New findings have recognized connections between an Android adware known as DragonEgg and one other refined modular iOS surveillanceware device named LightSpy.
DragonEgg, alongside WyrmSpy (aka AndroidControl), was first disclosed by Lookout in July 2023 as a pressure of malware able to gathering delicate knowledge from Android gadgets. It was attributed to the Chinese language nation-state group APT41.
However, particulars about LightSpy got here to gentle in March 2020 as a part of a marketing campaign dubbed Operation Poisoned Information during which Apple iPhone customers in Hong Kong have been focused with watering gap assaults to put in the adware.
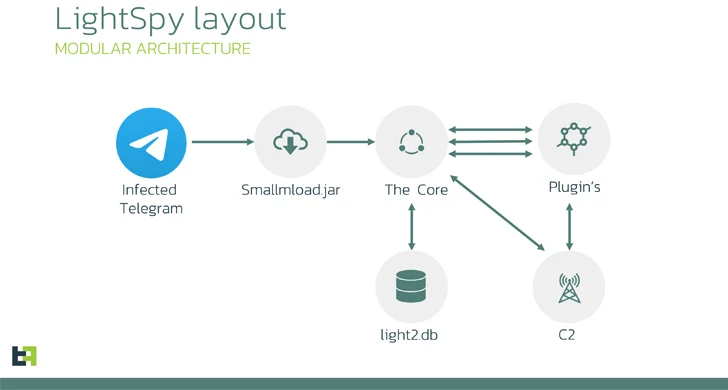
Now, in accordance with Dutch cell safety agency ThreatFabric, the assault chains contain using a trojanized Telegram app that is designed to obtain a second-stage payload (smallmload.jar), which, in flip, is configured to obtain a 3rd element codenamed Core.
Additional evaluation of the artifacts has revealed that the implant has been actively maintained since at the least December 11, 2018, with the most recent model launched on July 13, 2023.
The core module of LightSpy (i.e., DragonEgg) capabilities as an orchestrator plugin accountable for gathering the machine fingerprint, establishing contact with a distant server, awaiting additional directions, and updating itself in addition to the plugins.
“LightSpy Core is extraordinarily versatile when it comes to configuration: operators can exactly management the adware utilizing the updatable configuration,” ThreatFabric mentioned, noting that WebSocket is used for command supply and HTTPS is used for knowledge exfiltration.
Among the notable plugins embody a locationmodule that tracks victims’ exact places, soundrecord that may seize ambient audio in addition to from WeChat VOIP audio conversations, and a invoice module to collect cost historical past from WeChat Pay.
LightSpy’s command-and-control (C2) contains a number of servers positioned in Mainland China, Hong Kong, Taiwan, Singapore, and Russia, with the malware and WyrmSpy sharing the identical infrastructure.
ThreatFabric mentioned it additionally recognized a server internet hosting knowledge from 13 distinctive cellphone numbers belonging to Chinese language mobile phone operators, elevating the chance that the information both represents the testing numbers of LightSpy builders or victims’.
The hyperlinks between DragonEgg and LightSpy stem from similarities in configuration patterns, runtime construction and plugins, and the C2 communication format.
“The way in which the risk actor group distributed the preliminary malicious stage inside widespread messenger was a intelligent trick,” the corporate mentioned.
“There have been a number of advantages of that: the implant inherited all of the entry permissions that the service utility had. Within the case of messenger, there have been a number of personal permissions corresponding to digital camera and storage entry.”