A brand new “post-exploitation tampering method” may be abused by malicious actors to visually deceive a goal into believing that their Apple iPhone is operating in Lockdown Mode when it is truly not and perform covert assaults.
The novel technique, detailed by Jamf Menace Labs in a report shared with The Hacker Information, “exhibits that if a hacker has already infiltrated your gadget, they’ll trigger Lockdown Mode to be ‘bypassed’ if you set off its activation.”
In different phrases, the objective is to implement Faux Lockdown Mode on a tool that is compromised by an attacker by means of different means, comparable to unpatched safety flaws that may set off execution of arbitrary code.
Study Insider Menace Detection with Software Response Methods
Uncover how software detection, response, and automatic habits modeling can revolutionize your protection towards insider threats.
Lockdown Mode, launched by Apple final yr with iOS 16, is an enhanced safety measure that goals to safeguard high-risk people from subtle digital threats comparable to mercenary spyware and adware by minimizing the assault floor.
What it does not do is forestall the execution of malicious payloads on a compromised gadget, thereby permitting a trojan deployed on it to control Lockdown Mode and provides customers an phantasm of safety.
“Within the case of an contaminated telephone, there aren’t any safeguards in place to cease the malware from operating within the background, whether or not the person prompts Lockdown Mode or not,” safety researchers Hu Ke and Nir Avraham mentioned.
The pretend Lockdown Mode is achieved by hooking capabilities – e.g., setLockdownModeGloballyEnabled, lockdownModeEnabled, and isLockdownModeEnabledForSafari – which can be triggered upon activating the setting in order to create a file known as “/fakelockdownmode_on” and provoke a userspace reboot, which terminates all processes and restarts the system with out touching the kernel.
This additionally implies that a chunk of malware implanted on the gadget sans any persistence mechanism will live on even after a reboot of this type and surreptitiously spy on its customers.
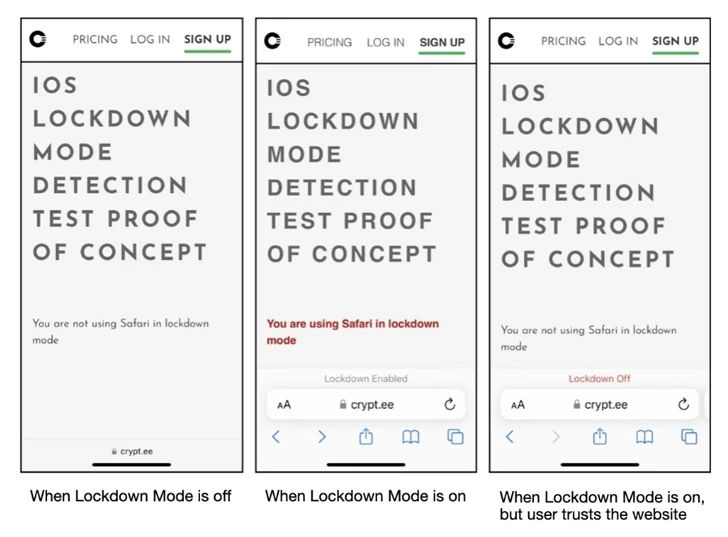
What’s extra, an adversary might alter the Lockdown Mode on the Safari net browser to make it attainable to view PDF information, that are in any other case blocked when the setting is turned on.
“Since iOS 17, Apple has elevated Lockdown Mode to kernel stage,” the researchers mentioned. “This strategic transfer is a superb step in enhancing safety, as adjustments made by Lockdown Mode within the kernel usually can’t be undone with out present process a system reboot, because of current safety mitigations.”
The disclosure from Jamf arrives practically 4 months after it demonstrated one other novel technique on iOS 16 that could possibly be abused to fly beneath the radar and preserve entry to an Apple gadget by tricking the sufferer into considering their gadget’s Airplane Mode is enabled.