquired overwhelmingly constructive suggestions from. The outreach was automated through python scripting, which might simply be made right into a Splunk SOAR playbook to execute with a push of a button.
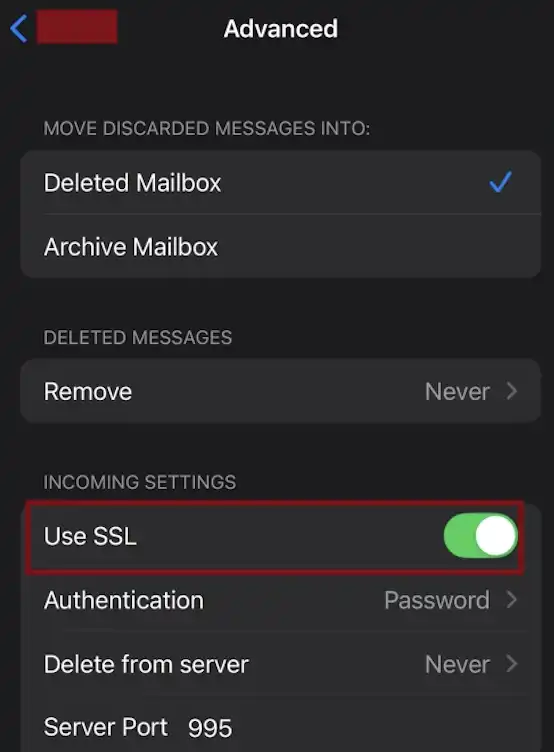
An instance of an answer we’d recommend to clients and attendees alike is so simple as the next setting change:
The Splunk staff is happy to proceed the collaboration with our Cisco Safety counterparts, to safe Cisco Stay and different occasions from attackers.
Need to be taught extra abut what we noticed at Cisco Stay San Diego 2025? Take a look at our foremost weblog publish — Cisco Stay San Diego 2025 SOC — and the remainder of our Cisco Stay SOC content material.
We’d love to listen to what you assume! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media
Share:


