Excessive-profile authorities and telecom entities in Asia have been focused as a part of an ongoing marketing campaign since 2021 that is designed to deploy fundamental backdoors and loaders for delivering next-stage malware.
Cybersecurity firm Examine Level is monitoring the exercise beneath the title Stayin’ Alive. Targets embrace organizations situated in Vietnam, Uzbekistan, Pakistan, and Kazakhstan.
“The simplistic nature of the instruments […] and their vast variation suggests they’re disposable, largely utilized to obtain and run further payloads,” it stated in a report revealed Wednesday. “These instruments share no clear code overlaps with merchandise created by any recognized actors and would not have a lot in widespread with one another.”
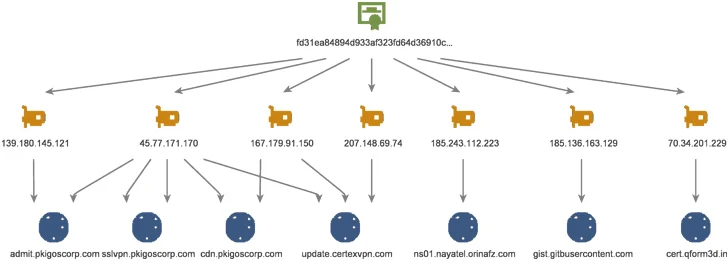
What’s notable concerning the marketing campaign is that the infrastructure shares overlaps with that utilized by ToddyCat, a China-linked menace actor recognized for orchestrating cyber assaults towards authorities and army businesses in Europe and Asia since a minimum of December 2020.
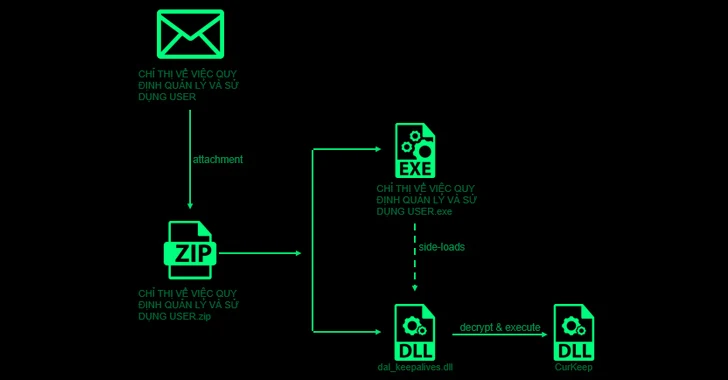
Assault chains start with a spear-phishing e mail that accommodates a ZIP file attachment with a reputable executable that leverages DLL side-loading to load a backdoor referred to as CurKeep via a rogue DLL dal_keepalives.dll current inside the archive.
CurlKeep is designed to ship details about the compromised host to a distant server, execute instructions despatched by the server, and write server responses to a file on the system.
A more in-depth examination of the command-and-control (C2) infrastructure has revealed a consistently evolving arsenal of loader variants dubbed CurLu, CurCore, and CurLog which might be able to receiving DLL recordsdata, executing distant instructions, and launch a course of related to a newly generated file to which knowledge from the server is written to.
Additionally found is a passive implant named StylerServ that listens on 5 totally different ports (60810, 60811, 60812, 60813, and 60814) to just accept a distant connection and obtain an encrypted configuration file.
Whereas there isn’t any conclusive proof to attach Stayin’ Alive to ToddyCat, the findings present that each intrusion units make the most of the identical infrastructure to go after the same set of targets.
“Using disposable loaders and downloaders, as noticed on this marketing campaign, is turning into extra widespread even amongst subtle actors,” it stated. “Using disposable instruments makes each detection and attribution efforts tougher, as they’re changed usually, and probably written from scratch.”