
Russian state hackers have developed their strategies for breaching industrial management methods by adopting living-off-the-land strategies that allow reaching the ultimate stage of the assault faster and with much less sources.
Safety researchers spotlight that the change opens the door to assaults which can be tougher to detect and don’t essentially require subtle malware for industrial management methods (ICS).
Native binary to ship instructions
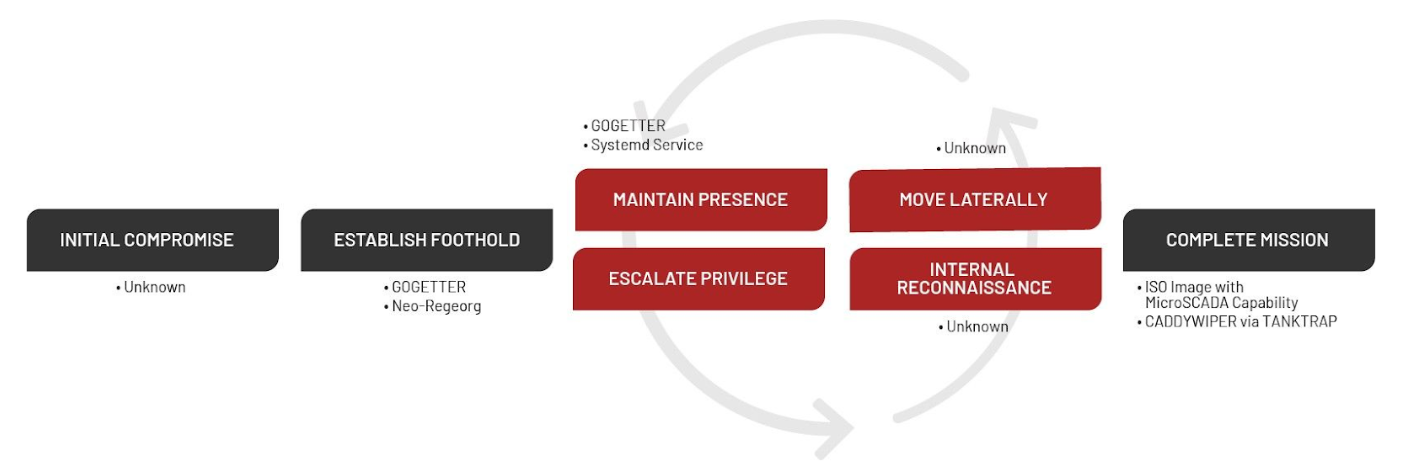
Final yr, the Sandworm risk group breached a Ukrainian crucial infrastructure group in an assault that required lower than 4 months to succeed in the ultimate part, an influence outage that was doubled by missile strikes on crucial amenities throughout the nation.
Sandworm is a hacker group energetic since at the least 2009 and linked to Russia’s Normal Workers Predominant Intelligence Directorate (GRU). It’s centered on focusing on industrial management methods (ICS) and engages in espionage and harmful cyberattacks.
In late 2022, incident responders at Google-owned Mandiant responded to a disruptive cyberattack in Ukraine, which they attributed to Sandworm, and analyzed the ways, strategies, and procedures.
The researchers decided that Sandworm had began the intrusion since at the least June 2022 and obtained entry to the operational expertise (OT) atmosphere via a hypevisor internet hosting a MicroSCADA server, which allows centralized management and automates operation of the whole energy distribution system.
“Primarily based on proof of lateral motion, the attacker probably had entry to the SCADA system for as much as three months” – Mandiant
Though the preliminary assault vector stays unknown presently, the researchers observe that Sandworm exercise was first noticed in June 2022, with the deployment of the Neo-REGEORG webshell on a server uncovered on the general public web.
After one month, the hackers executed the Golang-based GOGETTER tunneler to proxy encrypted communications for the command and management (C2) server utilizing the Yamux open-source library.
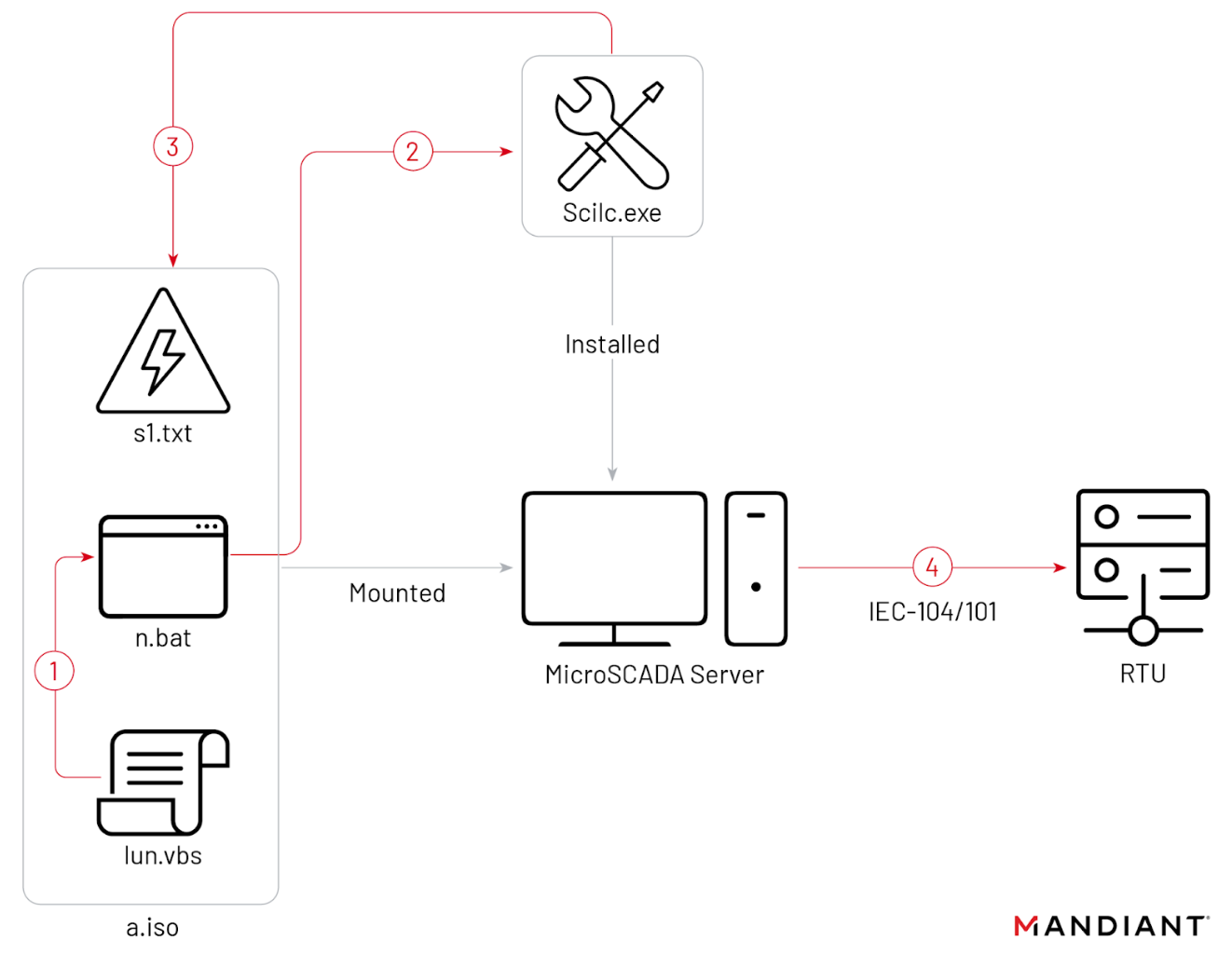
The assault culminated two disruptive occasions. One was an influence outage on October 10, 2022, when Sandworm used an ISO CD-ROM picture file to run the native MicroSCADA utility scilc.exe, prone to run malicious instructions that might swap off the substations.
Loading the ISO picture was attainable as a result of the digital machine MicroSCADA was working on had the autorun function enabled, permitting CD-ROMs, bodily or digital (e.g. an ISO file) to run routinely.
Supply: Mandiant
The scilc.exe utility is a part of the MicroSCADA software program suite and Sandworm used it to run SCIL (a high-level programming language for MicroSCADA) instructions that the server would relay to the distant terminal models (RTU – subject gadgets) within the substation.
In response to the researchers’ findings, the compromised MicroSCADA server was working an end-of-life software program model that allowed default entry to the SCIL-API.
Utilizing a local binary (LoLBin) within the assault signifies the hackers’ shift to living-off-the-land (LoL/LOTL) strategies that depend on extra light-weight and generic instruments, which make risk exercise tougher to detect.
Contained in the ISO file there have been at the least the next three recordsdata:
- “lun.vbs”, which runs n.bat
- “n.bat”, which probably runs the native scilc.exe utility
- “s1.txt”, which probably accommodates the unauthorized MicroSCADA instructions
The researcher discovered that the lun.vbs script had a September 23 timestamp, which means that the hackers had about two months to develop their OT functionality because the preliminary entry stage.
supply: Mandiant
The second disruptive occasion occurred on October 12, 2022, when Sandworm deployed a brand new model of the CADDYWIPER data-destroying malware, probably an effort to additional disrupt the atmosphere and take away traces of the assault.
“Nevertheless, we observe that the wiper deployment was restricted to the sufferer’s IT atmosphere and didn’t impression the hypervisor or the SCADA digital machine” – Mandiant
The researchers observe that this motion was uncommon as a result of the the risk actor had already eliminated different forensic artifacts from the SCADA system. They consider this might level to “a scarcity of coordination throughout totally different people or operational subteams concerned within the assault.”
Clues uncovered in the course of the investigation of the assault point out that the hackers had been prepared for the disruption of the methods at the least three weeks earlier than it occurred.
There isn’t enough proof to assist this idea however the researchers consider that Sandworm could have waited for a selected second to finish the mission.
“The eventual execution of the assault coincided with the beginning of a multi-day set of coordinated missile strikes on crucial infrastructure throughout a number of Ukrainian cities, together with town by which the sufferer was positioned” – Mandiant
Sandworm does not want customized malware
Within the report revealed immediately, Mandiant highlights that the strategies used within the assault “recommend a rising maturity of Russia’s offensive OT arsenal” that interprets into an elevated potential to acknowledge new OT risk vectors, growing new capabilities, and leveraging various kinds of OT infrastructure for his or her assaults.
Mixed with the swap to living-off-the-land strategies, the researchers consider that Sandworm is probably going succesful to hold out assaults in opposition to OT methods from totally different distributors.
Nathan Brubaker, Mandiant head of rising threats and analytics, Google Cloud, informed BleepingComputer that Sandworm’s risk exercise outdoors Ukraine wouldn’t be restricted by its functionality however guided by the motivation to assault.
The researcher says that the novelty on this assault is its agile nature and this could enable Sandworm to assault “different environments extra simply than with some subtle ICS malware.”
Brubaker underlines that Sandworm didn’t use customized malware for the OT a part of the assault however resorted to a LoL binary, which requires OT experience and understanding the focused industrial processes, the expertise used within the assault (MicroSCADA on this case) being much less notable.
“There isn’t a purpose Sandworm couldn’t replicate an analogous kind of assault in one other atmosphere with totally different expertise,” Brubaker concluded.
Mandiant’s report contains indicators of compromise, YARA guidelines, steering to harden SCADA administration hosts, and proposals that will help defenders detect Sandworm’s exercise in ICS environments and mitigate the risk.


