The 2025 Cisco Segmentation Report, with 1,000 respondents, was launched final month and has prompted me to assume extra deeply concerning the evolution of the decades-old cybersecurity idea and the way it continues to adapt to fulfill the wants of recent enterprises. I beforehand wrote that whereas 79% of respondents think about segmentation a high precedence, solely 33% implement it absolutely. The survey outcomes additionally revealed fascinating insights into why segmentation stays a foundational idea.
The evolution of segmentation and the event of various segmentation approaches make the idea perfect for implementing a proactive strategy to enterprise cybersecurity as we speak. For years, organizations have utilized macro-segmentation to divide networks into smaller sections, which helps restrict the unfold of profitable assaults whereas enhancing general resilience. And now, augmenting macro-segmentation with micro-segmentation implementations permits safety groups to separate environments into separate networks AND isolate particular workloads primarily based on conduct or identification. This twin segmentation strategy is well-suited to guard as we speak’s distributed, cloud-first community infrastructure and the purposes, information, and customers that depend on these important networks.
That is the primary a part of a three-part collection that delves deeper into the survey outcomes and what they reveal concerning the present state of segmentation.
Macro-Segmentation (On It’s Personal) Is Not Sufficient to Meet At present’s Cybersecurity Challenges
Macro-segmentation alone is inadequate on account of current modifications in fashionable software structure. Fashionable purposes are not monolithic, and they’re not constrained by a subnet or VLAN. Consequently, these purposes are decentralized and composed of a number of workloads. This new decentralized structure has boosted software efficiency, scalability, maintainability, and reliability; nevertheless, it has made it difficult to know what’s taking place on the workload degree.
Nonetheless, the dearth of visibility and management on the workload degree makes conventional safety approaches (together with macro-segmentation) difficult. It’s no marvel that cybersecurity groups are struggling to guard as we speak’s extremely distributed, cloud-first digital infrastructures.
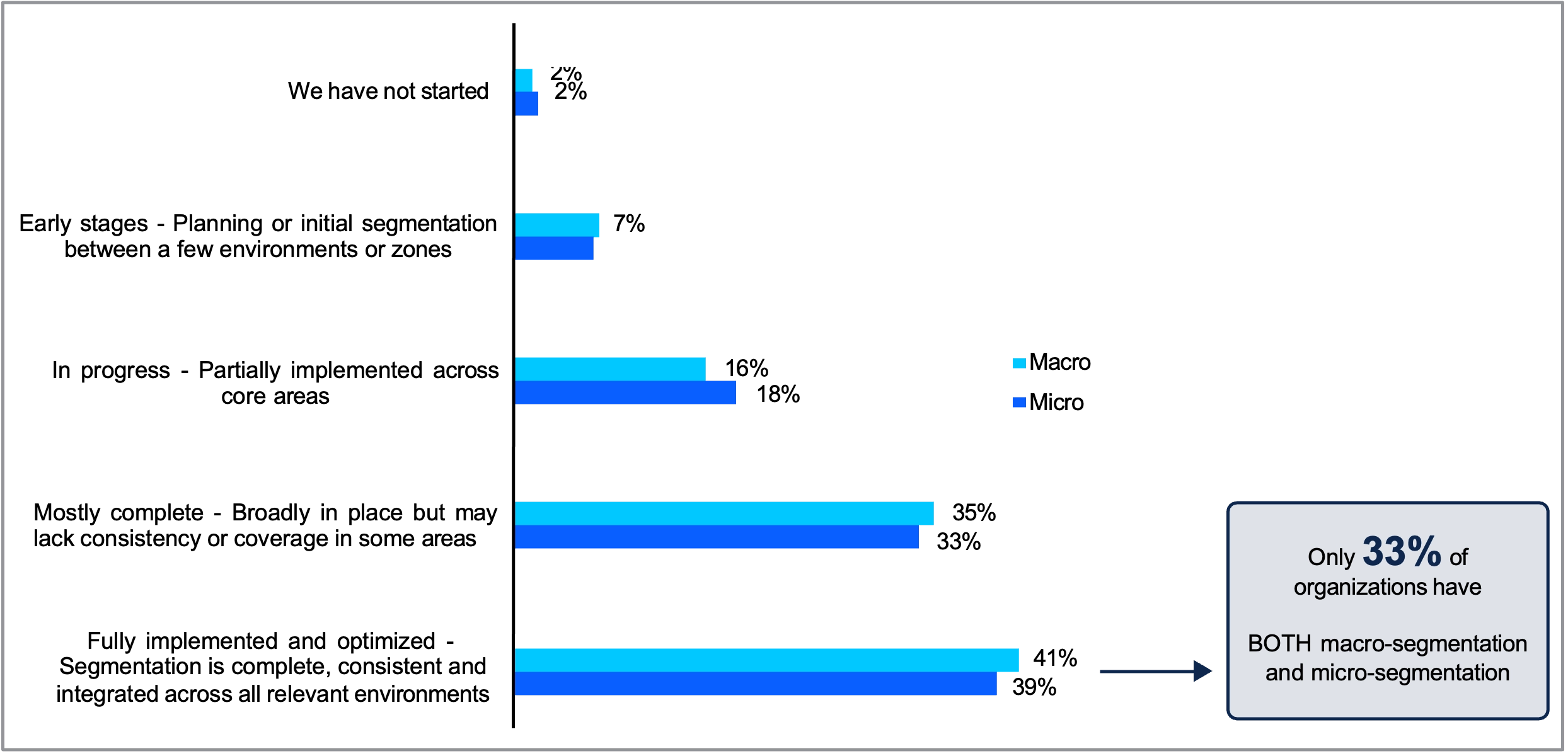
Organizations Have to Implement Macro-Segmentation and Micro-Segmentation in Tandem
Augmenting macro-segmentation with micro-segmentation implementations permits safety groups to separate IT environments into sections whereas isolating particular person workloads primarily based on their conduct or identification. This allows a proactive strategy to cybersecurity, leading to sooner restoration occasions, improved operations, and constant enforcement of segmentation insurance policies.
1. Faster Restoration Occasions
Respondents from organizations which have absolutely applied each macro- and micro-segmentation report that breach containment and restoration take a median of 20 days to finish. In distinction, respondents from organizations that haven’t absolutely applied each macro- and micro-segmentation report that restoration takes them a median of 29 days.
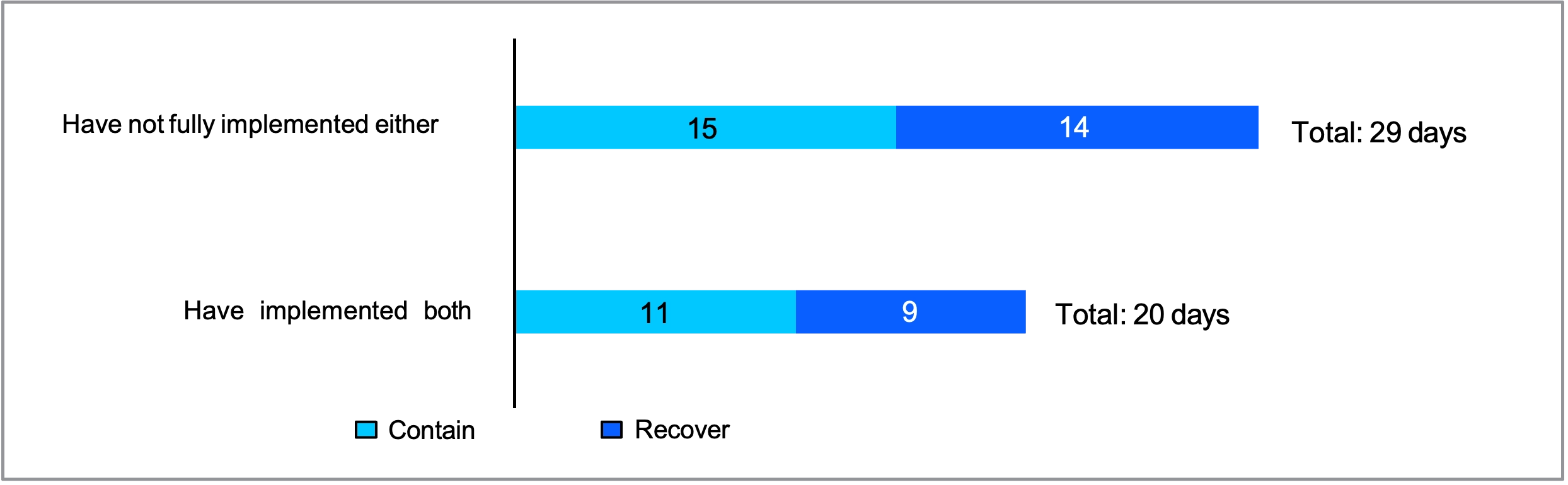
This can be a huge, huge deal. Reducing restoration time by one-third limits the breach’s impression and prevents its future unfold. Simply think about the injury that risk actors can inflict in these further 9 days. The mix of macro- and micro-segmentation slows down attackers. It additionally gives defenders with extra visibility and management over particular person workloads, providing insights into the assault chain that allow them to rapidly establish which belongings should be quarantined, taken offline, and recovered.
2. An Alternative to Align Groups
Segmentation tasks require coordination throughout a number of groups with a number of layers of accountability, necessitating full alignment all through the group. For instance, a improvement staff is aware of who created an software, however it could not have visibility into who’s utilizing the appliance or how the appliance is getting used. A failure to coordinate throughout groups can result in over-permissioning—a typical mistake that creates important dangers for organizations.
In accordance with the survey, organizations (typically) depend on three separate groups for implementing and managing segmentation—IT infrastructure or community (87%), Safety/ SecOps (77%), and DevOps/ Cloud Engineering (71%). The method of implementing each macro- and micro-segmentation can enhance alignment between these groups and get rid of a lot of the chance related to over-permissioning. Persevering with with our improvement staff instance, the drive towards segmentation can convey the event staff nearer to these managing and securing the community by establishing a typical vocabulary and shared goals.
Amongst survey respondents at organizations which have absolutely applied each macro- and micro-segmentation, 87% report that their groups are absolutely aligned, in contrast with 52% of these at organizations with out full implementation.

3. Constant Enforcement
In accordance with the report, two-thirds (63%) of respondents at organizations with full implementation strongly agree that automation is essential to scaling and maturing segmentation tasks, versus 50% with out full implementation of each. Automation permits organizations to scale their segmentation insurance policies throughout all the group (or a minimum of the place it is sensible), leading to extra complete and constant enforcement, and finally, stronger safety controls. Organizations that don’t make use of satisfactory automation should manually create and keep insurance policies, which might simply fall behind safety necessities over time.

A Twin Strategy Allows a Proactive Cybersecurity Technique
The power to implement micro-segmentation at scale at the side of macro-segmentation has turn out to be foundational to fashionable enterprise safety methods and the zero-trust safety mannequin. This allows organizations to recuperate extra rapidly, higher align their groups, and implement segmentation extra persistently—together, permitting for a proactive strategy to cybersecurity. Though segmentation is an outdated idea (from an IT perspective, after all), it stays a important element of a proactive enterprise safety strategy—primarily on account of its adaptation for contemporary environments.
In my subsequent weblog, I’ll define the challenges organizations are dealing with as we speak when implementing segmentation tasks. Within the meantime, obtain the 2025 Cisco Segmentation Report to higher perceive the state of segmentation as we speak.
We’d love to listen to what you assume! Ask a query and keep related with Cisco Safety on social media.
Cisco Safety Social Media



