Russian cyber espionage actors affiliated with the Federal Safety Service (FSB) have been noticed utilizing a USB propagating worm referred to as LitterDrifter in assaults concentrating on Ukrainian entities.
Examine Level, which detailed Gamaredon’s (aka Aqua Blizzard, Iron Tilden, Primitive Bear, Shuckworm, and Winterflounder) newest techniques, branded the group as partaking in large-scale campaigns which can be adopted by “knowledge assortment efforts aimed toward particular targets, whose choice is probably going motivated by espionage objectives.”
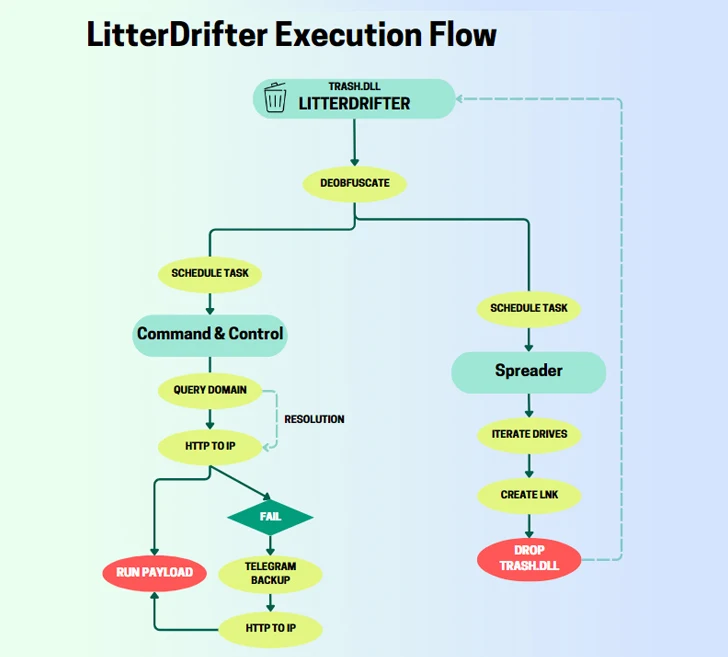
The LitterDrifter worm packs in two major options: routinely spreading the malware through linked USB drives in addition to speaking with the risk actor’s command-and-control (C&C) servers. It is also suspected to be an evolution of a PowerShell-based USB worm that was beforehand disclosed by Symantec in June 2023.
Written in VBS, the spreader module is chargeable for distributing the worm as a hidden file in a USB drive along with a decoy LNK that is assigned random names. The malware will get its identify LitterDrifter owing to the truth that the preliminary orchestration part is called “trash.dll.”
“Gamaredon’s method in direction of the C&C is relatively distinctive, because it makes use of domains as a placeholder for the circulating IP addresses truly used as C2 servers,” Examine Level defined.
LitterDrifter can be able to connecting to a C&C server extracted from a Telegram channel, a tactic it has repeatedly put to make use of since no less than the beginning of the yr.
The cybersecurity agency stated it additionally detected indicators of attainable an infection outdoors of Ukraine based mostly on VirusTotal submissions from the U.S., Vietnam, Chile, Poland, Germany, and Hong Kong.
Gamaredon has had an lively presence this yr, whereas repeatedly evolving its assault strategies. In July 2023, the adversary’s speedy knowledge exfiltration capabilities got here to mild, what with the risk actor transmitting delicate info inside an hour of the preliminary compromise.
“It is clear that LitterDrifter was designed to help a large-scale assortment operation,” the corporate concluded. “It leverages easy, but efficient methods to make sure it could actually attain the widest attainable set of targets within the area.”
The event comes as Ukraine’s Nationwide Cybersecurity Coordination Heart (NCSCC) revealed assaults orchestrated by Russian state-sponsored hackers concentrating on embassies throughout Europe, together with Italy, Greece, Romania, and Azerbaijan.
The intrusions, attributed to APT29 (aka BlueBravo, Cloaked Ursa, Cozy Bear, Iron Hemlock, Midnight Blizzard, and The Dukes), contain the exploitation of the just lately disclosed WinRAR vulnerability (CVE-2023-38831) through benign-looking lures that declare to supply BMWs on the market, a theme it has employed previously.
The assault chain commences with sending victims phishing emails containing a hyperlink to a specifically crafted ZIP file that, when launched, exploits the flaw to retrieve a PowerShell script from a distant server hosted on Ngrok.
“A regarding pattern of exploiting CVE-2023-38831 vulnerability by Russian intelligence companies hacking teams demonstrates its rising recognition and class,” NCSCC stated.
Earlier this week, the Laptop Emergency Response Staff of Ukraine (CERT-UA) unearthed a phishing marketing campaign that propagates malicious RAR archives that masquerades as a PDF doc from the Safety Service of Ukraine (SBU) however, in actuality, is an executable that results in the deployment of Remcos RAT.
CERT-UA is monitoring the exercise underneath the moniker UAC-0050, which was additionally linked to a different spate of cyber assaults aimed toward state authorities within the nation to ship Remcos RAT in February 2023.